
As 2026 unfolds, security leaders confront a surge in multifaceted threats where artificial intelligence blurs lines between human and machine actors, demanding new governance models and resilient strategies. Experts from Security Magazine outline expectations ranging from poly-risk environments to AI-driven identity challenges, while broader industry forecasts highlight agentic AI’s dual role in attacks and defenses.
Colin Daugherty, program manager at Convergint, warns of the ‘evolving depth and range of the already complicated poly-risk and poly-threat environments,’ encompassing cyber, privacy, physical, and supply chain risks across global scales. He questions the value of emerging technologies amid endless ‘shiny and fancy stuff,’ urging focus on people with ‘grit and resilience, curiosity, creativity, and courage.’
Kristen Devitt, director of campus safety at Oak Park River Forest High School, flags cybersecurity in schools overshadowed by active assailant focus: ‘We’ve been so focused on active assailants that we have failed to properly address other types of threats.’
AI Agents Reshape Accountability
Rosario Mastrogiacomo, CSO at SPHERE, predicts AI as ‘no longer a feature — it’s an actor,’ with challenges in accountability for non-human decisions and ‘invisible privilege escalation’ from AI identities. He advocates frameworks like RAISE—Reveal, Assign, Interpret, Secure, Evaluate—for governing adaptive AI agents, blending identity governance with AI risk.
‘The challenges in 2026 won’t be about the volume of threats — we’ve lived with that for years. The challenge will be accountability in environments where not every decision was made by a human,’ Mastrogiacomo states. Security teams must adopt ‘architectural discipline’ with least privilege and ‘operational humility’ for systems behaving like coworkers.
Frédéric Rivain, CTO at Dashline, foresees the ‘traditional network perimeter will continue its collapse,’ shifting to browser-based controls against phishing and AI agent vulnerabilities. He anticipates Fortune 500 password eliminations and passkey adoption amid credential-stuffing attacks.
Cloud and Quantum Pressures Mount
ISACA’s report on cybersecurity trends shaping 2026 emphasizes cloud-native architectures with continuous authentication, as organizations migrate amid AI’s offensive and defensive roles. Data privacy gains visibility, driving tighter governance around consumer data.
Check Point’s Cyber Security Report 2026 reveals record attacks, with AI infrastructure targeted—40% of 10,000 Model Context Protocol servers vulnerable. Attacks combine AI, identity abuse, ransomware, and social engineering faster than defenses.
IBM predicts a ‘surge in identity-focused attacks’ exploiting AI agents, urging quantum-safe algorithms as crypto-agility separates agile firms from exposed ones, per their 2026 trends .
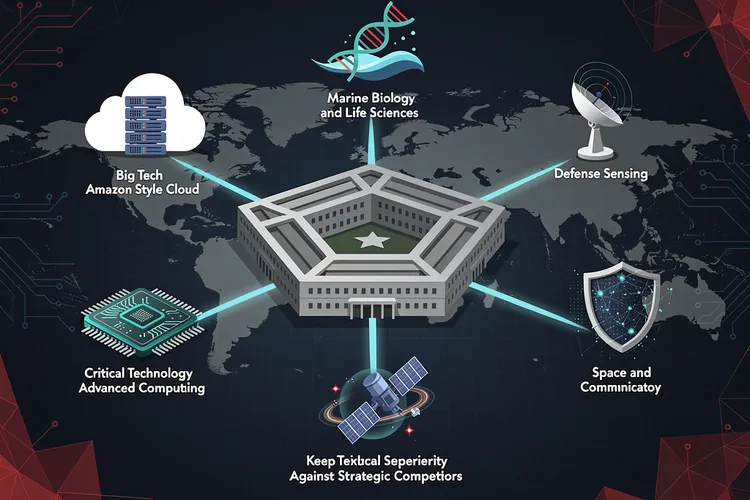
Nation-State and Resilience Demands
Google’s Mandiant and Threat Intelligence Group warn in ZDNet that ‘threat actor use of AI is expected to transition decisively from the exception to the norm,’ enhancing operations with adaptive payloads and AI-enhanced social engineering by groups like ShinyHunters.
