
IT Management
IT Management focuses on governance, security, infrastructure, and operations—helping teams run reliable systems, reduce risk, and align technology with business goals.
- Home
- IT Management
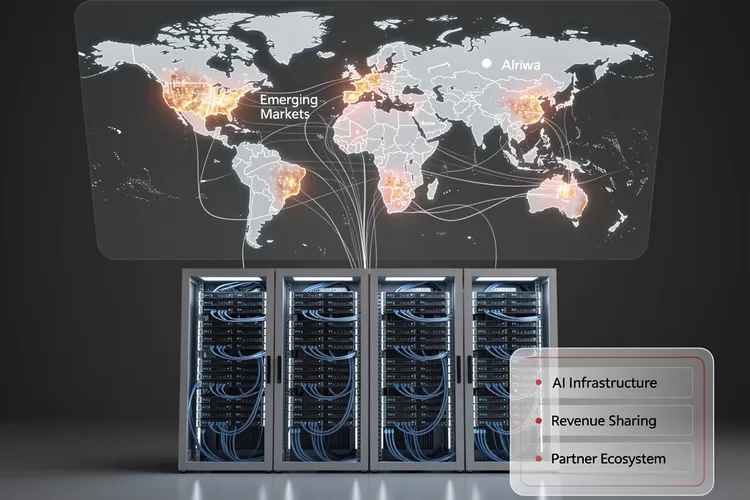
Inside Huawei Cloud’s Bold 2026 Partner Strategy: How Data Centers Become the Cornerstone of AI Infrastructure Expansion
Huawei Cloud's 2026 partner strategy positions data centers as strategic allies in AI infrastructure expansion, offering unprecedented revenue-sharing models and technical integration. The approach targets emerging markets with generous incentives while navigating geopolitical constraints and semiconductor restrictions.

Upwind’s Runtime Revolution: $250M Fuels $1.5B Cloud Security Unicorn
Upwind's $250 million Series B catapults it to $1.5 billion valuation, powering runtime-first cloud security amid 900% revenue surge. Backed by Bessemer and all-stars, the ex-Spot.io team targets AI-era threats for giants like Siemens and Roku.
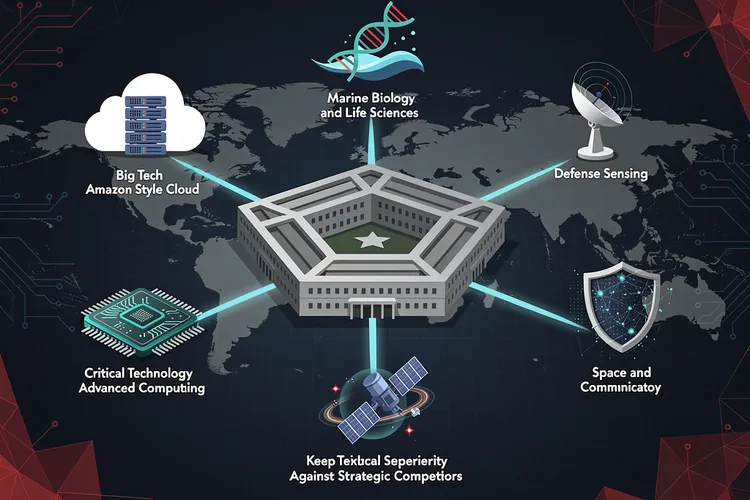
Pentagon’s New Technology Chiefs Signal Major Shift in Defense Innovation Strategy
The Pentagon's Chief Technology Officer has selected six defense technology veterans with diverse backgrounds—from Amazon executives to marine biologists—to lead Critical Technology Areas, signaling a major shift in how the Defense Department approaches innovation and maintains technological superiority against strategic competitors.
