
In the high-stakes world of operational technology, where a single breach can halt production lines worth millions per hour or compromise critical infrastructure serving entire regions, cybersecurity professionals face a paradox that has plagued the industry for over a decade: they cannot convincingly prove their value to executive leadership. Despite mounting threats and increasingly sophisticated attack vectors targeting industrial control systems, OT security teams struggle to translate their defensive victories into the language of business metrics that resonate in boardrooms.
This challenge has persisted even as the threat environment has evolved dramatically. According to Industrial Cyber , the fundamental issue lies not in the absence of threats or the lack of security expertise, but in the inherent difficulty of quantifying the value of incidents that never occurred. Unlike IT security, where data breaches can be measured in records compromised or regulatory fines incurred, OT cybersecurity operates in a realm where success means maintaining the status quo—a notoriously difficult proposition to budget for or celebrate.
The disconnect between operational technology security teams and business leadership has created a dangerous gap in corporate risk management. While chief information security officers in traditional IT environments have developed sophisticated frameworks for demonstrating return on investment, their counterparts in industrial environments lack comparable tools. The absence of standardized metrics for OT security value has left many organizations underinvesting in protections for systems that, if compromised, could result in catastrophic physical consequences, environmental disasters, or threats to human safety.
The Attribution Problem: When Success Means Nothing Happens
The core challenge facing OT cybersecurity professionals stems from what security experts call the “negative proof” problem. When security measures work as intended, the result is an absence of incidents—a non-event that generates no headlines, triggers no emergency response protocols, and requires no crisis management. This creates a perverse incentive structure where security teams must hope for small, contained incidents to justify their budgets, even as their primary mission is preventing any incidents whatsoever.
Industry veterans have witnessed this dynamic play out repeatedly across manufacturing, energy, and critical infrastructure sectors. Security investments that successfully thwart attacks often go unrecognized because the attacks themselves may never be detected by business leadership. Unlike a prevented data breach in IT systems, where logs and attempted intrusions can be documented and presented, many OT security victories involve stopping reconnaissance activities or blocking initial access attempts that never progress to the point where they would impact operations.
The Convergence Conundrum: When IT Metrics Don’t Translate
The increasing convergence of IT and OT systems has paradoxically made the value proposition more difficult rather than easier to articulate. As industrial networks connect to corporate systems and cloud platforms, security teams face pressure to adopt IT-centric security frameworks and measurement approaches that fundamentally misunderstand the unique requirements of operational technology. The availability-first mentality of OT environments—where uptime and safety trump confidentiality—doesn’t align with traditional cybersecurity metrics focused on data protection.
This misalignment has created tension in organizations attempting to unify their security operations. IT security teams measure success through metrics like mean time to detect, number of vulnerabilities patched, and percentage of systems with current security updates. In OT environments, however, patching systems may require production shutdowns scheduled months in advance, vulnerability scanning can disrupt sensitive industrial protocols, and detection systems must be carefully tuned to avoid false positives that could trigger unnecessary safety shutdowns costing millions in lost production.
The Risk Quantification Gap: Beyond Compliance Checkboxes
Traditional approaches to cybersecurity value proposition have relied heavily on regulatory compliance as a proxy for security effectiveness. Organizations point to their adherence to standards like NIST, IEC 62443, or industry-specific frameworks as evidence of their security posture. However, compliance-based arguments have proven insufficient for securing the resources necessary to address evolving threats. Compliance represents a baseline, not a comprehensive security strategy, and executives increasingly recognize that checking regulatory boxes doesn’t prevent determined adversaries from compromising industrial systems.
The limitations of compliance-focused value propositions became starkly apparent following high-profile incidents affecting critical infrastructure. When attacks succeed despite certified compliance programs, the entire framework of using regulatory adherence as a security metric loses credibility. Security teams need methods for quantifying risk reduction that go beyond compliance percentages and instead connect security investments to business outcomes like production reliability, asset longevity, and operational resilience.
The Asymmetric Information Challenge: What Leadership Doesn’t Know
A significant obstacle to proving OT cybersecurity value lies in the information asymmetry between security professionals and business executives. Security teams possess detailed technical knowledge about threat actors, attack methodologies, and system vulnerabilities, but often lack the business acumen to translate these technical realities into strategic business risks. Conversely, executives understand business impact and financial metrics but may lack the technical background to appreciate the severity of OT-specific threats or the complexity of implementing effective defenses.
This communication gap has led to chronic underinvestment in OT security across multiple industries. When security professionals present technical details about vulnerabilities in programmable logic controllers or the risks of unencrypted industrial protocols, executives struggle to connect these technical issues to concrete business impacts. The result is a cycle where security teams receive insufficient resources, which limits their ability to demonstrate value, which in turn makes future resource requests even more difficult to justify.
