
As the Milano Cortina 2026 Winter Olympics approach, set for February 6-22 across northern Italy’s Alpine regions, enterprise IT leaders face a surge of cyber vulnerabilities. Organizations supporting the Games—from suppliers to sponsors—must fortify defenses against bad actors eyeing the event’s massive visibility. Drawing from Paris 2024’s over 140 incidents, including 22 system breaches, experts warn of amplified risks amid geopolitical tensions and AI enhancements.
Kristopher Russo, principal threat researcher at IT Brew , highlighted motives: “The idea is really to both embarrass the hosts and the host countries of the game, show unpreparedness, get everybody on edge, and then also to push these individual ideologies and viewpoints to get that into the open… The bad guys really like these huge events like [the] Olympics because they have a lot of coverage built in right now.” France’s ANSSI aided nearly 500 companies during Paris, per the same report.
With three billion viewers expected, the event spans Milan, Cortina d’Ampezzo, Valtellina, and Val di Fiemme, creating a sprawling digital ecosystem ripe for exploitation.
Historical Attacks Set Grim Precedent
Past Games reveal patterns: PyeongChang 2018 saw WiFi disruptions; Tokyo 2021 faced Russian sabotage attempts; Paris 2024 endured DDoS spikes and phishing surges, as detailed in Palo Alto Networks Unit 42 analysis. Ransomware, phishing via business email compromise (BEC), and credential stuffing loom large, with 76% of phishing succeeding through BEC.
Italy’s National Cybersecurity Agency (ACN), formed in 2021, views Milano Cortina as its trial by fire. Rear Adm. Gianluca Galasso, ACN operations head, told Reuters : “The Olympics are a global event. We expect around three billion viewers and another one and a half million spectators with tickets. That visibility can attract criminal interests.” Around 20 specialists monitor dark web chatter from Rome, with 10 more joining Milan’s Technology Operations Centre (TOC) alongside Deloitte and partners.
ACN’s January 2025 MoU with Fondazione Milano Cortina commits to threat monitoring and crisis support, building on Paris collaboration, per ACN .
AI and Ransomware Reshape Attack Vectors
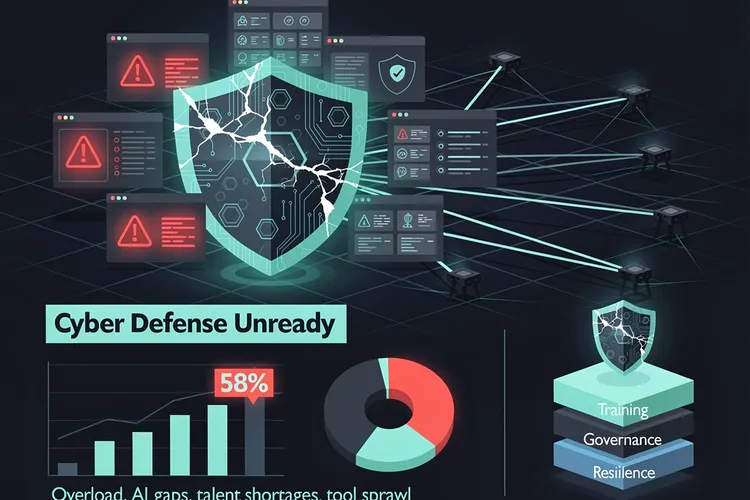
AI supercharges threats: deepfakes, rapid phishing, and automated scans for misconfigurations. Unit 42 notes attackers buying Dark Web credentials to bypass MFA-lacking systems. Ransomware gangs like Dark Scorpius phish IT staff for remote access, exfiltrating data in hours. “Ransomware gangs extort money from victims by encrypting and stealing data, or creating a chokepoint by disrupting critical systems,” states the report.
Il Sole 24 Ore echoes: “The Milan-Cortina 2026 Winter Olympic Games will attract attacks of all kinds, from state actors down to petty crooks,” targeting ticketing, turnstiles, and transport. Nation-states like Fighting Ursa (Russia-linked) and Insidious Taurus (China) seek espionage; hacktivists amplify ideologies.
Enterprises risk collateral damage: suppliers’ breached logistics could cascade to venues. Peter Evans, CEO of Xtract One Technologies, advised IT Brew : “Good cybersecurity resiliency is something that every company should be doing all the time… eventually cybersecurity pros will face an event of some kind.”
Cloudflare Dispute Heightens Vulnerabilities
A regulatory clash threatens defenses: Cloudflare, providing pro bono protection managing 20% of global traffic, faces a €14 million Agcom fine for piracy blocks. CEO Matthew Prince warned via Al Jazeera of discontinuing Olympic services, removing Italian servers, and halting investments, calling it a “scheme to censor the internet.”
This could expose networks to DDoS, as in Paris where Cloudflare aided. Italy’s TOC integrates connectivity, cloud, and cybersecurity, but enterprise partners must independently harden.
Russo urges: “Don’t try to do it yourself… bring in folks—you work with partners… to strengthen your own defense,” emphasizing maturity programs.
Enterprise Defense Imperatives
For IT chiefs, Unit 42 prescribes zero trust: enforce least privilege, continuous verification, MFA everywhere. Map attack surfaces, consolidate telemetry with AI for anomaly detection. Pre-event assessments triage ransomware readiness; during-Games, 2-hour incident response.
Galasso stresses early detection: “Our work happens before someone tries to enter a system… We look at everything that moves in the criminal ecosystem.” Enterprises should align: threat hunt, penetration tests, employee training against social engineering—where attackers escalate to domain admin in 40 minutes.
Bruno Frattasi, ACN director general, affirmed collaboration: “We will work together to provide the greatest possible cybersecurity,” per the MoU site.
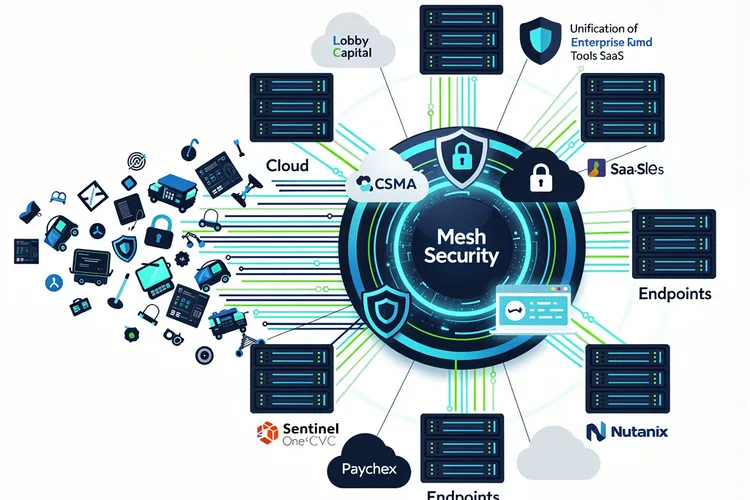
Integrated Security Backbone
Italy deploys 6,000 officers, drone surveillance, and a Milan cybersecurity command for networks and transport, per Reuters . TOC oversees accreditation, results, venue IT with 300 staff. Enterprises integrate via ISACs, Cyber Threat Alliance.
Peter Evans notes budgeting: proper practices anticipate threats beyond Olympics. Unit 42: “Gearing up… should be a gradual intensification of your existing practices. If you stay ready, you won’t have to get ready.”
As Games near, firms servicing Milano Cortina must audit partners, simulate breaches, and partner externally to shield operations from the cyber spotlight.









Leave a Reply
Your email address will not be published.