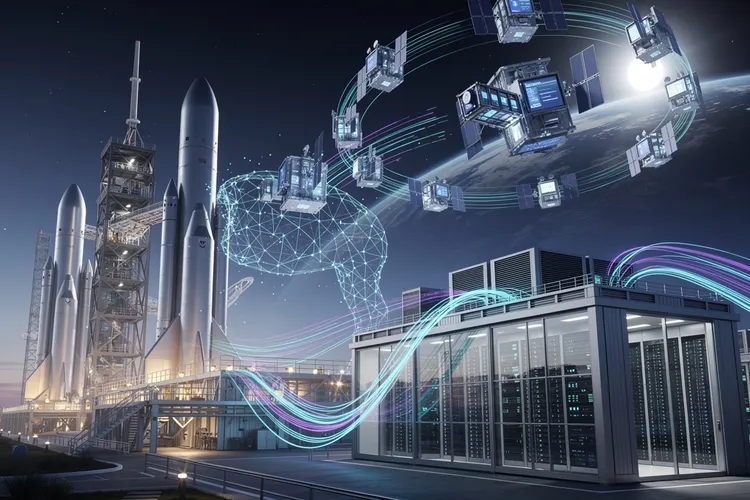
Inside Elon Musk’s Audacious Plan to Fuse Rockets and AI: The SpaceX-xAI Megamerger
Elon Musk is merging SpaceX and xAI in a deal combining an $800 billion rocket manufacturer with a $230 billion AI startup, advancing his vision of space-based data centers while consolidating his technological empire ahead of a planned summer IPO.

Verizon’s Subscriber Surge Signals Schulman’s Turnaround Triumph
Verizon crushed Q4 2025 expectations with 616,000 postpaid phone adds under CEO Dan Schulman, issuing bullish 2026 guidance post-Frontier acquisition. Revenue hit $36.4 billion, signaling a strategic revival amid fierce competition.
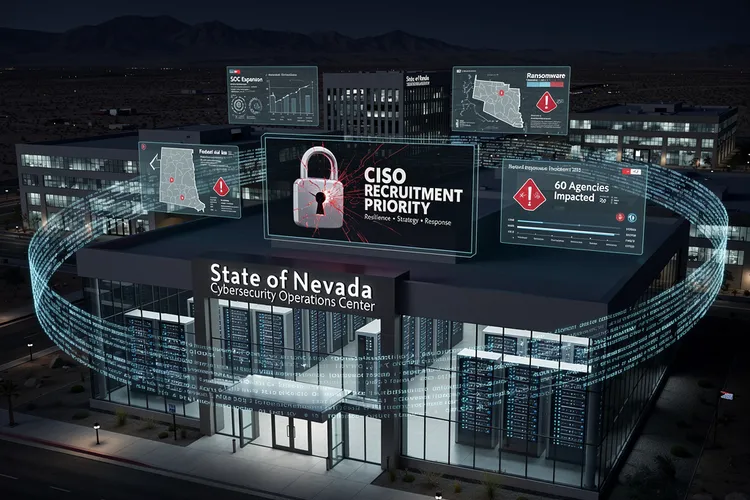
Nevada’s Urgent Hunt for a Cyber Sentinel After Ransomware Chaos
Nevada seeks a permanent CISO after 2025 ransomware chaos disrupted 60 agencies, stole data, and exposed gaps. The role demands strategy, response leadership amid SOC buildup and federal aid, signaling a hardened push for resilience.

How a Startup’s Unsecured Database Exposed the Fragility of AI Agent Platforms
Moltbook's completely exposed database allowed anyone to hijack AI agents on the platform, revealing how rapid AI deployment is outpacing basic cybersecurity practices. The incident highlights growing security debt in the AI startup ecosystem and regulatory gaps in governing autonomous agent platforms.
