
In an era where cyber breaches routinely exploit elevated system permissions, enterprises are racing to overhaul privileged access management, or PAM, to mitigate risks that legacy tools can no longer contain. Standing privileges—persistent high-level access rights—expose sensitive production environments to devastating attacks, a vulnerability that becomes starkly evident during compliance reviews. “Most teams modernize privileged access because standing and excessive access to sensitive systems creates real business risk,” states content from a GovInfoSecurity webinar sponsored by P0 Security.
That risk sharpens amid SOC 2 audits, regulatory deadlines, security incidents, or cyber insurance evaluations, where proving control over privileged sessions proves essential. Traditional PAM solutions, reliant on vaults and static credentials, falter in dynamic cloud and hybrid setups, leaving gaps that attackers exploit through credential theft and lateral movement. Modern approaches demand just-in-time, just-enough access tied to verifiable user identities, complete with session-level logging for irrefutable audit trails.
Audit Triggers Reshape Security Priorities
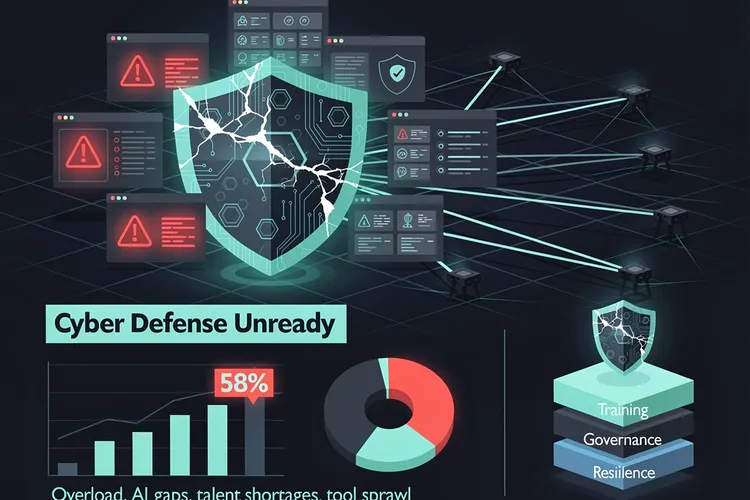
The push for PAM modernization stems directly from escalating compliance pressures. Regulators under NIST, ISO/IEC 27001, and SOC 2 now mandate granular governance of privileged accounts, while cyber insurers require multi-factor authentication, session recording, and ephemeral access as prerequisites for coverage. “Gartner estimates that 15–25% of new PAM deployments are now driven directly by cyber insurance requirements,” reports 12Port .
Industry data underscores the urgency: Privileged credentials fuel 80% of breaches, with average costs hitting $4.88 million per incident, according to IDM Works . Organizations face not just fines but operational paralysis when auditors demand evidence of least-privilege enforcement across sprawling infrastructures.
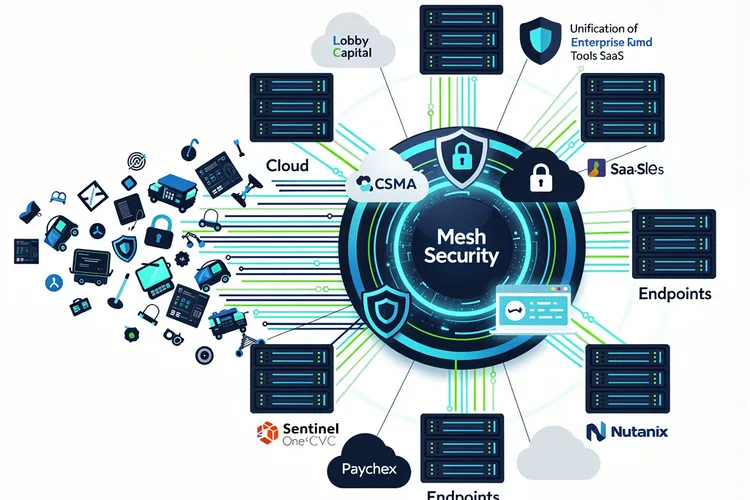
Cloud proliferation compounds these challenges, as ephemeral resources and containerized workloads multiply non-human identities—service accounts and API keys—outnumbering human users 80-to-1, per Apono . Legacy PAM struggles here, unable to scale without introducing friction that hampers DevOps velocity.
