
IT Management
IT Management focuses on governance, security, infrastructure, and operations—helping teams run reliable systems, reduce risk, and align technology with business goals.
- Home
- IT Management
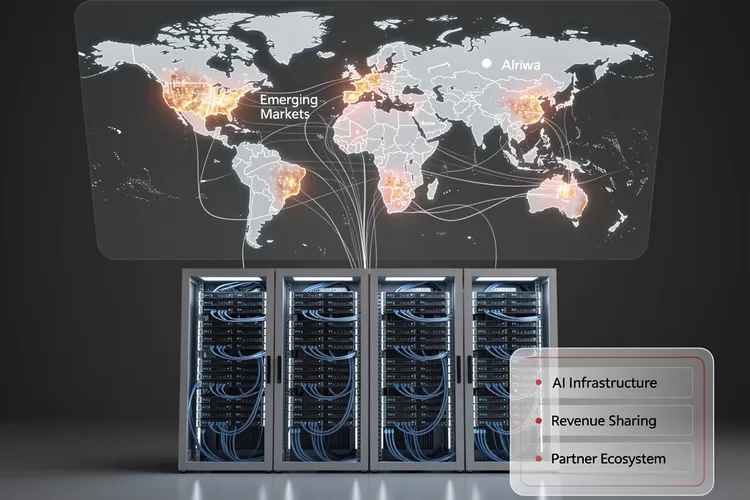
Inside Huawei Cloud’s Bold 2026 Partner Strategy: How Data Centers Become the Cornerstone of AI Infrastructure Expansion
Huawei Cloud's 2026 partner strategy positions data centers as strategic allies in AI infrastructure expansion, offering unprecedented revenue-sharing models and technical integration. The approach targets emerging markets with generous incentives while navigating geopolitical constraints and semiconductor restrictions.

Upwind’s Runtime Revolution: $250M Fuels $1.5B Cloud Security Unicorn
Upwind's $250 million Series B catapults it to $1.5 billion valuation, powering runtime-first cloud security amid 900% revenue surge. Backed by Bessemer and all-stars, the ex-Spot.io team targets AI-era threats for giants like Siemens and Roku.
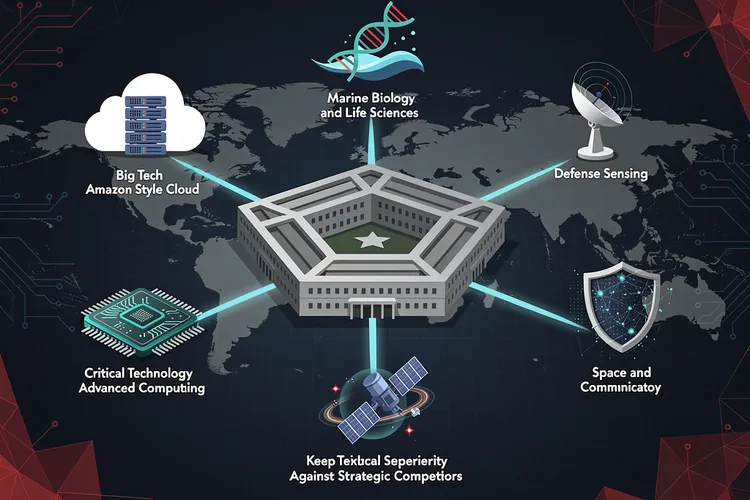
Pentagon’s New Technology Chiefs Signal Major Shift in Defense Innovation Strategy
The Pentagon's Chief Technology Officer has selected six defense technology veterans with diverse backgrounds—from Amazon executives to marine biologists—to lead Critical Technology Areas, signaling a major shift in how the Defense Department approaches innovation and maintains technological superiority against strategic competitors.
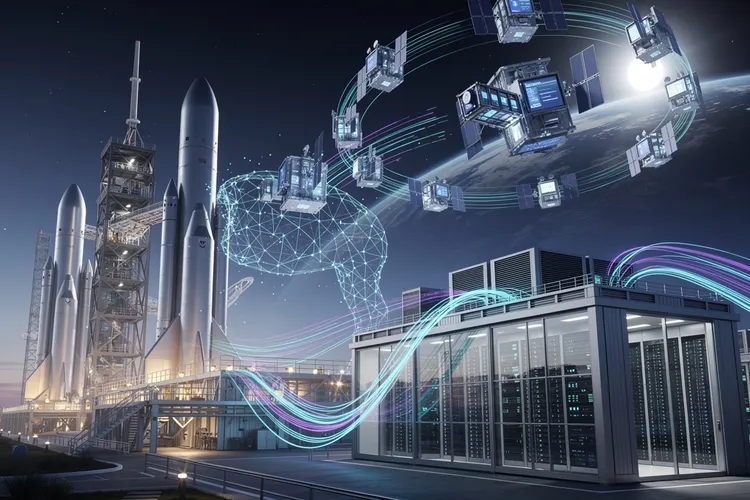
Inside Elon Musk’s Audacious Plan to Fuse Rockets and AI: The SpaceX-xAI Megamerger
Elon Musk is merging SpaceX and xAI in a deal combining an $800 billion rocket manufacturer with a $230 billion AI startup, advancing his vision of space-based data centers while consolidating his technological empire ahead of a planned summer IPO.