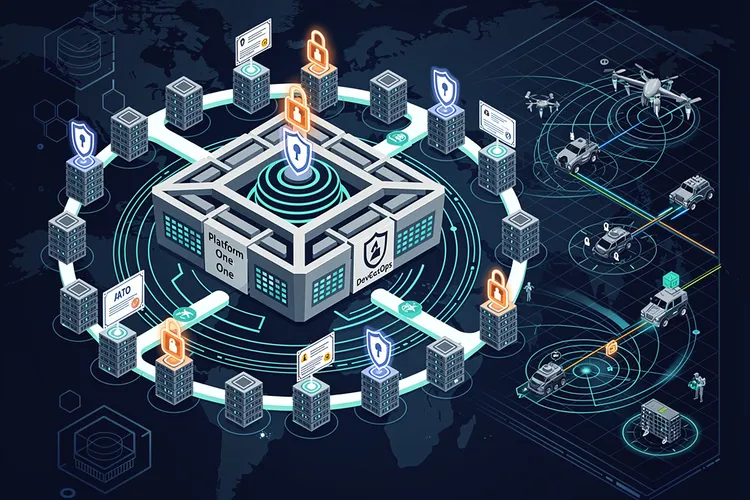
DevSecOps Arsenal: Pentagon’s Push for Warfighter Code at Warp Speed
The Pentagon's DevSecOps revolution integrates security into rapid software delivery, powering over 50 factories and slashing deployment times. From Platform One's secure pipelines to cATO approvals, it equips warfighters with resilient digital edge against evolving threats.
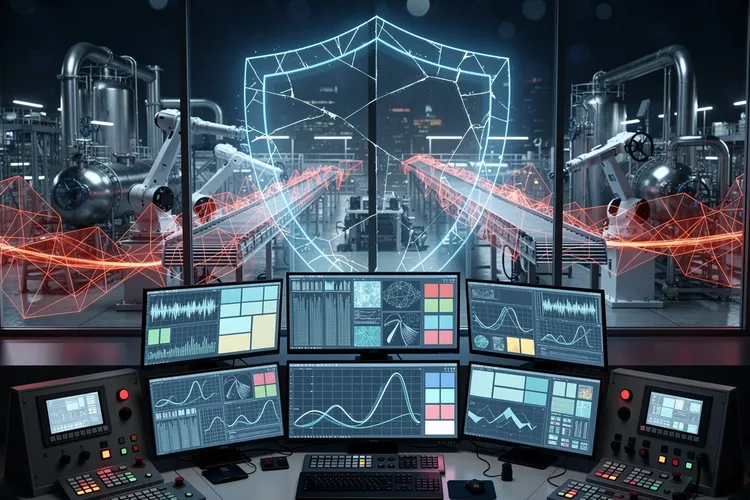
The Invisible Shield: Why Industrial Cybersecurity Still Can’t Quantify Its Worth to the Boardroom
Despite mounting threats to industrial control systems, OT cybersecurity teams face a persistent challenge: proving their value to executives when success means incidents that never happen. The struggle to quantify risk reduction in business terms leaves critical infrastructure chronically underprotected.

Data Scientist’s Trek: From Paris Courts to Australian Mineshafts
Simon Barres bridges labs and mines at QuantumBlack, deploying AI to optimize mining yields with sensor data and real-time models. His journey from Guadeloupe basketball to Amsterdam AI leadership highlights multidisciplinary impact in heavy industry.
The Cloud Security Paradox: Why Enterprise Spending Fails to Match the Growing Complexity Crisis
Despite substantial IT security budgets, cloud breaches continue escalating. New research reveals the root cause isn't insufficient spending but exponential structural complexity that outpaces security teams' management capabilities. AI simultaneously widens this gap while empowering sophisticated attackers at machine speed.
Inside Bitwise’s Audacious $6.5 Million Bitcoin Forecast: Why One CIO Sees Generational Wealth Creation Ahead
Bitwise CIO Matt Hougan projects Bitcoin could reach $6.5 million within 20 years, citing institutional adoption, central bank policies, and cryptocurrency's evolving role in global finance. His analysis extends beyond price speculation to examine regulatory developments, market cycles, and generational wealth transfer.
