
IT Management
IT Management focuses on governance, security, infrastructure, and operations—helping teams run reliable systems, reduce risk, and align technology with business goals.
- Home
- IT Management
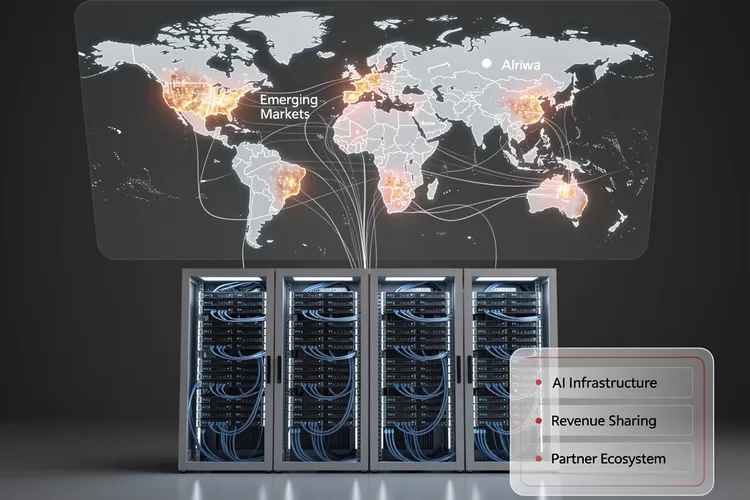
Inside Huawei Cloud’s Bold 2026 Partner Strategy: How Data Centers Become the Cornerstone of AI Infrastructure Expansion
Huawei Cloud's 2026 partner strategy positions data centers as strategic allies in AI infrastructure expansion, offering unprecedented revenue-sharing models and technical integration. The approach targets emerging markets with generous incentives while navigating geopolitical constraints and semiconductor restrictions.

Upwind’s Runtime Revolution: $250M Fuels $1.5B Cloud Security Unicorn
Upwind's $250 million Series B catapults it to $1.5 billion valuation, powering runtime-first cloud security amid 900% revenue surge. Backed by Bessemer and all-stars, the ex-Spot.io team targets AI-era threats for giants like Siemens and Roku.
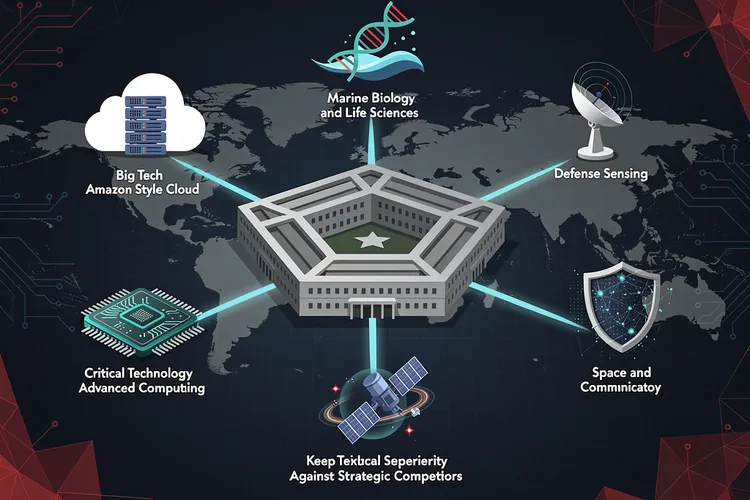
Pentagon’s New Technology Chiefs Signal Major Shift in Defense Innovation Strategy
The Pentagon's Chief Technology Officer has selected six defense technology veterans with diverse backgrounds—from Amazon executives to marine biologists—to lead Critical Technology Areas, signaling a major shift in how the Defense Department approaches innovation and maintains technological superiority against strategic competitors.
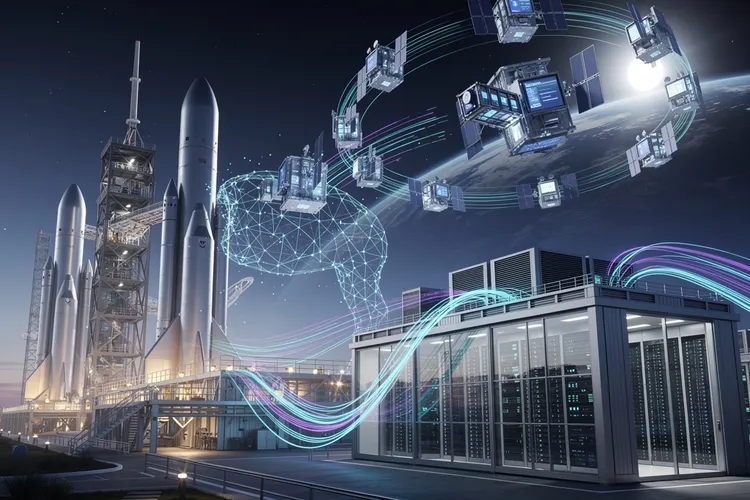
Inside Elon Musk’s Audacious Plan to Fuse Rockets and AI: The SpaceX-xAI Megamerger
Elon Musk is merging SpaceX and xAI in a deal combining an $800 billion rocket manufacturer with a $230 billion AI startup, advancing his vision of space-based data centers while consolidating his technological empire ahead of a planned summer IPO.