Verizon’s Subscriber Surge Signals Schulman’s Turnaround Triumph
Verizon crushed Q4 2025 expectations with 616,000 postpaid phone adds under CEO Dan Schulman, issuing bullish 2026 guidance post-Frontier acquisition. Revenue hit $36.4 billion, signaling a strategic revival amid fierce competition.
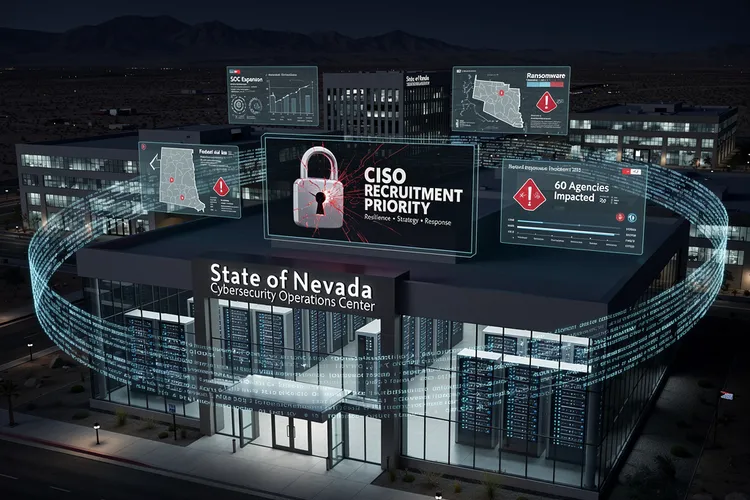
Nevada’s Urgent Hunt for a Cyber Sentinel After Ransomware Chaos
Nevada seeks a permanent CISO after 2025 ransomware chaos disrupted 60 agencies, stole data, and exposed gaps. The role demands strategy, response leadership amid SOC buildup and federal aid, signaling a hardened push for resilience.

How a Startup’s Unsecured Database Exposed the Fragility of AI Agent Platforms
Moltbook's completely exposed database allowed anyone to hijack AI agents on the platform, revealing how rapid AI deployment is outpacing basic cybersecurity practices. The incident highlights growing security debt in the AI startup ecosystem and regulatory gaps in governing autonomous agent platforms.
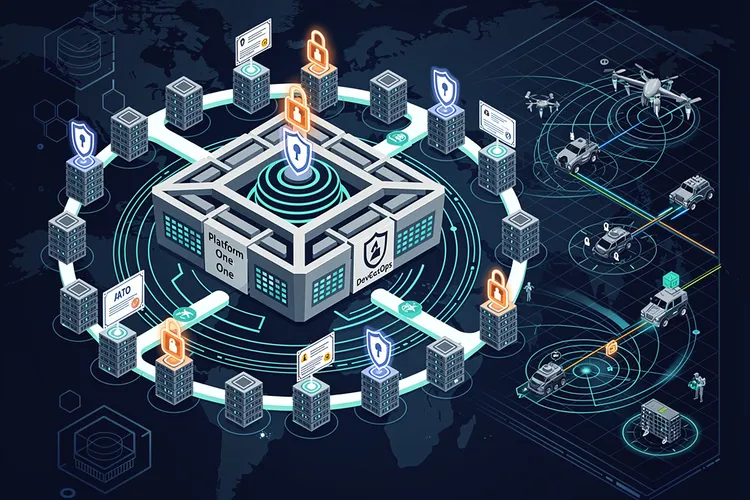
DevSecOps Arsenal: Pentagon’s Push for Warfighter Code at Warp Speed
The Pentagon's DevSecOps revolution integrates security into rapid software delivery, powering over 50 factories and slashing deployment times. From Platform One's secure pipelines to cATO approvals, it equips warfighters with resilient digital edge against evolving threats.
