
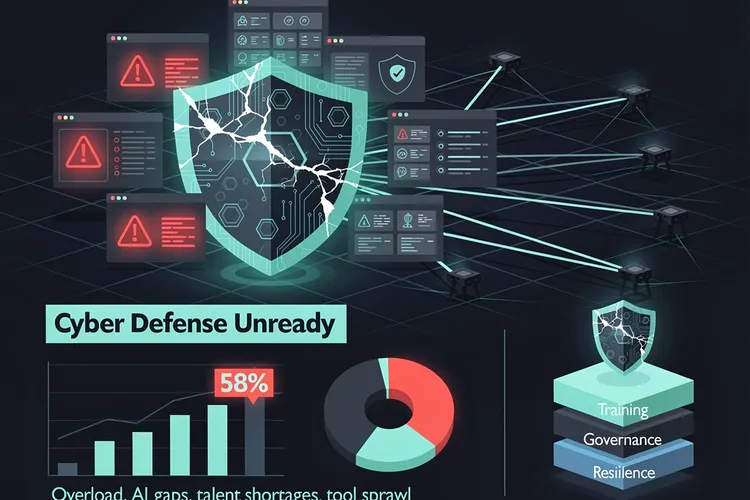
In the high-stakes arena of enterprise cybersecurity, where endpoints serve as the primary breach vectors, Samsung Electronics is positioning its Knox platform as the vanguard of zero trust architecture. Dr. Jerry Park, executive vice president and head of the global mobile B2B team at Samsung’s mobile experience business, laid out this strategy in a January 27, 2026, editorial, declaring, “A systematic, comprehensive approach is critical to ensuring seamless mobile capabilities and uncompromising cyber-protection.” With 70% of successful breaches originating from endpoints according to IDC data cited in Samsung News , Samsung’s shift from network-centric defenses to endpoint fortification arrives at a pivotal moment.
Mobile devices, now the dominant gateway to corporate networks amid remote and hybrid work, expose vast attack surfaces through suspicious URLs, insider threats, malware, and emerging AI risks like prompt injection. Park emphasized, “Endpoints have the largest attack surface and are the most challenging IT assets to protect against cyberattacks.” Samsung Knox, a defense-grade multilayer platform embedded in Galaxy hardware from the chipset level, enforces “never trust, always verify” by continuously assessing user identity, device posture, behavioral signals, and context such as location and time before granting access.
Endpoint Vulnerabilities Demand Radical Shifts
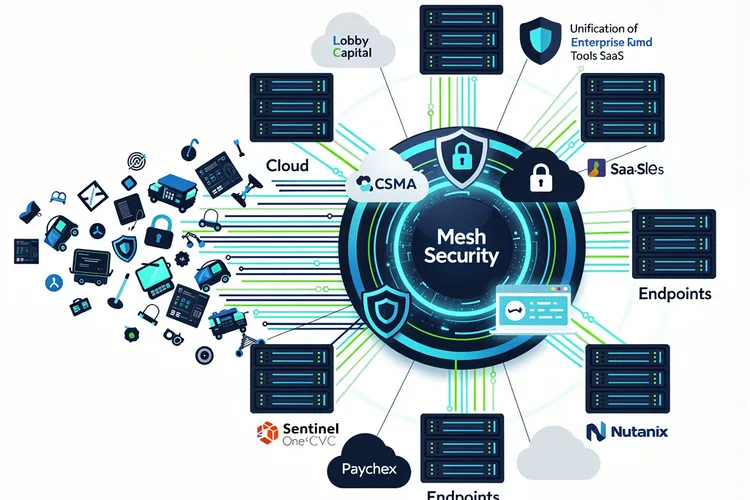
Traditional perimeter defenses falter as cloud apps, BYOD policies, and hyperconnectivity blur boundaries. Samsung’s zero trust model restricts privileges dynamically, isolating suspicious activity and integrating with enterprise tools for real-time enforcement. As detailed in Samsung’s Knox documentation updated March 7, 2025, the platform leverages ARM TrustZone for hardware-rooted trust, secure boot, and Knox Vault—a physically isolated chip certified to CC EAL 4/5+ standards that safeguards credentials and biometrics even if the main OS is compromised ( Samsung Knox Whitepaper ).
Knox’s architecture spans hardware, kernel, OS, and app layers, with features like DEFEX for exploit detection and Message Guard against zero-click attacks via SMS. The Knox Zero Trust Framework, introduced with Android 14, logs over 100 security signals in a privacy-filtered database, enabling SOC integration for threat hunting without exposing user data ( Samsung Knox Docs ).
Hardware-Backed Attestation Redefines Device Trust
Central to Samsung’s strategy is hardware-backed on-device attestation, first integrated with Microsoft Intune in 2023—the industry’s inaugural solution working on both corporate and personal devices. Now default in Intune’s Android App Protection Policies, it verifies device integrity before access, as noted in a Samsung Knox blog: “Samsung Knox On-Device Attestation is now enabled by default in Intune—making it easier to enforce Zero Trust” ( Samsung Knox Blog ). Further, Knox Asset Intelligence connects directly to Microsoft Sentinel SIEM, streaming near-real-time telemetry for fleet-wide monitoring.
In 2024, Samsung partnered with Cisco Secure Access, a Security Service Edge solution, to verify identity, threats, and context for high-speed Zero Trust Network Access (ZTNA) without VPNs—even on unmanaged BYOD devices running Android 15+. Park stated, “It is only through open collaboration with partners that we can bring the most advanced solutions to our customers” ( Samsung News US ).
Strategic Partnerships Accelerate Adoption
Knox Suite bundles these capabilities with management tools like Knox E-FOTA for staged firmware updates and Knox Asset Manager for telemetry. For foldables and rugged devices, Knox Vault and Enhanced Encrypted Protection (KEEP) in One UI 8 isolate AI features on-device, addressing 2025 threats like those in Verizon’s Data Breach Report where 60% involve human elements ( The Hacker News ). CIO.com highlights how Knox refines telemetry into SOC-digestible events: “The Samsung Knox Zero Trust framework… enabling better threat detection for admins” ( CIO ).
By Android 15, Knox enables prioritized SOC alerts and ZTNA augment requests. Certifications from the U.S., U.K., Australia, Canada, Netherlands, and Germany’s BSI underscore its rigor. Park affirmed, “These collaborative solutions are a testament to our commitment to not only adhere to industry standards but to also drive their continued development.”
Knox Innovations Counter Evolving Threats
Amid AI-driven attacks, Knox’s 2026 updates integrate on-device AI defenses for zero-day detection via system call analysis ( AirDroid ). Knox Matrix extends protection across Galaxy ecosystems, with dashboards in One UI 7 for transparent oversight. Samsung Business Insights notes, “Galaxy devices also benefit from… Knox Enhanced Encrypted Protection (KEEP), which debuted with One UI 8” ( Samsung Insights ).
For enterprises, Knox Platform for Enterprise offers granular controls, from auto-blocker against sideloading to warranty bit for tamper detection. As Park concluded, “As threats become increasingly complex with AI and hyperconnectivity taking centre stage, security and privacy are more important now than ever before.” Samsung’s endpoint-centric zero trust not only mitigates risks but empowers productivity, setting a benchmark for mobile security in regulated sectors like finance and defense.









Leave a Reply
Your email address will not be published.