
IT Management
IT Management focuses on governance, security, infrastructure, and operations—helping teams run reliable systems, reduce risk, and align technology with business goals.
- Home
- IT Management
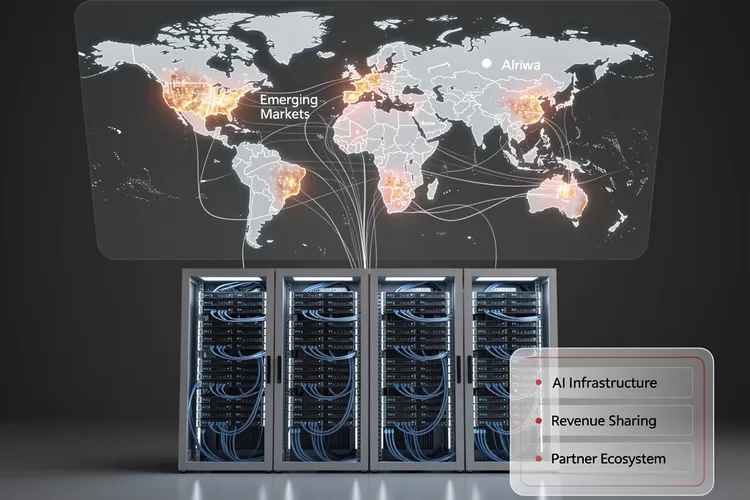
Inside Huawei Cloud’s Bold 2026 Partner Strategy: How Data Centers Become the Cornerstone of AI Infrastructure Expansion
Huawei Cloud's 2026 partner strategy positions data centers as strategic allies in AI infrastructure expansion, offering unprecedented revenue-sharing models and technical integration. The approach targets emerging markets with generous incentives while navigating geopolitical constraints and semiconductor restrictions.

Upwind’s Runtime Revolution: $250M Fuels $1.5B Cloud Security Unicorn
Upwind's $250 million Series B catapults it to $1.5 billion valuation, powering runtime-first cloud security amid 900% revenue surge. Backed by Bessemer and all-stars, the ex-Spot.io team targets AI-era threats for giants like Siemens and Roku.
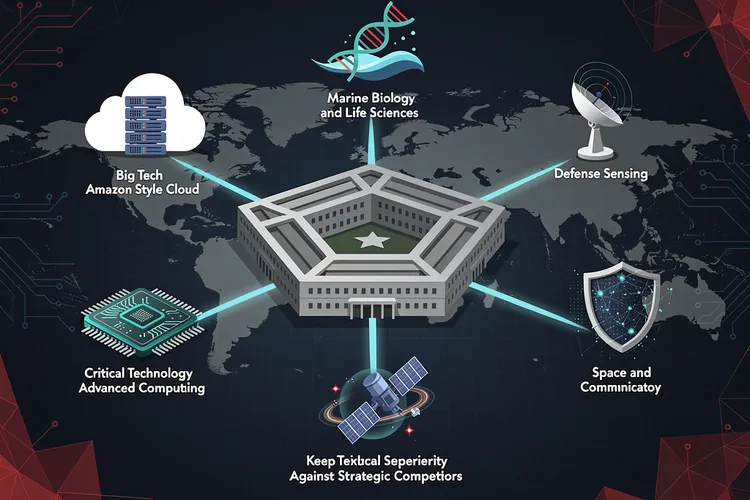
Pentagon’s New Technology Chiefs Signal Major Shift in Defense Innovation Strategy
The Pentagon's Chief Technology Officer has selected six defense technology veterans with diverse backgrounds—from Amazon executives to marine biologists—to lead Critical Technology Areas, signaling a major shift in how the Defense Department approaches innovation and maintains technological superiority against strategic competitors.
