
Fortinet has unveiled a comprehensive overhaul of its FortiCNAPP platform, positioning the cybersecurity giant to compete more aggressively in the rapidly consolidating cloud-native application protection market. The enhancements, which integrate cloud security posture management with advanced data protection capabilities, represent a strategic pivot toward unified security platforms as enterprises grapple with increasingly complex multi-cloud environments.
According to Yahoo Finance , the upgraded FortiCNAPP platform now delivers integrated cloud security posture management (CSPM), cloud workload protection platform (CWPP), and cloud infrastructure entitlement management (CIEM) capabilities within a single console. This consolidation addresses a persistent pain point for security teams managing disparate tools across Amazon Web Services, Microsoft Azure, and Google Cloud Platform deployments.
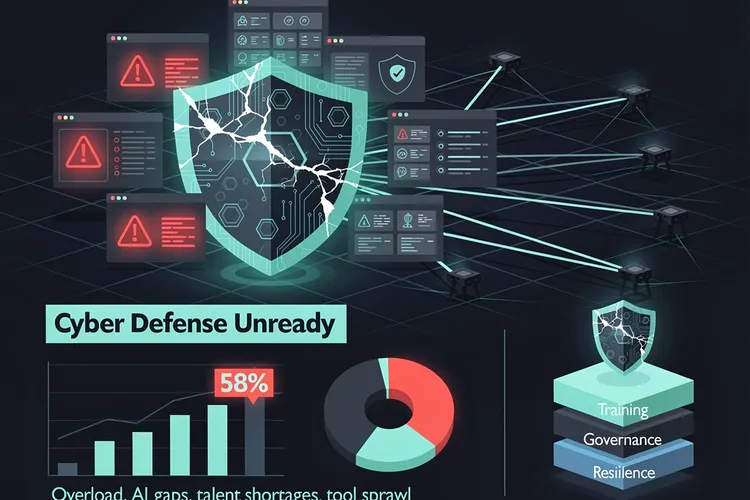
The timing of Fortinet’s expansion reflects broader industry dynamics where fragmented security tooling has created operational inefficiencies and visibility gaps. Enterprise security teams currently juggle an average of 45 different security tools, according to recent industry surveys, creating alert fatigue and delayed threat response times. Fortinet’s unified approach attempts to reduce this complexity while maintaining the depth of protection required for modern cloud-native applications.
Market Positioning Against Established Cloud Security Specialists
Fortinet’s enhanced FortiCNAPP enters a competitive arena dominated by specialists including Palo Alto Networks’ Prisma Cloud, Wiz, and Orca Security. The company’s differentiation strategy centers on leveraging its existing enterprise customer base and integrated security fabric architecture, which already connects network security, endpoint protection, and security operations center tools under a unified management framework.
The platform’s new capabilities include runtime protection for containers and serverless functions, automated compliance monitoring across regulatory frameworks, and AI-powered threat detection that correlates cloud security events with broader network activity. These features address the shift toward DevSecOps practices, where security must integrate seamlessly into continuous integration and continuous deployment pipelines without impeding developer velocity.
Industry analysts note that Fortinet’s broad security portfolio provides both advantages and challenges in the cloud security market. While the company can offer integrated protection across hybrid environments, pure-play cloud security vendors often demonstrate deeper expertise in cloud-native architectures and faster innovation cycles. The success of FortiCNAPP will likely depend on Fortinet’s ability to match specialist capabilities while delivering on its integration promises.
Technical Innovations Addressing Modern Cloud Threats
The expanded FortiCNAPP platform introduces several technical innovations designed to address emerging cloud security challenges. The system now provides agentless scanning capabilities that discover and assess cloud resources without requiring software installation, reducing deployment friction and eliminating blind spots created by unmanaged assets. This approach has become increasingly important as infrastructure-as-code practices proliferate, creating ephemeral resources that traditional agent-based solutions struggle to protect.
Data security receives particular emphasis in the updated platform, with new data classification and loss prevention features that automatically identify sensitive information across cloud storage services, databases, and data warehouses. The system applies machine learning algorithms to detect unusual data access patterns and potential exfiltration attempts, addressing one of the most significant risks in cloud environments where data often flows freely between services and regions.