The Insurance Industry’s Failed Promise
Many security professionals had hoped that the maturation of cyber insurance markets would provide an external validation mechanism for OT security investments. The theory held that insurance premiums would reflect actual risk levels, creating market-based incentives for organizations to invest in security controls that demonstrably reduced risk. However, the cyber insurance market for OT environments has struggled to develop the actuarial sophistication necessary to accurately price OT-specific risks, leaving this potential value-demonstration mechanism largely unrealized.
Insurance carriers have found OT risk assessment particularly challenging due to the lack of historical incident data, the difficulty of modeling cascading failures in interconnected industrial systems, and the potential for catastrophic losses that exceed traditional insurance capacity. As a result, cyber insurance policies often exclude or severely limit coverage for OT incidents, or price coverage at levels that make it economically unviable for many organizations. This leaves security teams without the external validation that insurance-based risk pricing could provide to justify their budgets and strategic importance.
Emerging Frameworks: The Search for Meaningful Metrics
Despite these persistent challenges, new approaches to demonstrating OT security value are beginning to emerge from leading organizations and industry groups. Some security teams have found success by reframing their value proposition around operational resilience rather than pure security metrics. By positioning security investments as enablers of reliable production, reduced unplanned downtime, and extended asset lifecycles, they connect security spending to outcomes that executives already measure and value.
Forward-thinking organizations are developing custom metrics that bridge the gap between technical security measures and business outcomes. These include tracking the relationship between security posture improvements and reductions in unplanned maintenance events, measuring how security controls contribute to regulatory compliance that enables market access, and quantifying how security investments protect the intellectual property embedded in industrial processes. While these approaches require significant effort to implement and validate, they represent promising directions for making OT security value more tangible and demonstrable to business leadership.
The Human Factor: Skills Shortages Compound the Problem
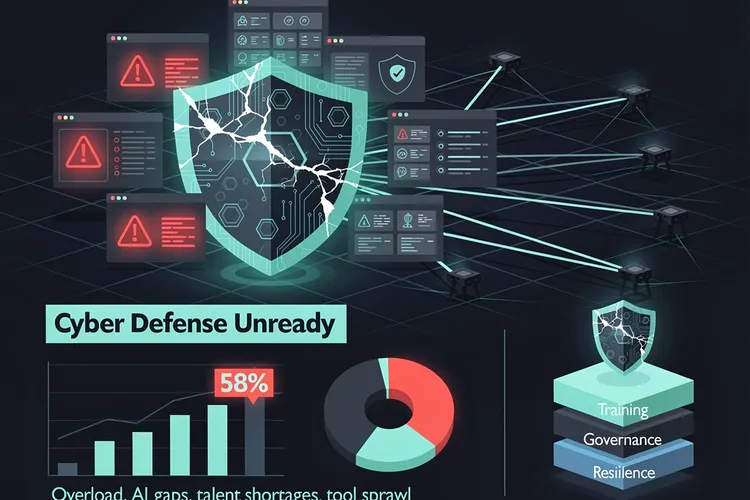
The challenge of proving OT security value is exacerbated by a severe shortage of professionals who possess both deep operational technology expertise and cybersecurity knowledge. This skills gap means that many organizations lack personnel capable of building the business cases and measurement frameworks necessary to demonstrate security value effectively. The few professionals who do possess this hybrid skill set are in such high demand that they command premium compensation, making it difficult for many organizations to access the expertise needed to solve their value-demonstration challenges.
This talent shortage also affects the quality of security implementations in OT environments. When security programs are designed and managed by professionals without sufficient OT domain knowledge, they may implement controls that interfere with operations, create new safety risks, or fail to address the most critical threats. These missteps damage the credibility of security teams and make future value propositions even harder to sell to skeptical executives who have witnessed security initiatives that created more problems than they solved.
The Path Forward: Integration, Education, and Evolution
Addressing the OT security value proposition challenge will require coordinated efforts across multiple dimensions. Security professionals must invest in developing business acumen and communication skills that enable them to translate technical security concepts into business language. Organizations need to create career development paths that cultivate the hybrid OT-security expertise the industry desperately needs. Industry groups and standards bodies should work to develop standardized frameworks for measuring and reporting OT security value that enable benchmarking and comparison across organizations.
Equally important is the need for executive education initiatives that help business leaders understand the unique characteristics of OT security risks and why traditional IT security metrics may not apply. As operational technology becomes increasingly central to competitive advantage and business model innovation, executives must develop literacy in OT security sufficient to make informed resource allocation decisions. The organizations that successfully bridge the communication gap between security teams and business leadership will be better positioned to defend against the sophisticated threats targeting industrial systems while maintaining the operational excellence that drives business success. The question is no longer whether OT security delivers value, but whether organizations can develop the frameworks and communication channels necessary to recognize and act on that value before a catastrophic incident forces the issue.









Leave a Reply
Your email address will not be published.