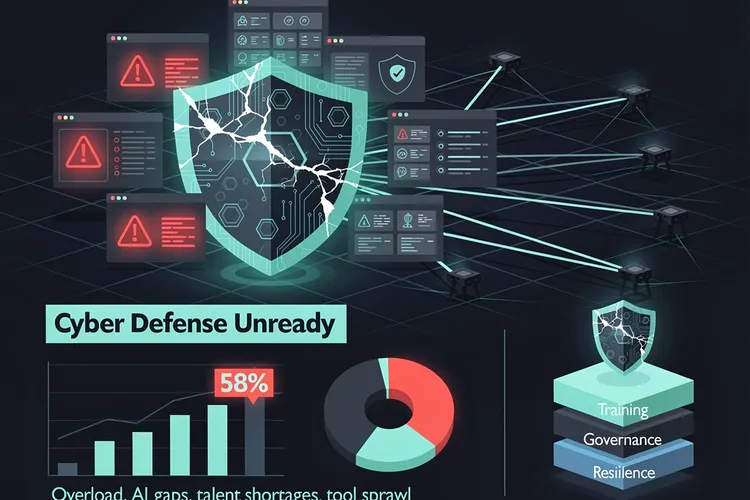
Organizations worldwide spent billions on security awareness training last year, yet phishing success rates remain stubbornly high and human error continues to be the leading cause of data breaches. This paradox has forced chief information security officers to confront an uncomfortable truth: teaching employees about cybersecurity threats doesn’t necessarily change their behavior when it matters most.
The traditional approach to security awareness training—mandatory annual sessions, simulated phishing tests, and knowledge assessments—has reached its limits. According to CSO Online , despite increasing investment in these programs, they continue to deliver marginal benefits. The fundamental problem lies in the assumption that knowledge equals behavior change, a premise that decades of psychological research has repeatedly disproven.
Enter human risk management, a paradigm shift that prioritizes measuring and modifying actual behaviors rather than testing knowledge retention. This approach recognizes that cybersecurity is fundamentally a human problem requiring behavioral solutions, not merely an educational challenge. Forward-thinking CISOs are now deploying sophisticated analytics to identify high-risk behaviors, implementing targeted interventions, and creating organizational cultures where secure practices become the path of least resistance.
The Measurable Failure of Traditional Training Programs
The data surrounding traditional security awareness training effectiveness tells a sobering story. Research consistently shows that employees can pass knowledge tests with flying colors yet still click on malicious links minutes later. The disconnect between knowing what’s right and doing what’s right represents the core challenge that human risk management seeks to address.
Organizations have invested heavily in compliance-focused training models that emphasize checkbox completion over behavioral transformation. These programs typically measure success through completion rates and quiz scores—metrics that correlate poorly with actual security outcomes. When breaches occur, post-incident analyses frequently reveal that the employees who fell victim to attacks had recently completed their annual security training and performed well on assessments.
Understanding the Psychology Behind Security Behaviors
Behavioral psychology research demonstrates that knowledge transfer alone rarely drives sustained behavior change, particularly when new behaviors require additional effort or slow down work processes. Employees operating under time pressure, cognitive load, or stress default to habitual patterns rather than applying learned security principles. This psychological reality explains why even well-trained employees make security mistakes.
The concept of “security fatigue” further complicates matters. As organizations implement increasingly complex security controls and policies, employees experience decision fatigue and alert desensitization. When every action requires security considerations and systems generate constant warnings, people develop coping mechanisms that often involve ignoring or circumventing security measures. Human risk management acknowledges these psychological factors and designs interventions accordingly.
Data-Driven Behavioral Analysis Replaces One-Size-Fits-All Training
Modern human risk management platforms leverage behavioral analytics to create detailed risk profiles for individuals and departments. Rather than treating all employees as equally risky, these systems identify patterns indicating elevated risk—such as frequently accessing sensitive data from unusual locations, regularly requesting password resets, or demonstrating poor email hygiene. This granular visibility enables targeted interventions for those who need them most.
The shift toward continuous monitoring and micro-interventions represents a fundamental departure from annual training cycles. Instead of hour-long training sessions once yearly, human risk management delivers brief, contextual guidance at moments when employees encounter actual security decisions. This “just-in-time” approach aligns with adult learning principles and proves far more effective at influencing behavior than abstract, decontextualized training modules.
Implementing Friction-Reducing Security Architecture
A cornerstone of effective human risk management involves making secure behaviors easier than insecure ones. Security teams are redesigning systems and processes to reduce the friction associated with secure practices. When security measures require excessive effort or significantly slow workflows, employees inevitably find workarounds—a rational response to poorly designed systems rather than willful negligence.
Examples of friction-reducing security include implementing single sign-on solutions that eliminate password fatigue, deploying passwordless authentication systems, and creating secure file-sharing platforms that are more convenient than consumer alternatives like personal email. By acknowledging that employees will choose the path of least resistance, human risk management focuses on ensuring that path is also the most secure.