Former Ripple CTO’s $100 XRP Price Target Ignites Fierce Debate Among Digital Asset Investors
Former Ripple CTO David Schwartz's comments on XRP potentially reaching $100 have divided the cryptocurrency community, exposing tensions between technical possibility and market reality. The debate highlights challenges facing digital assets as they navigate regulatory uncertainty, adoption hurdles, and investor expectations.
Panera Bread’s 1.4 Million Record Data Breach Exposes Critical Vulnerabilities in Restaurant Chain Cybersecurity
Panera Bread faces a massive data breach exposing 1.4 million customer records, including names, emails, and addresses. The incident highlights critical cybersecurity vulnerabilities in the restaurant industry and raises urgent questions about consumer data protection.
Microsoft’s Windows 11 Credibility Crisis: Inside the Company’s Pledge to Rebuild User Confidence
Microsoft publicly acknowledges Windows 11's trust crisis, committing to prioritize reliability and fixes throughout 2026. The admission marks a rare moment of corporate vulnerability as the tech giant confronts user frustration over forced updates, compatibility issues, and perceived prioritization of monetization over functionality.
Saudi Healthcare Pioneer Alrajhi Medicine Bets Big on Oracle’s AI-Powered EHR Overhaul
Alrajhi Medicine partners with Oracle to deploy Health Foundation EHR and Fusion Cloud, pioneering unified digital health in Saudi Arabia's private sector for AI-enhanced care and efficiency.
Formae’s Multi-Cloud Leap: Platform Engineering Labs Arms Builders Against IaC Gridlock
Platform Engineering Labs' formae surges to multi-cloud with GCP, Azure, OCI, and OVH beta support plus a Plugin SDK, empowering infrastructure builders to extend IaC without vendor delays. This upgrade redefines extensibility in a fragmented cloud era.
Teradata’s AgentStack: Bridging AI Pilots to Production Autonomy
Teradata's Enterprise AgentStack unifies AI agent building, deployment, and governance across hybrid environments, targeting enterprises stuck in AI pilots. With components like AgentEngine and AgentOps, it promises secure, scalable autonomy backed by governed data.
Sky47’s Sovereign Surge: Pakistan’s Massive AI Cloud Bet
Sky47's January 2026 launch marks Pakistan's boldest sovereign cloud move, with 3,000 racks and 50MW for AI workloads. Backed by Mari Energies and Fauji Foundation, it eyes hyperscalers amid rising data sovereignty demands.
Ivanti’s Neurons Platform Pioneers Autonomous IT Operations Through Agentic AI Integration
Ivanti integrates agentic AI into its Neurons platform, enabling autonomous IT service management, endpoint security, and asset management. The customer preview launches Q1 2025, positioning the company at the forefront of autonomous IT operations amid growing industry adoption of AI agents.
InfoSec’s Broader Shield: Why It Outspans Cybersecurity in 2026’s Threat Surge
InfoSec broadly protects all data via the CIA triad, encompassing cybersecurity's digital focus amid AI phishing, ransomware, and skill shortages projected for 2026.
How Google’s Gemini AI Turned a Singapore Hackathon Into the Future of Software Development
A Singapore hackathon team's use of Google Gemini AI to rapidly build complex software demonstrates how artificial intelligence is transforming development economics, productivity, and the fundamental skills required of software engineers in an AI-augmented future.
Chainguard’s Zero-CVE Revolution: Taming Open Source Chaos for CIOs
Chainguard rebuilds open-source components from source to deliver zero-CVE images, freeing CIOs from 30-40% engineering time lost to triage while fortifying supply chains against malicious threats.
France’s Digital Sovereignty Push: How VPN Regulations Could Reshape European Internet Freedom
France's Interior Minister has announced VPNs are under evaluation following a social media ban for under-15s, raising concerns about digital privacy and internet freedom across Europe and potentially setting precedent for restrictive regulations.
