
In the evolving arena of cybersecurity, where hybrid work models and unchecked AI adoption expose enterprises to unprecedented vulnerabilities, Sophos has unveiled Workspace Protection—a browser-centric suite poised to redefine access controls and threat mitigation. Announced in January 2026, this offering targets the core of modern workflows, where 85% of the workday unfolds inside web browsers, according to Sophos press release citing Omdia research.
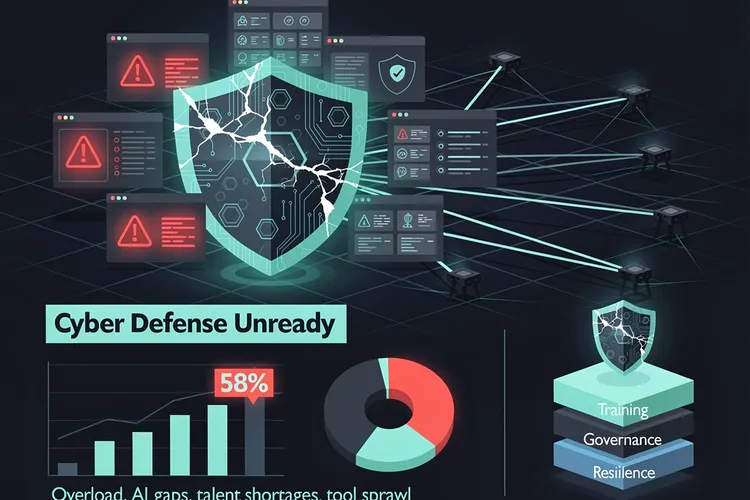
At its heart lies the Sophos Protected Browser, a hardened Chromium-based tool powered by Island’s enterprise technology. This browser integrates zero-trust network access (ZTNA), DNS filtering, and data loss prevention directly into the user’s daily interface, eliminating the need for traffic backhauling through costly centralized gateways typical of traditional SASE deployments. “Security teams are increasingly impacted by complexity as hybrid work, SaaS adoption and AI tools expand the workspace,” noted Mike Jude, research director at IDC, in coverage by SiliconANGLE .
Browser as Battleground
The Protected Browser enforces policies on application usage, local data handling, and web access, transforming what has long been a vulnerability hotspot into a fortified asset. It supports SSH and RDP for remote administration while providing granular visibility into shadow IT—unsanctioned apps that proliferate in distributed environments. Sophos ZTNA, now embedded within the browser, grants posture-based entry to private applications, verifying user identity and device compliance before allowing connections, as detailed in the Sophos blog introduction .
Complementing this are Sophos DNS Protection for endpoints, which blocks malicious domains across all protocols using DNS over HTTPS on Windows devices, and the Email Monitoring System, an overlay for Google Workspace or Microsoft 365 that flags phishing and unwanted messages. Existing ZTNA users gain automatic bundle access, streamlining upgrades for Sophos loyalists.
Targeting Shadow AI Proliferation
With over half of global employees using AI tools sans formal oversight—per a KPMG and University of Melbourne survey cited in Sophos materials—Workspace Protection delivers unified oversight into data shared with generative AI services. IT admins monitor interactions, block risky uploads, and promote approved tools, mitigating exfiltration threats inherent in tools like ChatGPT. “Organizations can now embrace AI while ensuring data stays protected, all through the browser people already use,” stated Mike Fey, co-founder and CEO of Island, in the Enterprise IT World report .
This governance extends to contractors and guests on unmanaged devices, enabling secure BYOD and third-party access without compromising core networks. Policies persist network-agnostically, a boon for firms juggling office returns and remote setups.
Edge Over SASE Heavyweights
Unlike SASE platforms from vendors like Zscaler or Palo Alto Networks, which demand infrastructure overhauls and incur latency from traffic rerouting, Sophos emphasizes point-of-activity enforcement. This slashes operational costs and overhead, appealing to midmarket players underserved by enterprise-grade SSE. “Sophos Workspace Protection reflects a pragmatic shift in the market—delivering core SASE and SSE outcomes through an integrated, endpoint- and browser-centric approach,” Jude affirmed to SiliconANGLE.
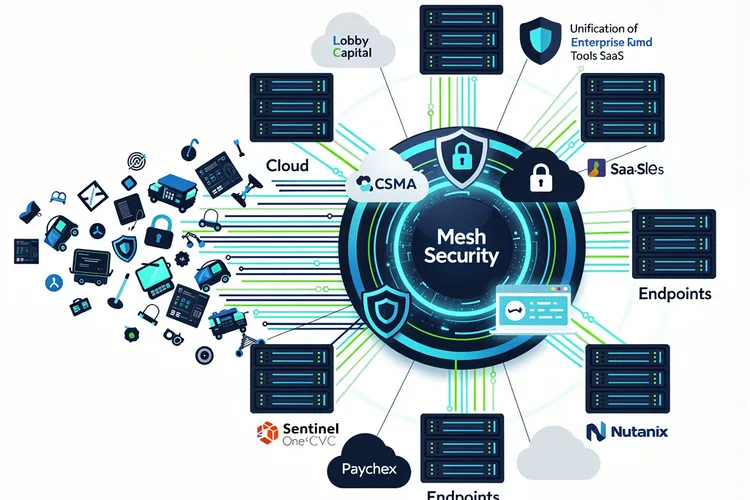
Management occurs via Sophos Central, the firm’s cloud console, integrating with Endpoint, Firewall, and MDR for synchronized defenses. Security Heartbeat now factors into ZTNA policies, auto-blocking compromised endpoints from app access—a feature extending across Sophos’ ecosystem.
Deployment Realities and Early Momentum
Components like the Protected Browser and DNS Protection entered early access in January 2026 via Sophos Central for licensed customers, with full general availability slated for late February. Free trials launch alongside GA, per the Sophos blog. No public pricing emerged, but per-user subscriptions align with Sophos’ model, positioning it as cost-effective versus SASE rivals.
Partner chatter on X highlights revenue potential, with NSS Corporation touting it as ideal for Firewall and Endpoint upsells. Sophos’ official X account underscored the 85% browser stat, linking back to the press release, signaling marketing push amid 600,000+ customers worldwide.
Strategic Fit in Threat Evolution
For industry insiders, Workspace Protection slots into Sophos’ synchronized security fabric, fortifying perimeters dissolved by cloud shifts. It addresses phishing via email monitoring, web threats through DNS and gateway functions, and insider risks via data controls—holistic coverage without silos. Joe Levy, Sophos CEO, emphasized in the press release: “By combining Island’s enterprise browser technology with Sophos’ security capabilities… we are helping organizations govern AI use, protect critical data, and secure hybrid workforces with a solution that is easier to deploy and manage.”
As hybrid persists and AI integrates deeper, this browser-led pivot could pressure competitors to simplify stacks, much like endpoint convergence years ago. Early adopters stand to gain frictionless productivity gains, but success hinges on seamless Island integration and Central scalability.









Leave a Reply
Your email address will not be published.