Measuring What Matters: Behavioral Metrics Over Knowledge Scores
Traditional security awareness programs measure inputs and outputs that don’t correlate with actual risk reduction. Completion rates, test scores, and hours of training completed tell organizations little about whether their security posture has improved. Human risk management instead focuses on behavioral metrics that directly indicate risk levels.
These metrics include phishing click-through rates measured continuously rather than through announced tests, frequency of security policy violations detected through monitoring systems, speed of reporting suspected incidents, and adoption rates of security tools like password managers and multi-factor authentication. By tracking behaviors that directly impact security outcomes, organizations can assess program effectiveness and identify areas requiring additional intervention.
Creating Positive Security Cultures Through Incentives and Enablement
Human risk management recognizes that punitive approaches to security violations often prove counterproductive, encouraging employees to hide mistakes rather than report them. Instead, leading organizations are building positive security cultures that reward good behaviors and treat security mistakes as learning opportunities. This cultural shift requires leadership commitment and consistent messaging that security is a shared responsibility rather than solely an IT concern.
Gamification elements, recognition programs for security-conscious employees, and transparent communication about threats and incidents help build engagement with security initiatives. When employees understand why security matters and see their role in protecting the organization, they become active participants rather than passive recipients of training. This engagement proves far more valuable than compliance achieved through fear or mandate.
Technology Enablement: AI and Automation in Human Risk Management
Artificial intelligence and machine learning technologies enable the behavioral analysis that underpins effective human risk management. These systems can process vast amounts of activity data to identify anomalous behaviors indicating either security risks or exemplary practices worth replicating. Automated systems can deliver personalized micro-interventions at scale, something impossible with traditional training approaches.
Advanced platforms correlate behavioral data with contextual factors like job role, department, access privileges, and historical patterns to create nuanced risk assessments. This granularity allows security teams to prioritize their limited resources on the highest-risk individuals and situations. Machine learning models continuously refine their understanding of risk indicators as they process more data, improving accuracy over time.
Regulatory Compliance Meets Behavioral Reality
Regulatory frameworks increasingly recognize the limitations of checkbox compliance and emphasize demonstrable security effectiveness. Human risk management aligns well with this evolution, providing evidence of actual risk reduction rather than mere training completion. Organizations can demonstrate to auditors and regulators that they understand their human risk profile and have implemented appropriate controls.
This shift benefits both organizations and regulators. Rather than focusing on whether every employee completed annual training, assessments can examine whether the organization has reduced risky behaviors and created systems that enable secure practices. This outcomes-focused approach better serves the ultimate goal of protecting sensitive information and systems.
The Road Ahead: Integration and Continuous Improvement
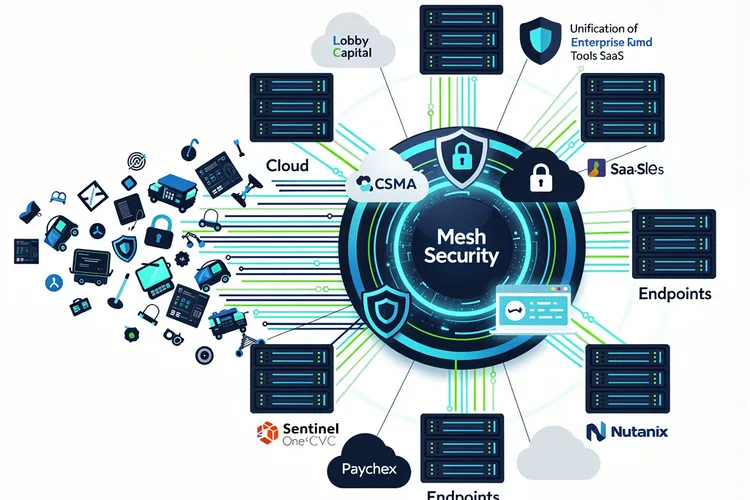
As human risk management matures, integration with broader security operations becomes essential. Behavioral risk indicators should inform access control decisions, trigger additional authentication requirements, and influence security tool deployment. This integration creates adaptive security environments that respond to actual human behaviors rather than static policies.
The future of human risk management likely involves even more sophisticated behavioral analysis, potentially incorporating factors like stress levels, workload, and personal circumstances that influence security decision-making. While privacy concerns must be carefully managed, the potential for truly personalized security guidance that accounts for individual circumstances represents the next frontier in addressing the human element of cybersecurity.
Organizations that embrace human risk management position themselves to finally break through the plateau that traditional security awareness training has reached. By acknowledging that humans are both the greatest vulnerability and the most important defense in cybersecurity, and by designing programs that work with human psychology rather than against it, these organizations build more resilient security postures. The shift from measuring knowledge to managing behavior represents not just an incremental improvement but a fundamental reimagining of how organizations approach their human security challenges.









Leave a Reply
Your email address will not be published.