Legacy Pitfalls in Hybrid Realms
Conventional PAM platforms, built for on-premises vaults, impose complex workflows and persistent privileges that clash with agile environments. “Common limitations include persistent standing privilege that expands attack surfaces, complex workflows that reduce administrator compliance, limited visibility into modern cloud and hybrid environments,” notes Netwrix . These tools often demand dedicated appliances, driving up costs and deployment times to months.
Attackers capitalize on such weaknesses, using stolen admin credentials for quiet escalation. PAM must evolve to Zero Standing Privileges, enforcing temporary elevation with real-time monitoring. Solutions now integrate with identity providers for seamless single sign-on, eliminating shared passwords that plague teams.
The market reflects this shift, projected to reach $4.44 billion in 2026, growing at 23.3% CAGR from 2024, fueled by Zero Trust mandates and ransomware defenses, as detailed by Netwrix. Vendors like CyberArk and Delinea lead with platforms offering vaultless access and behavioral analytics.
Just-in-Time Access Redefines Controls
Core to next-generation PAM is just-in-time provisioning, granting elevated rights only for approved durations via ticketing integration. “This ensures privileged access is granted only through approved, documented change or incident tickets, and also helps create audit-ready records,” explains miniOrange . Sessions record every keystroke and query, feeding SIEM tools for anomaly detection powered by machine learning.
Cloud-native options like StrongDM and KeeperPAM emphasize agentless deployment, supporting SSH, RDP, Kubernetes, and databases without infrastructure overhauls. “StrongDM tracks every query, keystroke, and access attempt and generates human-readable logs,” states StrongDM .
For non-human identities, secrets management automates rotation, preventing static keys from becoming liabilities. Gartner Peer Insights highlights Delinea’s hybrid focus: “Delinea specializes in the provision of Privileged Access Management solutions, catering to the needs of the modern, hybrid enterprise,” praising its authorization for diverse identities.
Market Leaders Gear for Scale
CyberArk’s platform isolates sessions without native experience loss, enforcing policies across vaulted and zero-privilege modes. “Centrally monitor all user behavior for forensics, audit and compliance—from a single pane of glass,” it promises on its product page . BeyondTrust layers granular visibility over IAM, curbing privileged commands.
Emerging players like 12Port integrate microsegmentation to block post-access lateral movement, a feature absent in vault-centric rivals. Netwrix Privilege Secure targets rapid deployment for maturity upgrades, recording changes in tamper-evident formats for insurers.
Gartner’s taxonomy—privileged account/session management, elevation/delegation, secrets, CIEM, remote PAM—guides selections, with peer reviews favoring scalable, low-overhead tools. The Gartner Peer Insights platform rates solutions on deployment ease and risk reduction.
Audit Checklists for Compliance Triumph
Effective PAM audits verify least-privilege adherence, MFA enforcement, session retention (90 days searchable, one-year archived), and anomaly alerts. Infisign advises presenting structured reports linking controls to regulations, simplifying reviews. “A PAM audit is a structured review of how privileged access is granted, used, monitored and removed,” per its guide .
Quarterly self-assessments, as recommended by Securden, maintain readiness, automating evidence collection. P0 Security’s webinar previews SOC 2 walkthroughs, showing live evidence generation—critical as 2026 frameworks tighten non-human identity scrutiny.
Forward trends include AI-driven behavioral baselines and browser-based access sans VPNs, per Help Net Security . “In 2026, AI will go beyond passive monitoring and become a proactive participant in securing IT resources via privileged sessions.”
Implementation Paths Forward
Teams start with discovery: mapping all privileged accounts, eliminating defaults, and applying least privilege. Integrate with ITSM for ticket-gated access, then layer monitoring. Microsoft Security stresses visibility into human and workload privileges, governing elevation dynamically.
Success metrics include reduced standing privileges, faster audits, and breach containment. As X posts from @cyber_spanish echo Gartner, PAM enables Zero Trust beyond compliance. Enterprises modernizing now position for resilient operations amid 2026’s threats.









Leave a Reply
Your email address will not be published.