Verizon’s Subscriber Surge Signals Schulman’s Turnaround Triumph
Verizon crushed Q4 2025 expectations with 616,000 postpaid phone adds under CEO Dan Schulman, issuing bullish 2026 guidance post-Frontier acquisition. Revenue hit $36.4 billion, signaling a strategic revival amid fierce competition.
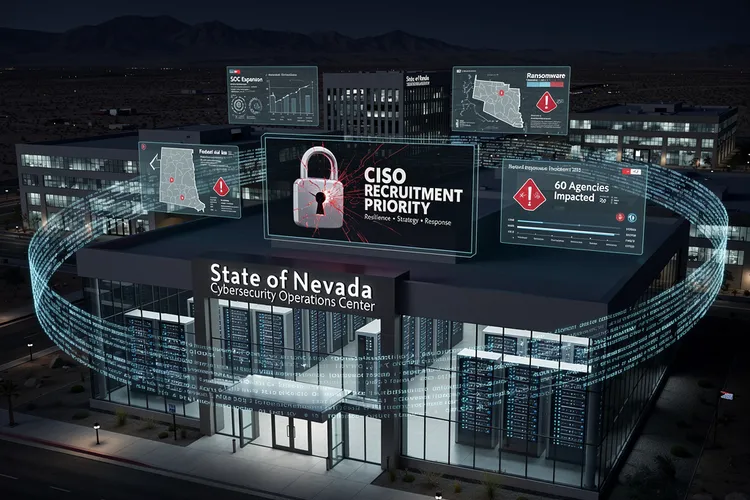
Nevada’s Urgent Hunt for a Cyber Sentinel After Ransomware Chaos
Nevada seeks a permanent CISO after 2025 ransomware chaos disrupted 60 agencies, stole data, and exposed gaps. The role demands strategy, response leadership amid SOC buildup and federal aid, signaling a hardened push for resilience.

How a Startup’s Unsecured Database Exposed the Fragility of AI Agent Platforms
Moltbook's completely exposed database allowed anyone to hijack AI agents on the platform, revealing how rapid AI deployment is outpacing basic cybersecurity practices. The incident highlights growing security debt in the AI startup ecosystem and regulatory gaps in governing autonomous agent platforms.
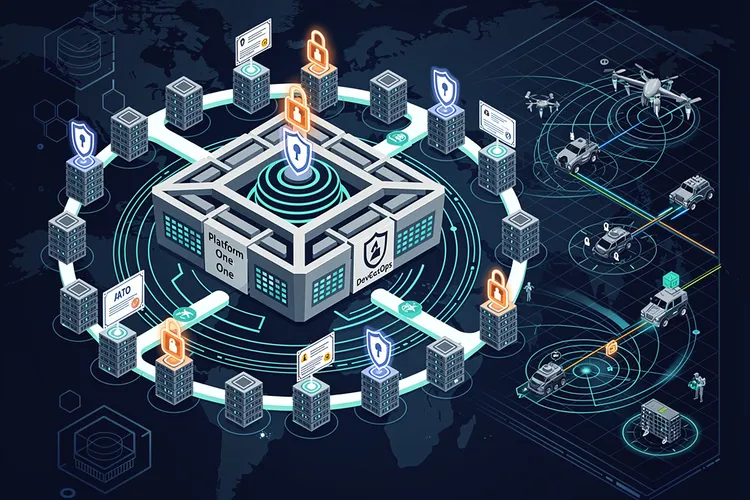
DevSecOps Arsenal: Pentagon’s Push for Warfighter Code at Warp Speed
The Pentagon's DevSecOps revolution integrates security into rapid software delivery, powering over 50 factories and slashing deployment times. From Platform One's secure pipelines to cATO approvals, it equips warfighters with resilient digital edge against evolving threats.
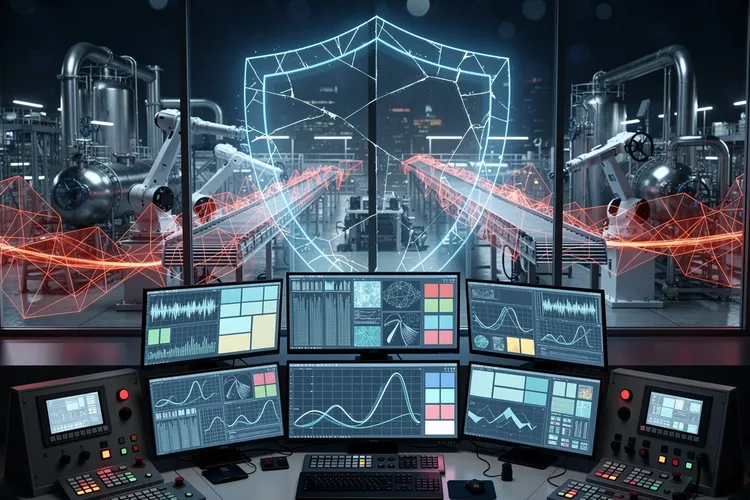
The Invisible Shield: Why Industrial Cybersecurity Still Can’t Quantify Its Worth to the Boardroom
Despite mounting threats to industrial control systems, OT cybersecurity teams face a persistent challenge: proving their value to executives when success means incidents that never happen. The struggle to quantify risk reduction in business terms leaves critical infrastructure chronically underprotected.

