- Home
- IT Management
Why Linux Mint Could Be Your Escape Route From Windows 11’s Growing Pains
As Windows 11's restrictive requirements and intrusive practices drive users to seek alternatives, Linux Mint emerges as the ideal transition platform. With its familiar interface, robust software compatibility, and respect for user autonomy, Mint offers Windows refugees a compelling escape route.
The Enterprise AI Power Struggle: How Anthropic’s Claude is Challenging OpenAI’s Dominance in Corporate America
A survey of Global 2000 companies reveals OpenAI leads with 78% CIO adoption, but Anthropic's rapid rise to 44% signals a fundamental shift in enterprise AI strategy as organizations embrace multi-model approaches and prioritize safety and compliance.
Inside Canada Computers’ Security Breach: A Forensic Analysis of Retail Technology Vulnerabilities
Canada Computers & Electronics disclosed a significant data breach exposing customer names, email addresses, billing information, and partial payment data. The incident highlights persistent cybersecurity vulnerabilities among mid-sized technology retailers operating with constrained security resources while facing sophisticated threats.
France’s Digital Sovereignty Push: How VPN Regulations Could Reshape European Internet Freedom
France's Interior Minister has announced VPNs are under evaluation following a social media ban for under-15s, raising concerns about digital privacy and internet freedom across Europe and potentially setting precedent for restrictive regulations.
Tulsa Airport Breach Exposes Critical Infrastructure Vulnerabilities as Russian Ransomware Group Claims Responsibility
Russian ransomware hackers allegedly breached Tulsa International Airport's systems, dumping private operational files online as proof of infiltration. The attack highlights growing vulnerabilities in regional transportation infrastructure and raises urgent questions about cybersecurity preparedness across American airports.
America’s Fiber Optic Buildout Stalls as Skilled Workers Vanish from the Grid
America's ambitious broadband expansion faces an unexpected obstacle: a critical shortage of skilled fiber optic technicians. Despite billions in federal funding and soaring wages, the telecommunications industry cannot find enough workers to install networks, threatening to derail rural connectivity goals.
Windows 11’s Desktop Catastrophe: How a Critical Bug Paralyzed User Interfaces and What Microsoft’s Response Reveals About Modern OS Fragility
A critical Windows 11 bug has rendered desktop environments completely unusable for thousands of users worldwide, exposing vulnerabilities in Microsoft's quality assurance processes and raising serious questions about operating system reliability in enterprise environments.
How Cybercriminals Weaponized Hugging Face’s AI Platform to Deploy Android Banking Trojans at Scale
Cybercriminals exploited Hugging Face's trusted AI platform to distribute Android banking trojans at scale, revealing how threat actors weaponize legitimate machine learning infrastructure. The sophisticated campaign bypassed traditional security measures by leveraging the platform's reputation to deliver malware targeting financial credentials and authentication systems across multiple continents.
Microsoft’s NTLM Retirement Marks End of Era for Three-Decade Authentication Protocol
Microsoft has begun phasing out NTLM authentication protocol after three decades, disabling it by default in Windows 11 Insider builds. This move forces enterprises to migrate to more secure authentication methods like Kerberos, addressing long-standing vulnerabilities that have enabled credential-based attacks.
OpenClaw Vulnerability Exposes AI Coding Assistants to Single-Click Remote Code Execution
The OpenClaw vulnerability in AI coding assistants enables one-click remote code execution, exposing millions of developers to sophisticated attacks. The flaw exploits trust relationships between programmers and AI tools, turning productivity enhancers into potential attack vectors with far-reaching supply chain implications.
OpenText’s Strategic Retreat: $150 Million Vertica Sale Signals Debt-Driven Portfolio Restructuring
OpenText sells Vertica analytics database to Rocket Software for $150 million, marking its second major divestiture in five months as the Canadian enterprise software giant pursues aggressive debt reduction following years of acquisition-driven expansion.
The MongoDB Extortion Crisis: How Cybercriminals Are Exploiting Database Vulnerabilities to Ransom Corporate Data
A sophisticated wave of cyberattacks targeting MongoDB databases has emerged as a critical security threat in 2024. Attackers exploit misconfigurations to delete databases and demand ransoms, affecting thousands of instances. Organizations face cascading costs beyond ransom payments, including regulatory fines and operational disruption.
