
IT Management
IT Management focuses on governance, security, infrastructure, and operations—helping teams run reliable systems, reduce risk, and align technology with business goals.
- Home
- IT Management
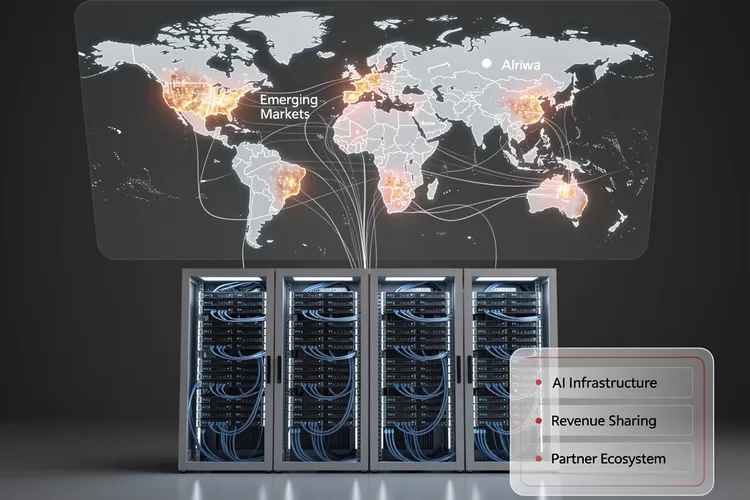
Inside Huawei Cloud’s Bold 2026 Partner Strategy: How Data Centers Become the Cornerstone of AI Infrastructure Expansion
Huawei Cloud's 2026 partner strategy positions data centers as strategic allies in AI infrastructure expansion, offering unprecedented revenue-sharing models and technical integration. The approach targets emerging markets with generous incentives while navigating geopolitical constraints and semiconductor restrictions.

Upwind’s Runtime Revolution: $250M Fuels $1.5B Cloud Security Unicorn
Upwind's $250 million Series B catapults it to $1.5 billion valuation, powering runtime-first cloud security amid 900% revenue surge. Backed by Bessemer and all-stars, the ex-Spot.io team targets AI-era threats for giants like Siemens and Roku.
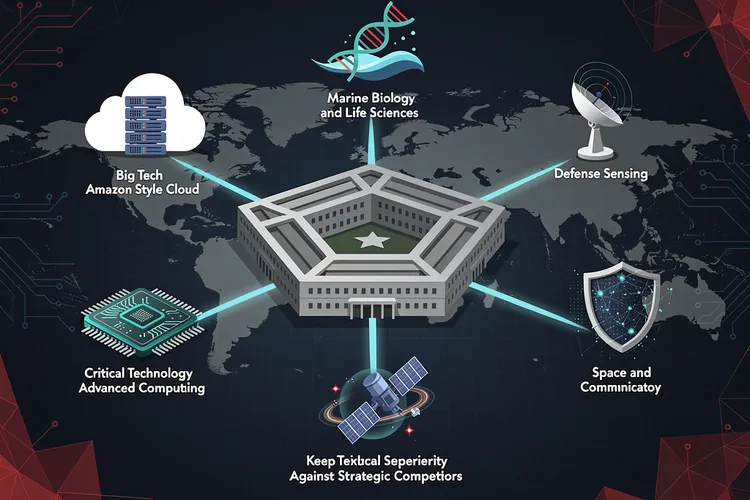
Pentagon’s New Technology Chiefs Signal Major Shift in Defense Innovation Strategy
The Pentagon's Chief Technology Officer has selected six defense technology veterans with diverse backgrounds—from Amazon executives to marine biologists—to lead Critical Technology Areas, signaling a major shift in how the Defense Department approaches innovation and maintains technological superiority against strategic competitors.
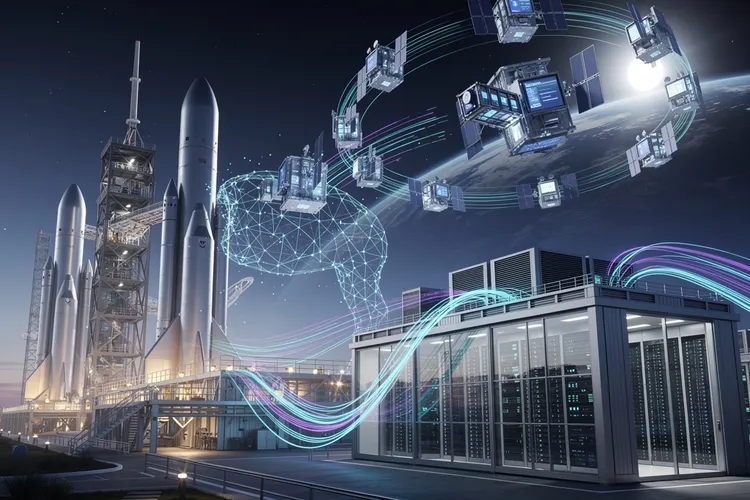
Inside Elon Musk’s Audacious Plan to Fuse Rockets and AI: The SpaceX-xAI Megamerger
Elon Musk is merging SpaceX and xAI in a deal combining an $800 billion rocket manufacturer with a $230 billion AI startup, advancing his vision of space-based data centers while consolidating his technological empire ahead of a planned summer IPO.