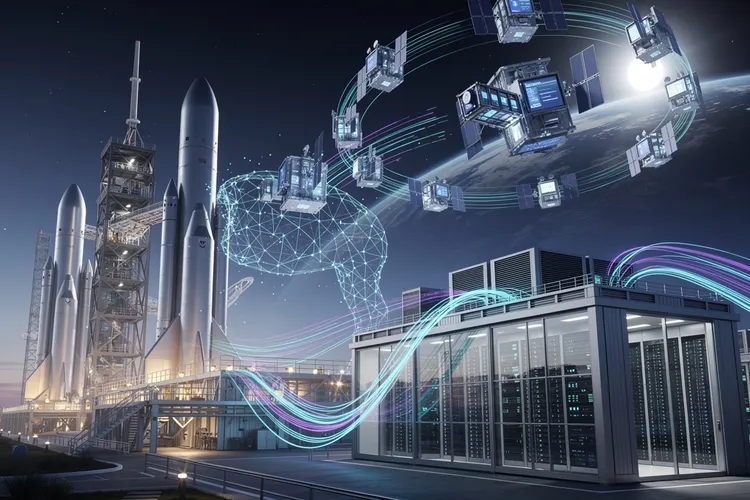
Inside Elon Musk’s Audacious Plan to Fuse Rockets and AI: The SpaceX-xAI Megamerger
Elon Musk is merging SpaceX and xAI in a deal combining an $800 billion rocket manufacturer with a $230 billion AI startup, advancing his vision of space-based data centers while consolidating his technological empire ahead of a planned summer IPO.

Verizon’s Subscriber Surge Signals Schulman’s Turnaround Triumph
Verizon crushed Q4 2025 expectations with 616,000 postpaid phone adds under CEO Dan Schulman, issuing bullish 2026 guidance post-Frontier acquisition. Revenue hit $36.4 billion, signaling a strategic revival amid fierce competition.
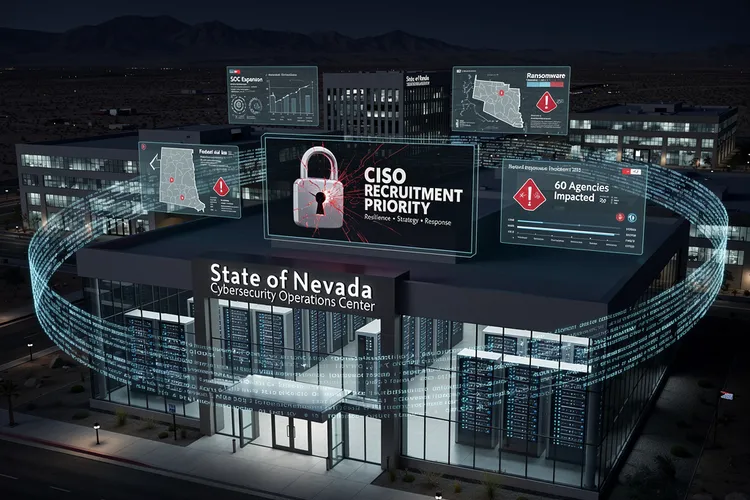
Nevada’s Urgent Hunt for a Cyber Sentinel After Ransomware Chaos
Nevada seeks a permanent CISO after 2025 ransomware chaos disrupted 60 agencies, stole data, and exposed gaps. The role demands strategy, response leadership amid SOC buildup and federal aid, signaling a hardened push for resilience.

How a Startup’s Unsecured Database Exposed the Fragility of AI Agent Platforms
Moltbook's completely exposed database allowed anyone to hijack AI agents on the platform, revealing how rapid AI deployment is outpacing basic cybersecurity practices. The incident highlights growing security debt in the AI startup ecosystem and regulatory gaps in governing autonomous agent platforms.