Data Scientist’s Trek: From Paris Courts to Australian Mineshafts
Simon Barres bridges labs and mines at QuantumBlack, deploying AI to optimize mining yields with sensor data and real-time models. His journey from Guadeloupe basketball to Amsterdam AI leadership highlights multidisciplinary impact in heavy industry.
The Fragmentation Revolution: How Distributed Cloud Networking Is Reshaping Enterprise Infrastructure
The unified cloud vision is fracturing as distributed cloud networking emerges to address AI workloads, data sovereignty requirements, and edge computing demands. This architectural shift represents a fundamental reimagining of enterprise infrastructure across public, private, neocloud, sovereign, and edge environments.
Oracle’s $50 Billion AI Infrastructure Gambit Signals Seismic Shift in Enterprise Cloud Computing
Oracle's unprecedented $50 billion investment in AI infrastructure represents a fundamental strategic shift for the enterprise software giant, positioning it to compete with hyperscale cloud providers in the rapidly expanding market for artificial intelligence workloads and specialized computing resources.
Google’s Domain Strike Dismantles Chinese Proxy Empire Fueling Kimwolf Botnet Menace
Google seized Ipidea domains in a court-ordered takedown, severing nine million devices from a Chinese proxy network tied to the massive Kimwolf botnet and BadBox threats, exposing risks to homes, firms, and governments worldwide.
Docker’s AI Assistant Vulnerability Exposes Critical Security Flaws in Containerization Platform
Docker has patched a critical vulnerability in its Ask Gordon AI assistant that could have allowed attackers to execute arbitrary code through prompt injection. The flaw highlights growing security concerns as companies integrate AI into enterprise infrastructure tools.
The Death of the Perimeter: Why Identity-Based Security Is Replacing Traditional Firewalls
Traditional perimeter defenses are becoming obsolete as organizations shift to identity-based security models. The new paradigm verifies user identity continuously rather than granting trust based on network location, fundamentally transforming how enterprises protect assets in an era of remote work and cloud computing.
How Data Scientists Are Rewriting the Rules of Modern Medicine
Data science is transforming medicine through AI-powered diagnostics, predictive analytics, and accelerated drug discovery. Healthcare data scientists earning up to $165,000 annually are building algorithms that detect diseases earlier, personalize treatments, and reshape clinical practice across hospitals and pharmaceutical companies nationwide.
WhatsApp’s Privacy Promise Under Federal Scrutiny After Whistleblower Allegations Surface
Federal whistleblower complaints allege WhatsApp's end-to-end encryption may not protect user privacy as advertised, raising questions about Meta's security claims and potentially exposing the company to regulatory scrutiny affecting its two billion global users.
When Privacy Havens Fail: Why PrivadoVPN Is Abandoning Switzerland’s Data Protection Framework
PrivadoVPN's decision to leave Switzerland challenges the notion of permanent privacy havens, as even traditionally protective jurisdictions face mounting international pressure. The move signals a broader industry shift toward jurisdictional arbitrage and raises critical questions about where VPN providers can genuinely protect user data.
California’s Delete Act Promises Privacy Revolution, Yet Implementation Reveals Deeper Cybersecurity Challenges
California's Delete Act enables residents to request deletion of personal data from hundreds of brokers with one click, but implementation reveals significant gaps in privacy protection and enforcement challenges that may require more comprehensive regulatory solutions.
The Pocket-Sized Linux Recovery Tool Reshaping Enterprise IT Disaster Response
Ventoy, an open-source bootable USB creation tool, has revolutionized enterprise IT disaster recovery by allowing multiple operating systems and utilities on a single device. Unlike traditional tools requiring reformatting for each OS, Ventoy enables simple ISO file copying, transforming system recovery approaches for IT professionals worldwide.
Sleep’s Silent Warnings: Stanford AI Foresees 130 Diseases from One Night
Stanford's SleepFM AI analyzes one night's polysomnography to predict risks for 130 diseases like Parkinson's, cancers, and heart conditions years ahead, using multimodal signals and achieving C-indices up to 0.89.
Join Us
Share your perspective with confidence. Your experience could inform, inspire, and help someone live better.