Surfshark’s Browser Extension Pivots to Proactive Threat Detection as VPN Industry Embraces Preventive Security
Surfshark's new Search Guardian browser extension marks a strategic shift in VPN industry security approaches, warning users about dangerous websites before they click. This proactive threat detection represents an evolution beyond traditional reactive security models in response to sophisticated phishing attacks.
Microsoft’s Delicate Dance: How Redmond Balances Legacy Software Revenue With Cloud Ambitions
Microsoft has mastered the art of balancing traditional software revenue with aggressive cloud expansion, creating a hybrid strategy that outmaneuvers competitors who chose more binary paths. This approach offers crucial lessons for technology incumbents navigating disruptive transitions.
Oracle’s $50 Billion AI Infrastructure Gambit Signals Seismic Shift in Enterprise Cloud Computing
Oracle's unprecedented $50 billion investment in AI infrastructure represents a fundamental strategic shift for the enterprise software giant, positioning it to compete with hyperscale cloud providers in the rapidly expanding market for artificial intelligence workloads and specialized computing resources.
Microsoft’s Windows 11 Credibility Crisis: Why Users Are Rejecting Promises of Reform
Microsoft faces unprecedented skepticism from Windows 11 users after years of controversial updates and aggressive AI integration. Recent promises to fix the operating system and scale back unwanted features have been met with cynicism, revealing a fundamental trust deficit.
How a Typosquatting Campaign Exploited Open VSX Registry to Compromise Developer Environments
A sophisticated supply chain attack targeting the Open VSX Registry exploited typosquatted extensions to compromise developer environments, revealing critical vulnerabilities in open-source infrastructure. The campaign demonstrates how threat actors increasingly exploit trust relationships within developer tool ecosystems to infiltrate software development pipelines.
Inside ClawdBot: How One Developer’s Weekend Project Became Silicon Valley’s Most Obsessive AI Experiment
Peter Steinberger's ClawdBot experiment reveals both the promise and pitfalls of AI-driven software development. His transparent approach to autonomous coding agents offers crucial insights into endless optimization loops, technical decision-making, and the essential role of human judgment in development.
How Google’s Gemini AI Turned a Singapore Hackathon Into the Future of Software Development
A Singapore hackathon team's use of Google Gemini AI to rapidly build complex software demonstrates how artificial intelligence is transforming development economics, productivity, and the fundamental skills required of software engineers in an AI-augmented future.
Palantir’s Explosive Growth Signals New Era of AI Dominance in Government and Enterprise Markets
Palantir Technologies delivered fourth-quarter revenue of $1.41 billion, crushing Wall Street estimates with 70% year-over-year growth. The AI software firm's aggressive 2026 guidance projects revenue reaching $7.19 billion, substantially exceeding analyst expectations, while net income surged eight-fold to $608 million, demonstrating sustainable profitability amid broader market concerns about AI valuations.
Related

Formae’s Multi-Cloud Leap: Platform Engineering Labs Arms Builders Against IaC Gridlock
Platform Engineering Labs' formae surges to multi-cloud with GCP, Azure, OCI, and OVH beta support plus a Plugin SDK, empowering infrastructure builders to extend IaC without vendor delays. This upgrade redefines extensibility in a fragmented cloud era.

Sky47’s Sovereign Surge: Pakistan’s Massive AI Cloud Bet
Sky47's January 2026 launch marks Pakistan's boldest sovereign cloud move, with 3,000 racks and 50MW for AI workloads. Backed by Mari Energies and Fauji Foundation, it eyes hyperscalers amid rising data sovereignty demands.

Cloud’s Complexity Trap: How Tool Overload and AI-Wielding Attackers Are Fracturing Security Defenses
Fortinet's 2026 Cloud Security Report exposes a widening complexity gap in hybrid clouds, where tool sprawl, AI-driven attacks, and skills shortages overwhelm teams despite rising budgets. Nearly 70% cite fragmentation as the top barrier, urging platform shifts and MSSP aid.
IT Management
NordVPN’s Sixth Consecutive Audit Validates Zero-Logs Promise as Privacy Scrutiny Intensifies
NordVPN completes its sixth consecutive independent audit by Deloitte, confirming its zero-logs policy amid intensifying privacy scrutiny. The verification highlights industry trends toward verifiable transparency as regulatory pressure mounts and consumer skepticism grows regarding VPN privacy claims.