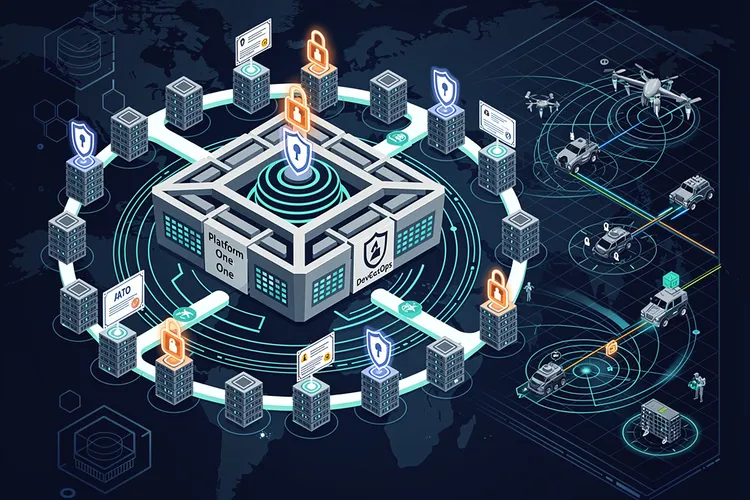
DevSecOps Arsenal: Pentagon’s Push for Warfighter Code at Warp Speed
The Pentagon's DevSecOps revolution integrates security into rapid software delivery, powering over 50 factories and slashing deployment times. From Platform One's secure pipelines to cATO approvals, it equips warfighters with resilient digital edge against evolving threats.
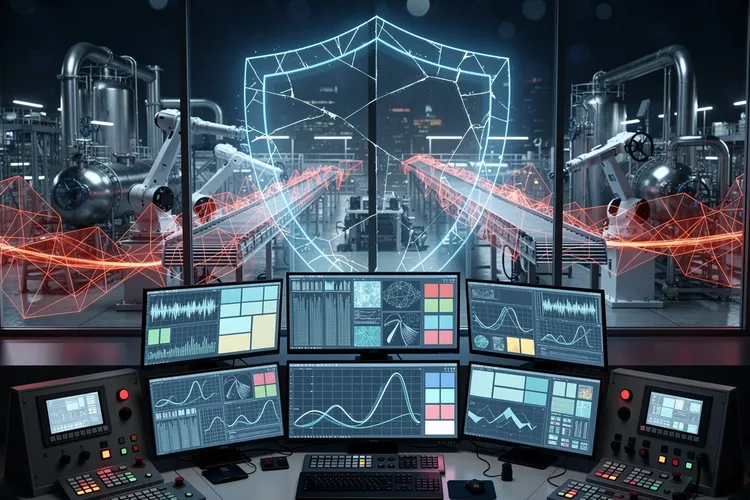
The Invisible Shield: Why Industrial Cybersecurity Still Can’t Quantify Its Worth to the Boardroom
Despite mounting threats to industrial control systems, OT cybersecurity teams face a persistent challenge: proving their value to executives when success means incidents that never happen. The struggle to quantify risk reduction in business terms leaves critical infrastructure chronically underprotected.

Data Scientist’s Trek: From Paris Courts to Australian Mineshafts
Simon Barres bridges labs and mines at QuantumBlack, deploying AI to optimize mining yields with sensor data and real-time models. His journey from Guadeloupe basketball to Amsterdam AI leadership highlights multidisciplinary impact in heavy industry.
The Hidden Dangers Lurking in Your Child’s Digital Diary: Why Moltbook’s Security Flaws Should Alarm Every Parent
Moltbook, a popular digital diary app for children, harbors critical security vulnerabilities that could expose young users' private journal entries to malicious actors. Security researchers have identified fundamental flaws in authentication, encryption, and data protection that raise urgent questions about children's digital safety.
Cloud’s Breaking Point: Fortinet Report Exposes Widening Security Chasm
Fortinet's 2026 Cloud Security Report uncovers a 'complexity gap' where hybrid multi-cloud growth outstrips defenses amid tool sprawl, talent shortages, and AI threats. With 88% in multi-cloud and 66% doubting real-time detection, consolidation emerges as key to resilience.