How SAIC’s Mission Integration Strategy Could Transform Defense Technology Deployment
SAIC's chief technology officer Bob Ritchie advocates for mission integration to accelerate defense capability delivery, challenging traditional acquisition models. This approach emphasizes parallel development and deployment processes, modular architectures, and closer collaboration between contractors and warfighters to compress timelines from decades to months.
Olympic Ice Turns to Cyber Fire: Enterprises Brace for Milano Cortina Threats
Enterprises supporting Milano Cortina 2026 Olympics face escalated cyber risks from AI phishing, ransomware, and DDoS, building on Paris 2024's 140 incidents. Experts urge zero trust, external partners, and constant readiness amid regulatory threats like Cloudflare's dispute.
Federal Data Dragnet: How DHS Demands on Tech Giants Target Political Dissent in the Digital Age
The Department of Homeland Security is compelling major technology companies to surrender user data on Trump critics, raising profound questions about surveillance powers, corporate compliance, and First Amendment protections in the digital age. This unprecedented campaign targets political speech through National Security Letters and administrative subpoenas, creating tensions between national security claims and civil liberties.
How Cybersecurity Infrastructure Could Determine America’s AI Supremacy Over China
As the U.S.-China AI race intensifies, experts argue America's competitive edge lies not in algorithms alone, but in trustworthy, secure AI infrastructure. Cybersecurity excellence could prove more decisive than raw model performance in capturing global market share and defining AI leadership.
Subscribe Newsletter
Subscribe to our newsletter and stay up to date with the latest news, updates, and exclusive offers. Join our community today!
Google Cloud’s Leadership Shake-Up: Hayete Gallot’s Departure Signals Strategic Pivot in Enterprise Customer Relations
Google Cloud's Customer Experience President Hayete Gallot has departed after less than two years, signaling a potential strategic shift in how the cloud division approaches enterprise customer relations amid intense competition from AWS and Microsoft Azure.
SGS Bolsters Cybersecurity Arsenal With Panacea Infosec Acquisition in Strategic Digital Trust Expansion
SGS acquires India-based Panacea Infosec to strengthen digital trust and payment card security capabilities, marking a strategic expansion into cybersecurity services as the Swiss testing giant builds comprehensive digital assurance offerings for global enterprise clients.
Community First Banking Elevates Cybersecurity Posture with Strategic Leadership Appointment Amid Rising Financial Sector Threats
Community First Banking Company appoints Jon Hanshaw as Information Security Officer, reflecting the critical importance of cybersecurity leadership in community banking as institutions face escalating threats and regulatory pressures in an increasingly digital financial services environment.
SGS Pivots to Cybersecurity with Panacea Infosec Acquisition, Signaling Industry Consolidation in Testing and Certification Sector
Swiss testing giant SGS acquires New Delhi-based Panacea Infosec in strategic move to expand cybersecurity capabilities, reflecting broader industry transformation as traditional quality assurance firms race to address converged physical and digital risks in increasingly interconnected global markets.
Inside the CISO’s War Room: How Enterprise Security Chiefs Are Redefining Digital Defense for 2026
Chief information security officers are reshaping enterprise defense strategies around five critical priorities for 2026, including AI-driven security operations, zero trust architecture, supply chain security, cloud-native capabilities, and privacy compliance, while positioning security as a strategic business enabler rather than cost center.
Cloud’s Complexity Trap: How Tool Overload and AI-Wielding Attackers Are Fracturing Security Defenses
Fortinet's 2026 Cloud Security Report exposes a widening complexity gap in hybrid clouds, where tool sprawl, AI-driven attacks, and skills shortages overwhelm teams despite rising budgets. Nearly 70% cite fragmentation as the top barrier, urging platform shifts and MSSP aid.
Join Us
Share your perspective with confidence. Your experience could inform, inspire, and help someone live better.





