
IT Management
IT Management focuses on governance, security, infrastructure, and operations—helping teams run reliable systems, reduce risk, and align technology with business goals.
- Home
- IT Management
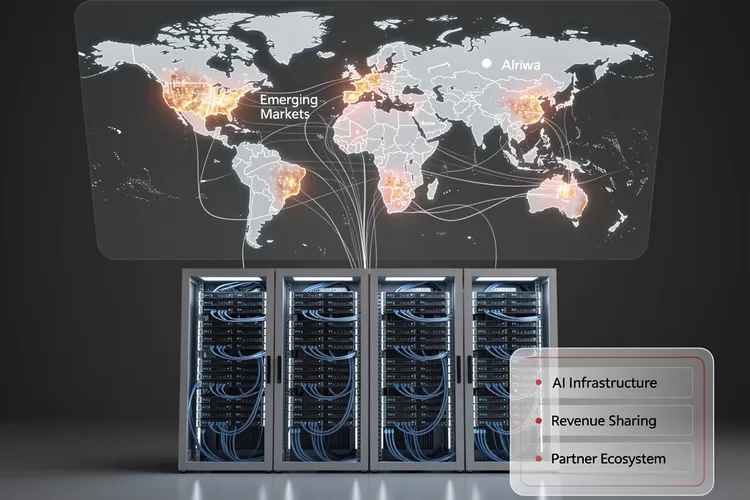
Inside Huawei Cloud’s Bold 2026 Partner Strategy: How Data Centers Become the Cornerstone of AI Infrastructure Expansion
Huawei Cloud's 2026 partner strategy positions data centers as strategic allies in AI infrastructure expansion, offering unprecedented revenue-sharing models and technical integration. The approach targets emerging markets with generous incentives while navigating geopolitical constraints and semiconductor restrictions.

Upwind’s Runtime Revolution: $250M Fuels $1.5B Cloud Security Unicorn
Upwind's $250 million Series B catapults it to $1.5 billion valuation, powering runtime-first cloud security amid 900% revenue surge. Backed by Bessemer and all-stars, the ex-Spot.io team targets AI-era threats for giants like Siemens and Roku.
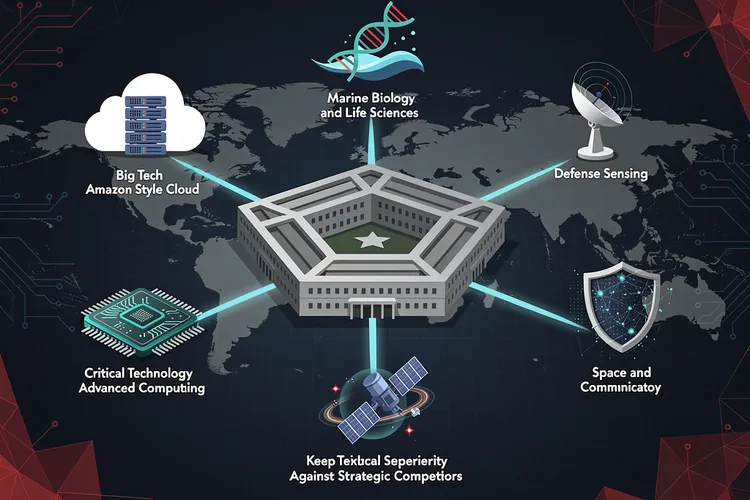
Pentagon’s New Technology Chiefs Signal Major Shift in Defense Innovation Strategy
The Pentagon's Chief Technology Officer has selected six defense technology veterans with diverse backgrounds—from Amazon executives to marine biologists—to lead Critical Technology Areas, signaling a major shift in how the Defense Department approaches innovation and maintains technological superiority against strategic competitors.
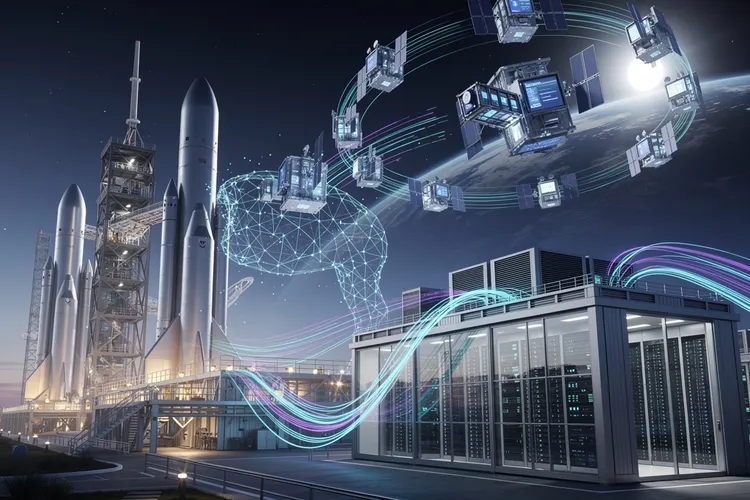
Inside Elon Musk’s Audacious Plan to Fuse Rockets and AI: The SpaceX-xAI Megamerger
Elon Musk is merging SpaceX and xAI in a deal combining an $800 billion rocket manufacturer with a $230 billion AI startup, advancing his vision of space-based data centers while consolidating his technological empire ahead of a planned summer IPO.