Google’s Android 16 Empowers Users with Unprecedented Control Over Network Intelligence
Google's Android 16 will introduce unprecedented user control over Adaptive Connectivity, exposing sophisticated network management features that balance Wi-Fi and cellular connections. This represents a philosophical shift toward transparency and user empowerment in mobile operating systems.
Enterprise Cloud Strategies Shift as Multi-Cloud Adoption Surges Toward $1 Trillion Market by 2031
The global multi-cloud computing market is experiencing unprecedented growth as enterprises seek to eliminate vendor dependency and enhance operational resilience. Organizations are discovering tangible benefits in performance optimization, cost management, and regulatory compliance through strategic diversification.
Snowflake’s Energy Play: Unifying Data Silos to Fuel AI-Driven Power Shift
Snowflake's January 27, 2026, Energy Solutions suite unifies IT, OT, and IoT data for energy firms, powering AI for grid optimization and lower emissions. Backed by 30+ partner apps and customers like ExxonMobil and PG&E, it accelerates reliable, decarbonized operations.
Fortifying Code: Security’s Pivot in Web App Development
Security now defines excellence in web app development, driving DevSecOps adoption amid rising AI threats and OWASP risks. Breaches cost $4.44 million on average, per IBM, demanding encryption, zero trust, and vigilant practices from design to deployment.
Data Analyst Reboot: Mastering 2026’s AI-Infused Path
As AI disrupts traditional paths, this deep dive charts a precise 2026 roadmap for data analysts: Excel, SQL, Power BI, Python, AI tools, and portfolios that land jobs amid surging demand.
AI Agents Grounded in DevSecOps Platforms: GitLab and Harness Lure Enterprises with Context
GitLab and Harness deploy context-rich AI agents in DevSecOps platforms, fixing pipelines and incidents autonomously to draw enterprise adopters. With credits-based access and modular designs, they tackle the AI paradox of fast coding but slow delivery.
How a SonicWall Firewall Vulnerability Exposed Marquis Client Data: A Case Study in Enterprise Security Failures
Marquis's data breach through a compromised SonicWall firewall exposes critical vulnerabilities in enterprise network security infrastructure. The incident highlights growing concerns about security appliance reliability and raises important questions about vendor accountability in protecting sensitive healthcare data.
India’s Privacy Pivot: DPDP Rules Reshape AI’s Trust Frontier
India's DPDP Act and 2025 Rules enforce consent-driven privacy amid AI's rise, mandating overhauls for data fiduciaries with phased compliance to May 2027. Enterprises fuse safeguards with cybersecurity, building trust as penalties up to ₹250 crore enforce accountability.
Airtable’s Superagent: Multi-Agent AI Reshapes No-Code Empire
Airtable launches Superagent, its first standalone AI product via DeepSky acquisition, enabling multi-agent coordination for complex research and interactive deliverables. CEO Howie Liu bets big despite valuation reset, positioning the no-code giant as an AI-native powerhouse serving Fortune 100 firms.
Beyond the Buzzword: How Prevention-First Security and Resilient Endpoints Are Making Zero Trust Operational
Zero trust security is evolving from theoretical framework to operational reality through prevention-first architectures and resilient endpoints. Organizations are discovering that building security into infrastructure foundations delivers superior protection and efficiency compared to traditional detect-and-respond approaches, fundamentally transforming enterprise cybersecurity.
OpenClaw Vulnerability Exposes AI Coding Assistants to Single-Click Remote Code Execution
The OpenClaw vulnerability in AI coding assistants enables one-click remote code execution, exposing millions of developers to sophisticated attacks. The flaw exploits trust relationships between programmers and AI tools, turning productivity enhancers into potential attack vectors with far-reaching supply chain implications.
GSA’s Stealth Cybersecurity Mandate Reshapes Federal Procurement Without Fanfare
The General Services Administration has quietly implemented comprehensive cybersecurity requirements for federal contractors, mirroring the Defense Department's CMMC framework but applying immediately to civilian agency contracts. The self-attestation model prioritizes accessibility over third-party verification, creating new compliance challenges for small businesses while attempting to strengthen federal supply chain security.