The World Economic Forum’s Global Cybersecurity Outlook 2026 identifies AI as the top change driver per 94% of respondents, with 64% assessing AI tool security—up from 37%—amid geopolitical fragmentation and cyber inequity.
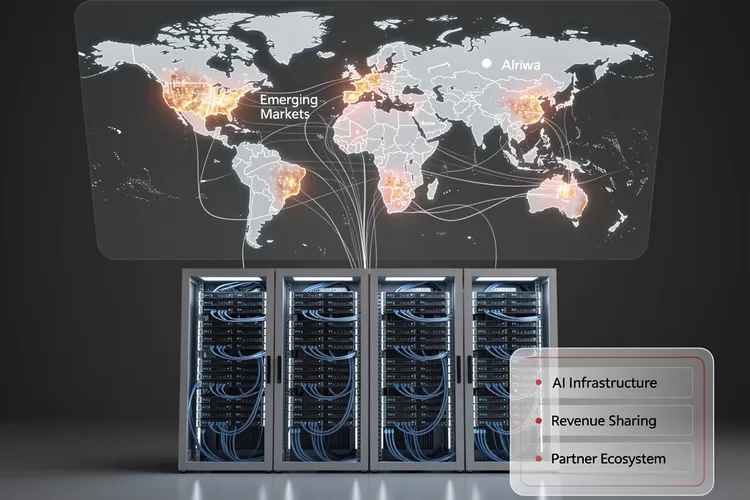
RightCrowd’s guide for physical security leaders highlights AI, cloud, and identity governance proving compliance at global scale with lean teams, per their 2026 trends .
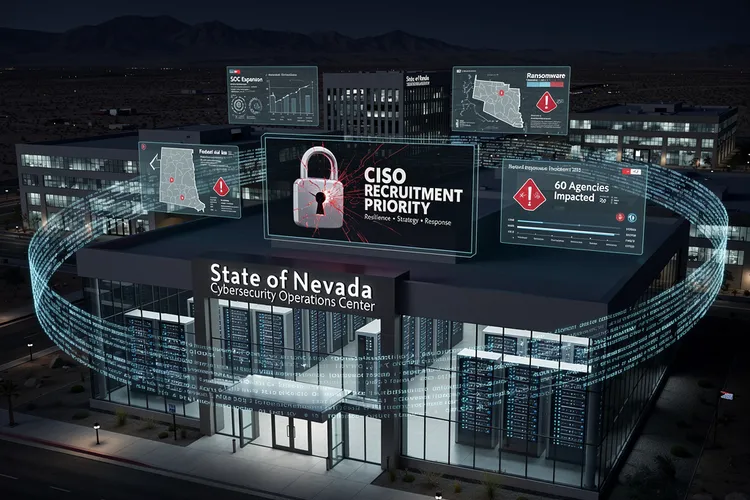
Leadership Amid Fragmentation
Security Industry Association’s 2026 Security Megatrends crowns AI’s software influence as paramount, disrupting alarm monitoring and SOCs based on 2025 surveys from leaders.
SecurityWeek’s CISO insights, like Pierre Mouallem of Delinea, note fading AI wariness: ‘CISOs now recognize rapid support of emerging technologies is essential not just for security, but for business competitiveness,’ from their Cyber Insights 2026 .
Dr. Khulood Almani on X predicts AI-driven autonomous defense, quantum risks, and regulatory pressures like NIS2, emphasizing ‘how fast you can sense, decide, and adapt.’
Path to Trusted Operations
Leaders prioritize supply chain resilience, AI governance, and simplification over hype, per SecurityWeek’s 2026 priorities . Gartner forecasts via GovTech warn of deepfakes, IoT expansion, and cybercrime professionalization.
Pinkerton anticipates Zero Trust Architecture convergence of physical and cyber signals, requiring coordinated policies. VikingCloud sees consolidation as fragmentation causes breaches, with PCI DSS v4.x demanding continuous controls.
Securiti on X underscores trusted data and sovereignty: ‘By 2026, leaders will be defined by trusted data, identity-driven controls, autonomous AI risk, and data sovereignty.’










Leave a Reply
Your email address will not be published.