
In the high-stakes arena of data defense, information security—known as InfoSec—stands as the encompassing guardian of all data forms, digital and physical alike, while cybersecurity zeroes in on digital fortification. The National Institute of Standards and Technology (NIST) delineates InfoSec as the “protection of information and information systems from unauthorized access, use, disclosure, disruption, modification or destruction,” rendering it synonymous with IT and information systems security. Cybersecurity, by contrast, NIST frames as safeguarding “computers and electronic communications systems, including the digital information stored in these systems and devices.” This distinction sharpens as threats evolve, with Forbes Advisor noting, “Information security takes this broader view, ensuring data protection and integrity whether the information in question is stored in the cloud, on a backup disc, on paper or even in a person’s mind.”
Cybersecurity operates as a vital subset, laser-focused on repelling online incursions like malware and phishing through tools such as firewalls and intrusion detection systems. Yet InfoSec extends to physical safeguards—locked filing cabinets, surveillance, and access controls—ensuring the CIA triad’s pillars endure across mediums. As Coursera explains, InfoSec deploys “policies, processes, and controls organizations use to protect all their information from unauthorized access, alteration, or loss,” underpinning confidentiality, integrity, and availability.
The overlap is profound: both fields wield the CIA triad as their bedrock. Confidentiality bars unauthorized eyes via encryption and access limits; integrity preserves data accuracy against tampering with checksums and signatures; availability guarantees timely access through redundancies and recovery plans. TechTarget underscores its timeless role: “Confidentiality, integrity and availability are considered the three most important concepts in infosec.”
Triad’s Enduring Pillars Under Siege
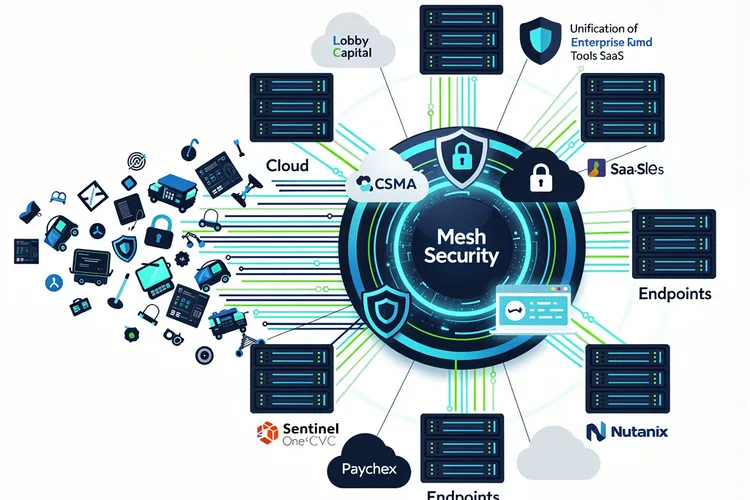
InfoSec’s breadth shines in specialized domains: cloud security shields virtual stores, network security barricades infrastructure, application security patches software flaws, physical security guards tangible assets, and incident response orchestrates breach countermeasures. Cybersecurity dovetails here but skips non-digital realms, as SecurityScorecard clarifies: “Cybersecurity focuses on protecting data found in a digital format from being compromised and attacked… Unlike cybersecurity, information security extends beyond digital concerns, addressing the security landscape in its entirety.”
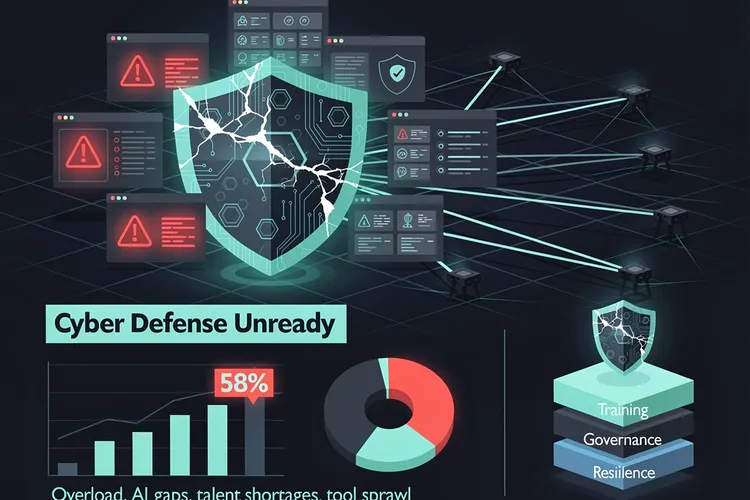
Threats pierce both shields with escalating ferocity. Phishing and social engineering, now AI-enhanced for hyper-realism, snag credentials; malware and ransomware encrypt or corrupt; breaches pilfer secrets; insiders betray trust. The World Economic Forum’s Global Cybersecurity Outlook 2026 reveals CEOs pegging cyber-enabled fraud as paramount, with 73% impacted personally in 2025, while CISOs fret ransomware persistence.
AI ignites the powder keg: 94% of executives foresee it reshaping defenses, yet 87% flag AI vulnerabilities as the swiftest-rising peril. WEF notes, “AI is anticipated to be the most significant driver of change in cybersecurity in the year ahead.”
AI’s Double-Edged Onslaught
Remote work amplifies exposures—home networks lack corporate rigor—while skill voids persist, with 3.5 million global vacancies lingering into 2026 per Cybersecurity Ventures . Trend Micro’s 2026 forecast warns of “AI-fication,” where agentic AI automates ransomware reconnaissance to extortion, as researcher Numaan Huq cautions: “Vibe coding is a double-edged sword… deploying vibe-coded modules into production software… carries significant risk.” Geopolitics fuels targeted strikes, with 64% bracing for infrastructure sabotage.
Careers thrive amid demand: InfoSec analysts monitor breaches at a median $120,360 salary (BLS 2023 via Forbes ); ethical hackers probe flaws; architects blueprint defenses; compliance officers align with regs like GDPR. Cybersecurity mirrors with penetration testers and SOC analysts, but InfoSec’s governance edge suits CISOs, whose ranks hit 32,000 globally.
Tools arm the fight: firewalls repel, IDS/IPS detect/block, DLP stems leaks, SIEM correlates events. Yet as Trend Micro predicts, “Ransomware will become increasingly autonomous, using AI to automate exploitation, data analysis, and negotiation.”
Career Arenas and Tool Arsenals
Global spending surges to $522 billion in 2026 ( Cybersecurity Ventures ), yet gaps yawn: 68% lack cloud experts, 37% penetration testers. Projections show 32% U.S. analyst growth by 2032, near-zero unemployment for veterans. Women eye 30% workforce share by 2025.
InfoSec’s holistic vigilance—blending CIA across realms—positions it as indispensable amid 2026’s AI-fueled chaos, where digital alone falters. As threats morph, mastering this expanse defines resilience.









Leave a Reply
Your email address will not be published.