When Machines Hunt Bugs: How AI-Powered Security Teams Are Rewriting the Rules of Vulnerability Discovery
An AI-assisted security team's discovery of multiple OpenSSL vulnerabilities marks a turning point in cybersecurity research, earning praise from maintainers for report quality and collaboration while demonstrating how artificial intelligence can augment rather than replace human expertise in protecting critical digital infrastructure.
Apple’s Gemini Integration: How Tim Cook Plans to Maintain Privacy Fortress While Opening AI Gates
Apple's integration of Google's Gemini AI into iOS marks a watershed moment for the company, as CEO Tim Cook insists the partnership won't compromise privacy principles. The move reflects competitive pressures in AI while attempting to maintain Apple's privacy-first brand identity through novel technical safeguards.
The Data Fluency Imperative: How Modern Marketers Are Mastering Analytics Terminology to Drive Business Growth
As marketing technology grows more sophisticated, understanding data analytics terminology has transformed from optional knowledge into a fundamental requirement. This deep dive explores how modern marketers are building analytical fluency to drive business growth and strategic decision-making in data-driven organizations.
FBI’s RAMP Takedown: Dismantling Ransomware’s Last Open Market
The FBI seized RAMP, ransomware's premier forum, granting access to user data that could spark arrests. Born from 2021 bans, it hosted gangs recruiting affiliates amid law enforcement pressure.
Subscribe Newsletter
Subscribe to our newsletter and stay up to date with the latest news, updates, and exclusive offers. Join our community today!
The Quantum Leap: How Cloud-Based Quantum Computing Is Reshaping Corporate Strategy and Investment
Quantum computing has emerged from research labs into cloud-based services, allowing businesses to access experimental quantum hardware remotely. This democratization is reshaping corporate strategy across industries, from pharmaceuticals to finance, as organizations experiment with quantum algorithms without massive infrastructure investments.
North Korean Malware Fractures Into Three-Headed Hydra as Pyongyang Refines Cyber Arsenal
North Korean hackers have evolved a dangerous malware strain into three distinct variants that work together to maximize damage while evading detection. This fragmentation strategy represents a significant escalation in Pyongyang's cyber capabilities, targeting financial institutions and critical infrastructure worldwide.
Inside the NSA’s Ambitious Blueprint to Revolutionize Federal Cybersecurity Through Zero Trust Architecture
The NSA has released comprehensive two-phase Zero Trust Implementation Guidelines from Fort Meade, providing federal agencies with unprecedented technical specifications for transitioning from legacy perimeter security to architectures that verify every access request, marking a critical milestone in meeting the 2027 OMB cybersecurity deadline.
How Cybercriminals Weaponized Hugging Face’s AI Platform to Deploy Android Banking Trojans at Scale
Cybercriminals exploited Hugging Face's trusted AI platform to distribute Android banking trojans at scale, revealing how threat actors weaponize legitimate machine learning infrastructure. The sophisticated campaign bypassed traditional security measures by leveraging the platform's reputation to deliver malware targeting financial credentials and authentication systems across multiple continents.
Sycomp’s Strategic Cloudability Partnership Signals Enterprise FinOps Evolution Beyond Traditional Cost Management
Sycomp's strategic partnership with Apptio's Cloudability platform represents a significant evolution in enterprise cloud financial management, integrating sophisticated FinOps capabilities into managed services as organizations face mounting pressure to optimize multi-cloud spending while maintaining innovation velocity.
Why Disabling 2G on Your Smartphone Is the Security Upgrade You Can’t Afford to Ignore
Security experts warn that 2G networks remain a critical vulnerability in modern smartphones. The outdated technology lacks proper authentication and encryption, allowing attackers to deploy fake cell towers that intercept communications. Disabling 2G connectivity provides immediate protection against these sophisticated surveillance attacks.
Join Us
Share your perspective with confidence. Your experience could inform, inspire, and help someone live better.