Verizon’s Subscriber Surge Signals Schulman’s Turnaround Triumph
Verizon crushed Q4 2025 expectations with 616,000 postpaid phone adds under CEO Dan Schulman, issuing bullish 2026 guidance post-Frontier acquisition. Revenue hit $36.4 billion, signaling a strategic revival amid fierce competition.
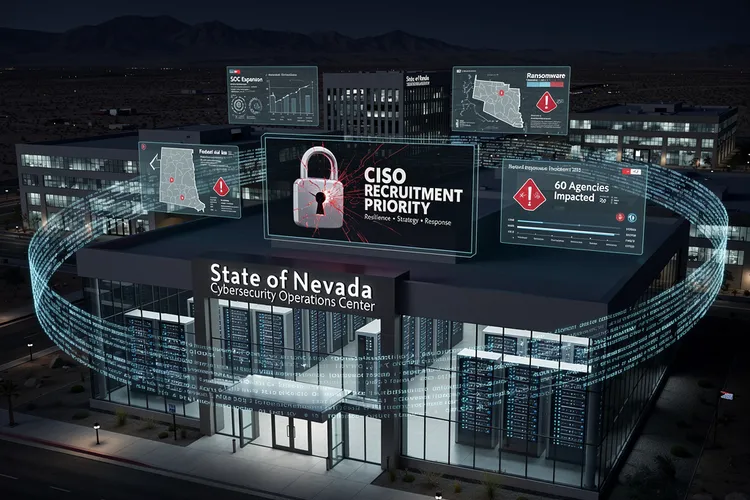
Nevada’s Urgent Hunt for a Cyber Sentinel After Ransomware Chaos
Nevada seeks a permanent CISO after 2025 ransomware chaos disrupted 60 agencies, stole data, and exposed gaps. The role demands strategy, response leadership amid SOC buildup and federal aid, signaling a hardened push for resilience.

How a Startup’s Unsecured Database Exposed the Fragility of AI Agent Platforms
Moltbook's completely exposed database allowed anyone to hijack AI agents on the platform, revealing how rapid AI deployment is outpacing basic cybersecurity practices. The incident highlights growing security debt in the AI startup ecosystem and regulatory gaps in governing autonomous agent platforms.
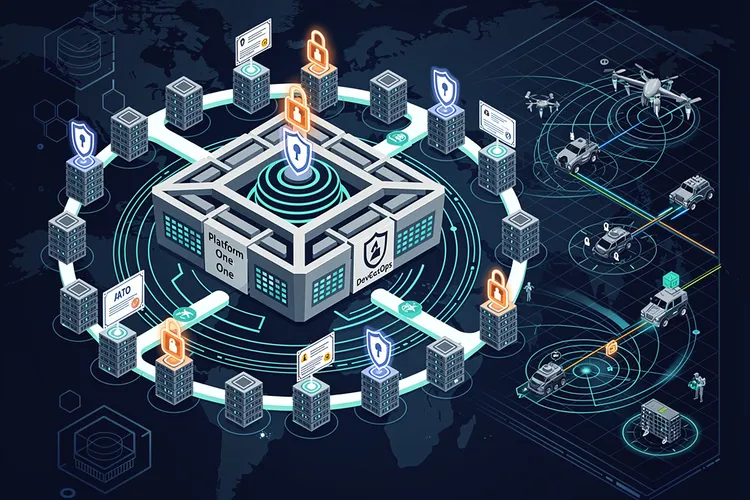
DevSecOps Arsenal: Pentagon’s Push for Warfighter Code at Warp Speed
The Pentagon's DevSecOps revolution integrates security into rapid software delivery, powering over 50 factories and slashing deployment times. From Platform One's secure pipelines to cATO approvals, it equips warfighters with resilient digital edge against evolving threats.