The platform’s threat detection capabilities now incorporate behavioral analysis that establishes baseline activity patterns for cloud workloads and flags deviations indicative of compromise. This approach proves particularly valuable for detecting sophisticated attacks that evade signature-based detection, such as living-off-the-land techniques where attackers abuse legitimate cloud services and credentials to maintain persistence and move laterally through environments.
Compliance Automation As Competitive Differentiator
Regulatory compliance has emerged as a critical driver for cloud security investments, and Fortinet has enhanced FortiCNAPP with automated compliance monitoring and remediation capabilities spanning major frameworks including SOC 2, PCI DSS, HIPAA, and GDPR. The platform continuously assesses cloud configurations against these standards and provides prioritized remediation guidance, reducing the manual effort required to maintain compliance across dynamic cloud environments.
The compliance features extend beyond basic configuration checks to include evidence collection and audit trail generation, addressing the documentation requirements that consume significant security team resources during regulatory assessments. Organizations can generate compliance reports on-demand and track remediation progress over time, providing visibility that supports both operational security improvements and board-level risk management discussions.
This compliance focus aligns with broader market trends where regulatory requirements increasingly drive security technology adoption. The proliferation of data protection regulations globally has created complex compliance obligations for multinational organizations, making automated compliance monitoring a valuable differentiator in crowded security markets.
Integration Strategy Leverages Existing Security Fabric
Fortinet’s integration strategy represents a key element of its cloud security expansion, connecting FortiCNAPP with the company’s broader Security Fabric architecture. This integration enables correlation of cloud security events with network traffic analysis, endpoint detection and response telemetry, and security information and event management data, providing comprehensive visibility across hybrid environments.
The unified approach addresses a significant challenge facing security operations centers, where analysts struggle to connect events across disconnected security tools and identify sophisticated attacks that span multiple infrastructure layers. By centralizing security data and applying cross-platform analytics, FortiCNAPP aims to reduce mean time to detection and enable faster, more informed incident response decisions.
However, this integration strategy also creates vendor lock-in considerations for potential customers. Organizations must weigh the operational benefits of unified platforms against the flexibility of best-of-breed approaches that allow mixing specialized tools from multiple vendors. The decision often hinges on organizational maturity, available security resources, and specific risk profiles.
Pricing and Deployment Models Target Enterprise Buyers
Fortinet has structured FortiCNAPP pricing to appeal to enterprise buyers seeking predictable costs and flexible deployment options. The platform offers consumption-based pricing that scales with cloud resource usage, addressing a common concern where fixed licensing models create cost overruns as cloud footprints expand. This approach aligns pricing with actual security needs while providing budget predictability through committed use discounts.
The deployment model supports both software-as-a-service delivery and private cloud installations for organizations with data sovereignty requirements or regulatory restrictions on third-party data processing. This flexibility proves particularly important in regulated industries including financial services and healthcare, where security tool deployments must accommodate strict data handling requirements.
Channel partners receive enhanced margins and technical support for FortiCNAPP sales, reflecting Fortinet’s continued reliance on indirect sales channels for enterprise customer acquisition. The company has developed specialized training programs and technical certifications to ensure partners can effectively position and deploy the expanded platform, recognizing that complex cloud security solutions require significant implementation expertise.
Market Implications and Competitive Response
Fortinet’s aggressive expansion into comprehensive cloud security capabilities signals intensifying competition in a market projected to exceed $20 billion by 2027. The move pressures both established security vendors and venture-backed startups to accelerate innovation and potentially pursue consolidation to match the breadth of integrated platforms. Industry observers anticipate increased merger and acquisition activity as vendors seek to fill capability gaps and achieve the scale necessary to compete against comprehensive platforms.
The competitive response from market leaders will likely focus on deepening cloud-native capabilities and expanding platform integrations. Palo Alto Networks, CrowdStrike, and Microsoft have all made significant cloud security investments through acquisitions and organic development, creating a dynamic market where continuous innovation determines competitive positioning. Smaller specialist vendors may increasingly target specific use cases or vertical markets where deep expertise provides defensible differentiation.
For enterprise buyers, the expansion of comprehensive cloud security platforms creates both opportunities and challenges. Organizations gain access to more integrated solutions that promise operational efficiency and improved security outcomes, but must carefully evaluate vendor claims against actual capabilities and implementation requirements. The complexity of cloud security demands rigorous proof-of-concept testing and reference checking to ensure platforms deliver on their integration and automation promises in production environments.









Leave a Reply
Your email address will not be published.