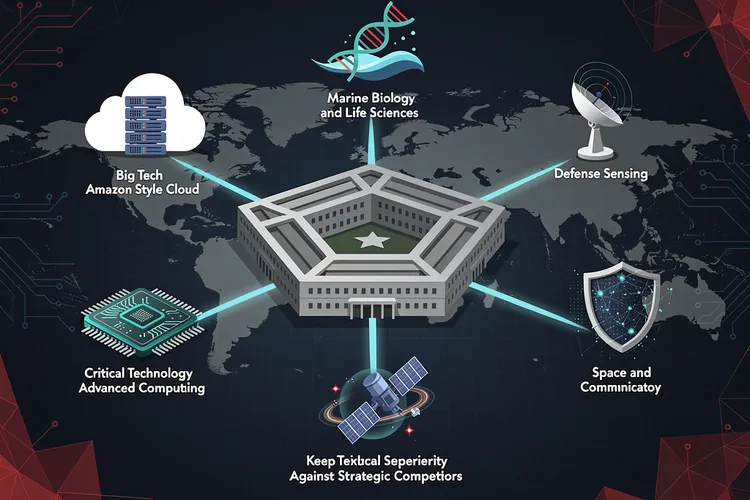
In the high-stakes arena of modern warfare, where software underpins everything from missile guidance to cyber defenses, the U.S. Department of Defense is undergoing a profound transformation. DevSecOps—integrating development, security, and operations from the outset—has emerged as the linchpin for delivering mission-critical code rapidly and resiliently. This shift promises to arm warfighters with capabilities at the ‘speed of relevance,’ as DoD leaders term it, amid escalating threats from peer adversaries.
The practice treats security not as an afterthought but as a core thread woven through the entire software lifecycle. As defined in the DoD Enterprise DevSecOps Fundamentals v2.5 , it ‘unifies software development (Dev), security (Sec), and operations (Ops), emphasizing collaboration, automation, and continuous monitoring to support secure, high-quality software delivery.’ This approach has taken root across more than 50 software factories, enabling deployments in days rather than years.
Forge of Digital Weapons
DXC Technology highlights a defense client case where Scaled Agile Framework principles and a DevSecOps model based on microservices and containerization slashed deployment times for frontline digital products. The result: faster user onboarding, heightened security confidence in sensitive environments, and assured compliance at every stage, per the firm’s industry analysis . Such outcomes underscore DevSecOps’s role in navigating compressed timelines and rising risks.
The global DevSecOps market in defense hit $2.16 billion in 2024, eyeing $11.38 billion by 2033, fueled by demands for resilient operations. Yet, in DoD’s ecosystem, the stakes amplify: software now permeates weapons systems, AI, cybersecurity, and space ops.
DoD’s Strategic Pivot
A March 2025 State of DevSecOps report by the DoD CIO reveals substantial strides. Over 78 acquisition programs embraced the Software Acquisition Pathway (SWP), with 75% delivering software in under six months. Among 40 Major Defense Acquisition Programs tracked by GAO, 75-80% adopted modern practices like Agile and DevSecOps, nearly half clocking deliveries below four months. ‘DoD views DevSecOps as a critical enabler to protecting warfighters by driving modernization,’ the report states.
Software factories—hubs of people, tools, and processes—have proliferated into mission-critical (weapons), training, infrastructure-as-code pipelines, and innovation variants. Iron Bank, boasting 1,200+ hardened containers, exemplifies supply chain fortification. Continuous Authority to Operate (cATO) supplants static assessments, embedding Zero Trust and real-time monitoring.