The Invisible Shield: Why Industrial Cybersecurity Still Can’t Quantify Its Worth to the Boardroom
Despite mounting threats to industrial control systems, OT cybersecurity teams face a persistent challenge: proving their value to executives when success means incidents that never happen. The struggle to quantify risk reduction in business terms leaves critical infrastructure chronically underprotected.

Data Scientist’s Trek: From Paris Courts to Australian Mineshafts
Simon Barres bridges labs and mines at QuantumBlack, deploying AI to optimize mining yields with sensor data and real-time models. His journey from Guadeloupe basketball to Amsterdam AI leadership highlights multidisciplinary impact in heavy industry.
The Data Management Revolution: How Enterprise Leaders Are Ditching Legacy Systems for AI-Ready Infrastructure
Enterprise data management is undergoing its most significant transformation in decades. IT leaders are abandoning legacy warehouses and batch processing for AI-ready, cloud-native architectures that enable real-time analytics, self-service access, and machine learning at scale.
Google Dismantles IPidea’s Global Proxy Network in Unprecedented Cybercrime Crackdown
Google has dismantled IPidea's massive residential proxy network, removing millions of compromised devices in an unprecedented operation. The action marks a significant shift in how tech companies combat cybercrime infrastructure, disrupting one of the world's largest networks enabling credential stuffing, fraud, and malicious activities.
The Collision Course: How Agentic AI Forces InfoSec and SaaS Teams to Rethink Enterprise Data Protection
As autonomous AI agents gain decision-making power across SaaS platforms, the traditional divide between information security and SaaS administration has become a critical vulnerability. Organizations must rethink access controls, data recovery, and compliance frameworks designed for human actors to accommodate machine intelligence operating at unprecedented speed and scale.
CTOs’ High-Wire Act: Taming AI Speed, Cyber Threats and Talent Crunch
Chief technology officers grapple with AI acceleration, cyber threats, legacy integration and talent shortages amid breakneck tech shifts. Strategic upskilling, agile architectures and data-driven priorities help them deliver value without disruption.
Balaji’s Warning: Silicon Valley’s Zero Hour and Crypto’s Rise
Balaji Srinivasan predicts Silicon Valley's collapse under California's billionaire tax, with crypto protocols rising as resilient successors. Political risks and decentralization trends threaten the VC model, forcing a global tech realignment.
How South African Enterprises Are Breaking Through AI Infrastructure Barriers With Cross-Border Cloud Architecture
South African enterprises are overcoming AI infrastructure limitations through Amazon Bedrock's cross-Region inference architecture, accessing Anthropic's Claude 4.5 models with minimal latency while dynamically routing requests across continents. This breakthrough enables emerging markets to deploy frontier AI capabilities previously restricted to established cloud regions.
The ClawdBot Heist: How Anthropic’s AI Assistant Became an Unwitting Accomplice in Cryptocurrency Theft
Security researchers have uncovered ClawdBot, a sophisticated attack that exploits Anthropic's Claude AI to steal cryptocurrency by manipulating the Model Context Protocol integration. The technique represents a new category of AI-mediated theft that challenges existing security frameworks.
Sophisticated Apple Pay Phishing Scheme Exploits User Trust Through Multi-Channel Attack Vector
A sophisticated multi-channel phishing campaign is targeting Apple Pay users through coordinated text messages, phone calls, and fraudulent websites. The operation exploits user trust in Apple's brand and payment platform, representing an evolution in social engineering tactics that security experts warn poses significant risks to digital payment security.
Google’s $135 Million Android Settlement Exposes the Hidden Cost of Location Data Collection
Google's $135 million settlement with 40 states exposes systematic location tracking of Android users who disabled privacy settings. The multistate investigation revealed Google continued harvesting location data through backdoor methods between 2014-2019, raising fundamental questions about user consent and corporate accountability in digital privacy.
Why the GeForce GTX 1650 Refuses to Die: Inside the Economics of Budget Gaming’s Most Resilient Graphics Card
The Nvidia GeForce GTX 1650, released in 2019, continues dominating budget gaming markets worldwide with accelerating popularity. This aging GPU's persistence reveals fundamental shifts in consumer behavior, global economics, and the widening gap between enthusiast expectations and mainstream gaming needs.
How Machine Learning and Genomic Data Are Reshaping Drug Discovery at MIT’s Schmidt Center
MIT Professor Caroline Uhler describes how the Eric and Wendy Schmidt Center is leveraging machine learning and genomic data to transform drug discovery and personalized medicine, marking a fundamental shift from hypothesis-driven to data-driven biomedical research.
Oracle’s 26ai Unlocks AI Power for On-Prem Data Centers
Oracle's AI Database 26ai hits general availability for on-premises Linux x86-64, packing vector search, agentic AI, quantum encryption, and seamless upgrades from 19c. Features unify multimodal data querying, rivaling cloud silos while prioritizing security and sovereignty.