The Invisible Shield: Why Industrial Cybersecurity Still Can’t Quantify Its Worth to the Boardroom
Despite mounting threats to industrial control systems, OT cybersecurity teams face a persistent challenge: proving their value to executives when success means incidents that never happen. The struggle to quantify risk reduction in business terms leaves critical infrastructure chronically underprotected.

Data Scientist’s Trek: From Paris Courts to Australian Mineshafts
Simon Barres bridges labs and mines at QuantumBlack, deploying AI to optimize mining yields with sensor data and real-time models. His journey from Guadeloupe basketball to Amsterdam AI leadership highlights multidisciplinary impact in heavy industry.
Britain’s NHS Launches Revolutionary Cancer Gene Database, Granting Families Direct Access to Hereditary Risk Data
The NHS in England is launching a revolutionary cancer gene database allowing thousands of families direct access to hereditary risk information. This unprecedented initiative transforms how genetic cancer risk is communicated, potentially saving lives through enhanced screening and prevention for at-risk relatives.
When the Watchdog Stumbles: Inside the ChatGPT Security Breach That Exposed Federal Cybersecurity Vulnerabilities
The acting director of CISA allegedly uploaded sensitive government documents to ChatGPT, exposing critical vulnerabilities in federal AI adoption policies. This incident reveals systemic gaps in cybersecurity protocols as agencies struggle to balance innovation with national security requirements.
The Great Interface Erosion: Why AI Agents Are Poised to Devour Enterprise SaaS
A deep dive into how AI agents from Anthropic and strategies from JPMorgan are signaling the end of the traditional SaaS interface. As AI moves from chatbots to autonomous workers, the seat-based software model faces an existential threat, shifting value from the application layer to data and intelligence.
WhatsApp’s Enhanced Privacy Arsenal: How Meta’s Lockdown Mode Shields High-Risk Users From Digital Threats
WhatsApp's new Lockdown Mode transforms the messaging platform into a security fortress for high-risk users facing sophisticated cyber threats. The feature blocks unknown contacts, restricts media downloads, and implements comprehensive protections against state-sponsored attacks and advanced malware targeting vulnerable populations.
Britain’s Proposed VPN Age Verification System Sparks International Outcry and Technical Skepticism
The UK's proposed mandatory age verification for VPN services has triggered widespread criticism from privacy advocates, technology experts, and civil liberties organizations who argue the policy is technically unworkable and threatens fundamental digital rights while setting dangerous precedents for democratic internet regulation.
Microsoft’s PowerToys Experiment Signals Bold Rethinking of Windows 11 Interface Design
Microsoft is testing a macOS-style top menu bar for Windows 11 through PowerToys, marking a significant experiment in desktop interface design. This cautious approach to reimagining Windows' three-decade-old taskbar paradigm reflects lessons learned from past interface controversies.
Microsoft’s NTLM Retirement Marks End of Era for Three-Decade Authentication Protocol
Microsoft has begun phasing out NTLM authentication protocol after three decades, disabling it by default in Windows 11 Insider builds. This move forces enterprises to migrate to more secure authentication methods like Kerberos, addressing long-standing vulnerabilities that have enabled credential-based attacks.
Inside the Database Revolution: How Enterprise Data Management Transformed From Magnetic Tapes to AI-Powered Systems
From magnetic tapes to AI-powered cloud systems, databases have transformed from simple storage into sophisticated platforms managing billions of records. This deep dive explores how database technology evolved, the shift to cloud-native architectures, and emerging trends including vector databases and multimodel systems reshaping enterprise data management.
AI Agents Resurrect the Database Imperative
AI agents are forcing a database renaissance, prioritizing reliable infrastructure for real-time, verifiable data. Vector stores, contextual memory, and agent-native systems address scaling challenges, with forecasts signaling massive enterprise adoption by 2026.
Social Media’s Reckoning: Addiction Trials Target Tech Giants’ Designs
Landmark trials in California accuse Meta and YouTube of designing addictive apps that harmed young users' mental health. TikTok and Snap settled; bellwethers could force billions in changes or payouts.
Surfshark’s Browser Extension Pivots to Proactive Threat Detection as VPN Industry Embraces Preventive Security
Surfshark's new Search Guardian browser extension marks a strategic shift in VPN industry security approaches, warning users about dangerous websites before they click. This proactive threat detection represents an evolution beyond traditional reactive security models in response to sophisticated phishing attacks.
Vulnerability Exploitation Overtakes Phishing as Primary Attack Vector, Cisco Reports Amid Rising MFA Bypass Threats
Cisco's latest threat intelligence reveals vulnerability exploitation has surpassed phishing as the primary attack method in Q4 2024, forcing enterprises to fundamentally reassess security strategies. The shift includes rising MFA bypass techniques, demanding urgent changes in resource allocation and defensive priorities.