IT Management
Upwind’s Runtime Revolution: $250M Fuels $1.5B Cloud Security Unicorn
Upwind's $250 million Series B catapults it to $1.5 billion valuation, powering runtime-first cloud security amid 900% revenue surge. Backed by Bessemer and all-stars, the ex-Spot.io team targets AI-era threats for giants like Siemens and Roku.
IT Management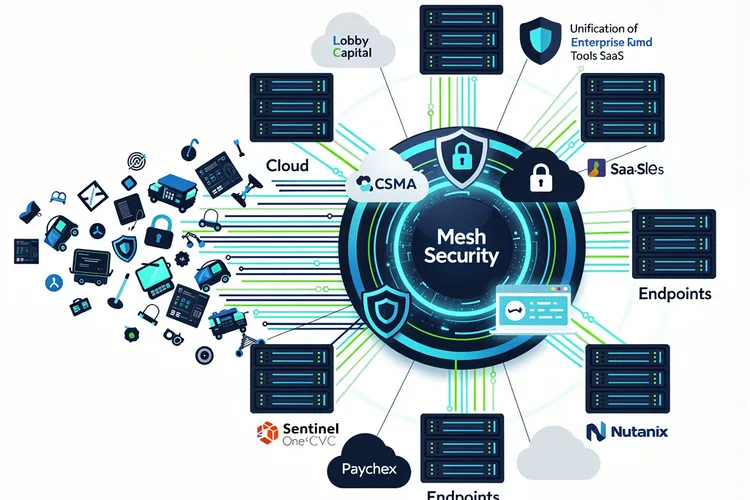
Mesh Security’s $12M Bet: Unifying Cyber Chaos into Enterprise Powerhouse
Mesh Security's $12M Series A funds its CSMA platform to unify enterprise cyber tools across clouds and SaaS, eliminating silos agentlessly. Backed by Lobby Capital and SentinelOne's CVC, it gains traction with Paychex and Nutanix amid tool sprawl crisis.
IT Management
Abstract Security and Netskope Forge Real-Time Threat Pipeline, Slicing Through Data Delays
Abstract Security and Netskope's new partnership embeds real-time detection into security data streams, eliminating indexing delays and slashing costs for joint customers. By processing Netskope telemetry in motion, it boosts threat response while preserving data control.
IT Management
Nationwide’s AI Fortress: AWS Bolsters Fraud Defenses for 17 Million Clients
Nationwide Building Society expands its AWS partnership to deploy AI-driven cloud security and fraud prevention, powering tools like Call Checker against impersonation scams affecting 17% of incidents. Workforce training boosts cloud literacy for enhanced service to 17 million customers.
IT Management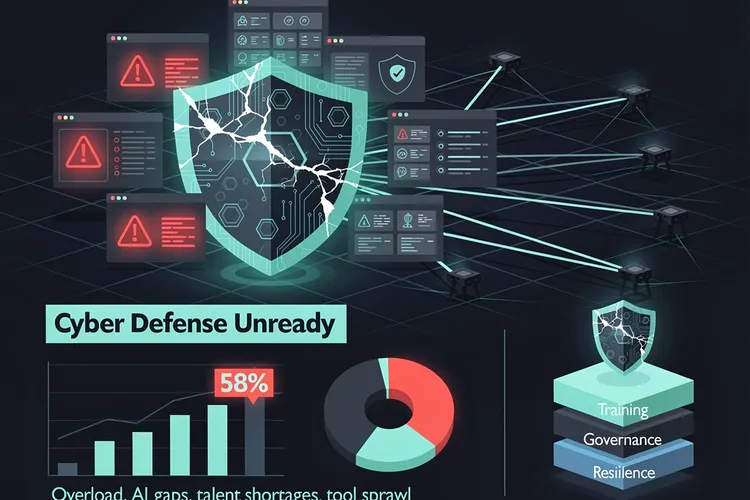
CISOs’ Hidden Roadblocks: Why 58% See Their Firms Unready for Cyber Onslaught
Despite rising budgets, 58% of CISOs deem their organizations unready for cyberattacks, hindered by team overload, AI gaps, talent shortages, and tool sprawl. Experts urge prioritization training, governance, and resilience focus.
IT Management
Security Chiefs Gear Up for AI Agents and Poly-Threats in 2026
Security leaders brace for 2026's AI agents, poly-threats, and quantum risks, shifting from reactive defenses to governance, identity controls, and resilient architectures amid record attacks and regulatory mandates.
IT Management