Pennsylvania’s Digital Sovereignty Play: How Alerify and Zadara Are Building America’s AI Infrastructure Fortress
Pennsylvania data center provider Alerify's partnership with AI cloud specialist Zadara signals a strategic shift toward sovereign AI infrastructure, offering enterprises localized computing capabilities that address mounting data residency and regulatory compliance concerns in artificial intelligence deployment.
The MongoDB Extortion Crisis: How Cybercriminals Are Exploiting Database Vulnerabilities to Ransom Corporate Data
A sophisticated wave of cyberattacks targeting MongoDB databases has emerged as a critical security threat in 2024. Attackers exploit misconfigurations to delete databases and demand ransoms, affecting thousands of instances. Organizations face cascading costs beyond ransom payments, including regulatory fines and operational disruption.
Telecom’s Secrets Shield: How Prevention-First Detection Reshapes Enterprise Security at Scale
Orange Business cut secret leaks 80% using GitGuardian's prevention-first hooks, setting a telecom blueprint for enterprises facing NIS2 rules and developer-scale sprawl. Precision detection under 5% false positives drives adoption and compliance.
Security Breach Exposes Critical Vulnerability in MoltBot Data Infrastructure: How One Click Could Compromise Enterprise Systems
A critical one-click remote code execution vulnerability in MoltBot infrastructure threatens enterprise data security, allowing attackers to steal sensitive information and cryptographic keys through minimal user interaction, highlighting growing risks in automated systems deployment.
LinkedIn’s AI Verification Push Signals Shift in Professional Credentialing as Platform Battles Skills Inflation
LinkedIn introduces AI-powered coding verification badges to combat skills inflation and help employers identify genuine technical expertise. The move signals a broader shift toward platform-based credentialing that could reshape professional certification markets and challenge traditional education's role in validating competence.
Forging Finance-Grade AI Analysts for Revenue Precision
Enterprises pilot AI data analysts for revenue insights, but finance insists on statutory-grade controls amid $12.9 million data quality losses yearly. Semantic layers, policy engines, and human gates forge trust, slashing close times via governed architectures.
Subscribe Newsletter
Subscribe to our newsletter and stay up to date with the latest news, updates, and exclusive offers. Join our community today!
Sophos Workspace Protection: Browser-First Shield for Hybrid Work and AI Risks
Sophos Workspace Protection reimagines hybrid security via a browser-centric model, governing AI use and slashing SASE complexity. Powered by Island, it bundles ZTNA, DNS filtering, and data controls for distributed workforces.
Inside the CNAPP Revolution: How Security Platforms Are Reshaping Enterprise Cloud Defense Strategy
Cloud Native Application Protection Platforms are transforming enterprise security by consolidating fragmented tools into unified solutions that protect applications from development through production, offering comprehensive visibility and control across multi-cloud environments while addressing the operational and economic challenges of traditional security approaches.
The Arms Race Intensifies: How AI Systems Are Revolutionizing Cybersecurity Vulnerability Detection
Artificial intelligence systems are demonstrating unprecedented capabilities in identifying and exploiting software vulnerabilities, fundamentally altering cybersecurity dynamics. This development creates both powerful defensive tools and potent offensive weapons, raising critical questions about the future of digital security.
The Silent Crisis: Why Most Healthcare Organizations Still Fail to Encrypt Patient Data at Rest
Healthcare organizations continue storing patient data unencrypted despite mounting cyber threats and regulatory pressure. This systemic failure exposes millions to data breaches, stemming from legacy systems, budget constraints, and misunderstood compliance requirements that prioritize checkboxes over genuine security.
The New Math of Cyber Defense: How Threat Intelligence Is Reshaping CISO Strategy for 2026
CISOs face critical strategic decisions in 2026 as actionable threat intelligence delivers 58% more detections, 30% fewer escalations, and 21-minute response times. Organizations must prioritize contextualized intelligence, automate response workflows, and align security with business continuity to prevent costly downtime.
The Invisible War: How Machine Learning Obscures Modern Payment Fraud From Detection Algorithms
As fraudsters deploy AI to mimic legitimate customer behavior, traditional fraud detection methods face obsolescence. The challenge isn't rising fraud rates—it's that fraudulent transactions have become statistically indistinguishable from authentic ones, forcing payments companies to fundamentally rethink defensive strategies beyond conventional pattern recognition.
Join Us
Share your perspective with confidence. Your experience could inform, inspire, and help someone live better.