Air Force’s Factory Floor
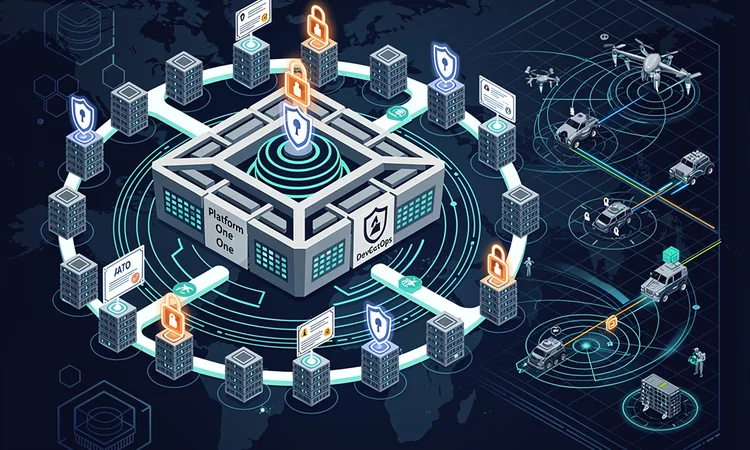
The U.S. Air Force leads with initiatives like Platform One, the backbone for DevSecOps across DoD. Hosting tools such as Big Bang for Kubernetes orchestration and Iron Bank for secure containers, it cuts approval times from years to 90 days. As detailed on software.af.mil , groups like the 309th Software Engineering Group deploy pipelines in GitLab and Azure DevOps for weapon systems, while EmeraldCode Software Factory leverages machine learning for verifiable insights.
Kessel Run and Kobayashi Maru factories deliver command-and-control updates with >99.9% uptime. GEN Duke Z. Richardson, AFMC Commander, noted of factory consolidation: ‘This retooling… is laser focused on the warfighter.’ Platform One’s mission: ‘Provide the trusted foundation to continuously develop, secure, and operate better software.’
Navy and Army Momentum
Pipeline Powerhouses
The Navy’s software factories, assessed via the Afloat Software Authorization Playbook, pumped 13 updates to a cloud app in nine months. Army Directive 2024-02 mandates modern practices, birthing the SMART team and Army Software Factory. HON. Christine E. Wormuth, Secretary of the Army, affirmed: ‘These reforms will enable the Army’s adoption of best practices… and accelerate digital transformation.’
A Software Engineering Institute (SEI) study, released May 2025, interviewed 75+ leaders from 19 organizations. ‘A combination of significant strategic initiatives and smaller efforts demonstrate successful DevSecOps implementations,’ per SEI insights . Eileen Wrubel, SEI technical director, emphasized scaling: ‘Identify opportunities to optimize investment, processes, and policies.’
Overcoming Inertia
Challenges persist: bureaucratic drag, funding silos, skill gaps, and legacy integration. The State report flags PPBE reform needs for flexible appropriations and reciprocity delays in cATO. Workforce woes include 68% citing pay gaps for turnover. Yet, Cyber Workforce Strategy introduces roles like DevSecOps Specialist, with DAU micro-learning via Coursera.
ADM Lisa Franchetti, Chief of Naval Operations, captured the urgency: ‘Speed matters… the pace at which we procure, modernize, maintain, and sustain our platforms matters.’ Software Factory Coalition fosters grassroots fixes, hosting hundreds monthly.
Frontline Victories
Real-world wins abound. USMEPCOM’s MIRS modernization ditched failed waterfall for agile MVPs. NAVSEA iterated RDT&E features in 24-48 hours. BESPIN slashed cloud setup by 99%, ATO by 90%, serving 100k+ users. F-35, F-16, and Project Overmatch harness DevSecOps for edge.
DXC’s 2025 insights echo: Frontline units report shorter deployments, higher adoption, greater trust. Defense Unicorns pioneers tailored platforms, per StartUs Insights 2026 report .
Metrics That Matter
Measuring Mission Impact
DoD tracks DORA metrics—deployment frequency, lead time, failure rate, recovery—plus DoD4 expansions tying to cyber resilience and ROI. OKRs guide: Platform One aims for 100% auto-deployments, halving cycles. ‘The path forward relies on data… to inform decision-making,’ urges the State report.
2026 trends amplify: AI agents automate scans, policy-as-code enforces compliance, per Debuglies’ 2026 forecast . DoD’s FY26 budget requests $961.6 billion base, prioritizing such tools amid great-power rivalry.
As threats evolve, DevSecOps cements asymmetric edges. Secretary Lloyd Austin III intoned: ‘Attract, train and promote a workforce… to tackle national security challenges, creatively and capably.’ This cultural and technical overhaul positions DoD to outpace foes in the code wars ahead.











Leave a Reply
Your email address will not be published.