
In the high-stakes arena of digital transformation, security has eclipsed aesthetics and speed as the defining metric for web application quality. Cyber threats, growing in sophistication, have elevated protection from a technical footnote to a boardroom imperative. The worldwide average cost of a data breach dipped to $4.44 million in 2025, down 9% from $4.88 million the prior year, yet the financial and reputational toll remains staggering, as detailed in IBM’s Cost of a Data Breach Report 2025 .
Philadelphia’s tech firms exemplify this shift, where providers like OpenSource Technologies integrate safeguards from inception. “The key determinant of quality in web application development services is no longer its design or its speedy performance, but its impenetrable security,” writes Chris Bates in NorthPennNow . Traditional bolt-on defenses prove inadequate against evolving attacks, demanding a proactive ‘Security by Design’ ethos.
Threat Evolution Reshapes Priorities
Attackers exploit vulnerabilities like SQL injection and cross-site scripting (XSS) with AI-enhanced precision, targeting APIs and cloud-native stacks. OWASP’s Top 10 for 2025 lists Broken Access Control as the foremost risk, followed by Security Misconfiguration and Software Supply Chain Failures, per TryHackMe on X . Developers must now anticipate these in every commit, as rapid deployment cycles amplify exposure.
DevSecOps emerges as the antidote, embedding security into CI/CD pipelines via ‘shift-left’ practices. This continuous testing catches flaws early, slashing remediation costs. Yehuda Raz notes in Security Boulevard that OWASP ASVS provides structured benchmarks, from opportunistic Level 1 controls for low-risk apps to advanced Level 3 for critical infrastructure.
In 2026, AI dual-role intensifies: attackers craft adaptive phishing, while defenders leverage it for anomaly detection. Novas Arc highlights in its trends report that “integrating generative AI features into production applications expands the application attack surface,” urging OWASP adherence and zero-trust enforcement.
DevSecOps: The New Development Standard
Teams adopting DevSecOps integrate static application security testing (SAST) and software composition analysis (SCA) into workflows, prioritizing exploitable flaws. SANS Institute’s SEC522 course emphasizes securing Infrastructure as Code (IaC) against misconfigurations, a top OWASP risk, through hands-on labs on OWASP Top 10 defenses.
Dependency management proves pivotal; a vulnerable open-source package can unravel secure code. “A single vulnerable third-party package can compromise an otherwise secure application,” warns Techloy . Tools like Snyk generate Software Bills of Materials (SBOMs) for transparency, essential for compliance and rapid patching.
Encryption anchors data defense: TLS 1.3 for transit, AES-256 at rest, and HTTPS enforcement. NorthPennNow stresses database encryption and hashing, extending to APIs via schema validation and rate limiting to thwart abuse.
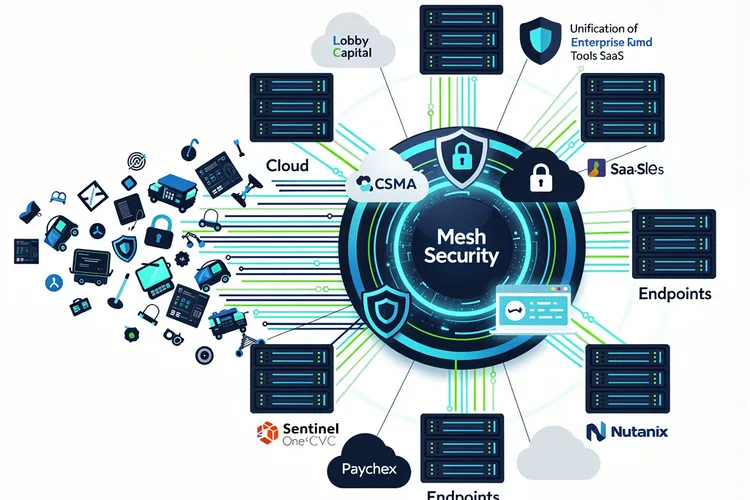
Zero Trust and API Fortification
Zero Trust Application Access (ZTAA) verifies every request, decoupling from networks. Novas Arc cites Cisco’s success: “Application access was decoupled from the network, improving security.” OAuth 2.1 and OpenID Connect, backed by providers like Auth0, enforce MFA and scoped tokens, mitigating 95% of API breaches reported by Techloy.
Web Application Firewalls (WAFs) and Runtime Application Self-Protection (RASP) block OWASP threats in real-time. Cloudflare advocates DDoS mitigation and bot management, noting shadow APIs as hidden risks where “development teams work quickly… without informing security teams.” Unified WAAP platforms consolidate defenses amid cloud sprawl.
Mobile endpoints demand device attestation and secure enclaves, as 2026 trends per Novas Arc extend app security to tampered hardware.
Open-Source Edge and Vendor Scrutiny
Open-source frameworks, vetted by global communities, outpace proprietary in patching speed when tracked via SBOMs. Bates affirms their strategic value for Philadelphia developers, provided meticulous management.
Procuring services requires grilling vendors on ASVS levels and DevSecOps maturity. Raz recommends evidence trails—test results, remediation logs—for audits. X users like @alexcooldev echo: “Escape & sanitize user input to prevent XSS… Implement JWT/OAuth + RBAC,” underscoring practical checklists.
Post-launch vigilance—monitoring, patching, logging—sustains resilience. SANS labs teach defending external inputs from browsers and services, including AI components.
2026 Imperatives for Resilience
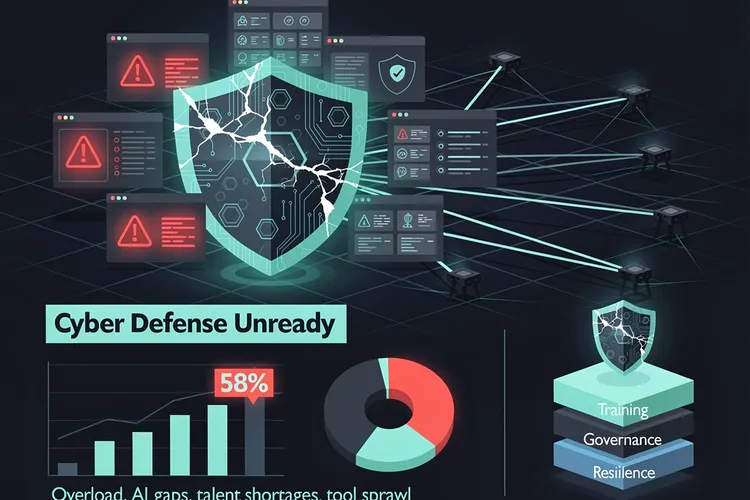
“In 2026 and beyond, successful application security relies on treating security as a core engineering discipline, rather than an afterthought,” per Techloy. AI governance curbs shadow AI risks, adding $670,000 to breaches without controls, IBM reports.
Organizations automating security save $1.9 million per incident, trimming lifecycles by 80 days. As threats like injection and cryptographic failures persist, OWASP ASVS and Top 10 guide maturity. Bates concludes: “Delivering secure, scalable, and future-ready applications is a core responsibility, not an afterthought.”
Insiders must champion shift-left, zero-trust, and continuous verification to outpace adversaries in this arms race.









Leave a Reply
Your email address will not be published.