The Resource Divide: Why Information Security Commands Bigger Budgets Than Privacy Teams
Information security departments command substantial budgets and large teams while privacy functions operate with far fewer resources despite expanding regulatory demands. This persistent resource gap undermines data protection efforts and reflects outdated organizational priorities that leading companies are beginning to address through integrated approaches and strategic investment.
AI’s Privacy Imperative: Rebuilding Digital Trust on Data Privacy Day 2026
Data Privacy Day 2026 highlights AI's transformation of privacy into digital trust's cornerstone, amid cloud complexity gaps and governance gaps. Experts demand privacy-by-design as regulations tighten globally.
Why Open Document Format Represents More Than Just File Compatibility—It’s About Digital Sovereignty
The Open Document Format represents more than technical specifications—it embodies a philosophy of digital sovereignty, data longevity, and user freedom that challenges proprietary software dominance. As institutions worldwide grapple with long-term data accessibility, ODF's transparent architecture and open governance offer critical advantages.
Spain’s Digital Childhood Protection Act: Inside Europe’s Most Aggressive Social Media Age Restriction Framework
Spain implements Europe's strictest social media age restrictions, banning access for users under 16 and requiring sophisticated verification systems. The legislation raises complex questions about enforcement feasibility, privacy implications, and the balance between child protection and digital rights in an interconnected world.
Laboratory Medicine Enters the Algorithm Age: How ADLM’s Data Science Initiative Aims to Transform Diagnostic Testing
The Association for Diagnostics & Laboratory Medicine launches the first comprehensive data science educational program for laboratory professionals, addressing the critical skills gap as diagnostic facilities grapple with exponentially increasing data volumes from genomic sequencing, mass spectrometry, and digital pathology platforms.
State Technology Chiefs Push Washington for Unified Strategy on AI Governance and Cyber Defense
State chief information officers are calling for comprehensive federal support to address mounting challenges in artificial intelligence implementation and cybersecurity defense. NASCIO leads effort to secure coordinated assistance, arguing fragmented approaches create national vulnerabilities that require unified strategy and resource sharing.
Subscribe Newsletter
Subscribe to our newsletter and stay up to date with the latest news, updates, and exclusive offers. Join our community today!
The Code War: Inside the Pentagon’s Aggressive Shift to Offensive Cyber Operations
The Pentagon has shifted from reactive cyber defense to aggressive "Defend Forward" operations, treating code as a kinetic weapon. This deep dive explores the strategic pivot, the integration of AI, the friction with Silicon Valley, and the high-stakes shadow war currently waging across global critical infrastructure networks.
The Silent Crisis: How 175,000 Unsecured AI Servers Became a Global Security Liability
Over 175,000 Ollama AI servers are publicly exposed worldwide, creating unprecedented security risks. This investigation reveals how rapid AI adoption has outpaced security measures, leaving organizations vulnerable to data theft, model poisoning, and network compromise across 140 countries.
Inside Microsoft’s Copilot Crisis: How the Tech Giant’s AI Flagship Lost Its Way
Microsoft's Copilot chatbot, positioned as the cornerstone of its AI transformation, is losing users to competitors despite massive marketing investments. Data shows paid subscribers using Copilot as their primary option dropped from 18.8% to 11.5% while Google's Gemini gained ground, raising questions about the tech giant's AI strategy.
Inside the Federal Government’s Radical Plan to Transform Digital Services Through Unified Technology Standards
Federal CIO Greg Barbaccia unveils ambitious "one government" strategy to overhaul digital services through unified standards and shared platforms, prioritizing tangible outcomes over technical metrics in the most comprehensive federal IT transformation attempt in decades.
How Philip Payne’s AMIA Presidency Signals Healthcare AI’s Shift from Academic Theory to Clinical Reality
Philip Payne's election as AMIA president represents a critical juncture for medical informatics as artificial intelligence transforms from academic concept to clinical reality. His dual role bridging academic research and operational healthcare leadership positions him to address challenges from regulatory complexity to workforce development.
The Boardroom Reckoning: How Chief Security Officers Are Redefining Enterprise Defense in the Age of Autonomous Threats
Chief Information Security Officers face unprecedented challenges as artificial intelligence reshapes both cyber threats and defenses. From regulatory pressures to talent shortages, security leaders must balance innovation with risk management while translating technical concerns into business imperatives that resonate with boards and executives.
Join Us
Share your perspective with confidence. Your experience could inform, inspire, and help someone live better.