Verizon’s Subscriber Surge Signals Schulman’s Turnaround Triumph
Verizon crushed Q4 2025 expectations with 616,000 postpaid phone adds under CEO Dan Schulman, issuing bullish 2026 guidance post-Frontier acquisition. Revenue hit $36.4 billion, signaling a strategic revival amid fierce competition.
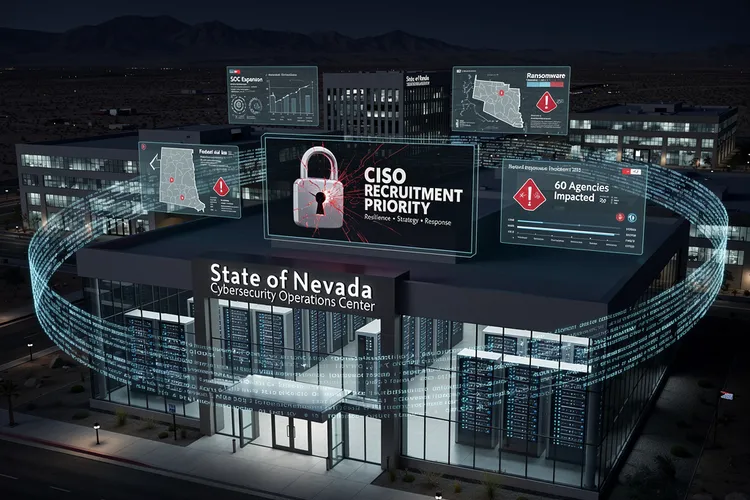
Nevada’s Urgent Hunt for a Cyber Sentinel After Ransomware Chaos
Nevada seeks a permanent CISO after 2025 ransomware chaos disrupted 60 agencies, stole data, and exposed gaps. The role demands strategy, response leadership amid SOC buildup and federal aid, signaling a hardened push for resilience.

How a Startup’s Unsecured Database Exposed the Fragility of AI Agent Platforms
Moltbook's completely exposed database allowed anyone to hijack AI agents on the platform, revealing how rapid AI deployment is outpacing basic cybersecurity practices. The incident highlights growing security debt in the AI startup ecosystem and regulatory gaps in governing autonomous agent platforms.
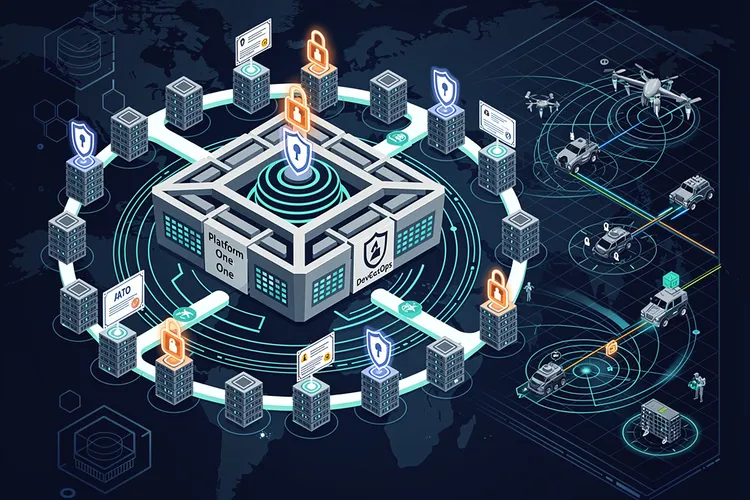
DevSecOps Arsenal: Pentagon’s Push for Warfighter Code at Warp Speed
The Pentagon's DevSecOps revolution integrates security into rapid software delivery, powering over 50 factories and slashing deployment times. From Platform One's secure pipelines to cATO approvals, it equips warfighters with resilient digital edge against evolving threats.
The Invisible Shield: Why Industrial Cybersecurity Still Can’t Quantify Its Worth to the Boardroom
Despite mounting threats to industrial control systems, OT cybersecurity teams face a persistent challenge: proving their value to executives when success means incidents that never happen. The struggle to quantify risk reduction in business terms leaves critical infrastructure chronically underprotected.

Data Scientist’s Trek: From Paris Courts to Australian Mineshafts
Simon Barres bridges labs and mines at QuantumBlack, deploying AI to optimize mining yields with sensor data and real-time models. His journey from Guadeloupe basketball to Amsterdam AI leadership highlights multidisciplinary impact in heavy industry.
Inside Mustang Panda’s Arsenal: How China’s Elite Hackers Refined Their Most Persistent Malware
Chinese state-sponsored hacking group Mustang Panda has deployed enhanced versions of its TONESHELL backdoor and PlugX malware, incorporating sophisticated evasion techniques and modular architecture. The updates demonstrate continuous evolution in tradecraft targeting government and diplomatic entities worldwide.
Alkira Taps S&P Global Veteran to Turbocharge AI Networking Ambitions
Alkira appoints S&P Global's Guru Ramamoorthy to its advisory board, leveraging his expertise in cloud and AI infrastructure to advance AI-native networking for enterprises facing multi-cloud and security challenges.
Aisuru-Kimwolf’s 31.4 Tbps Onslaught: Inside the Largest DDoS Assault on Record
Cloudflare blocked a record 31.4 Tbps DDoS from the Aisuru/Kimwolf botnet on December 19, 2025, surpassing prior peaks amid a 121% annual attack surge. Powered by millions of compromised IoT and Android devices, the assault targeted telecoms and infrastructure.
Split Inference: Enterprise IT’s New AI Power Equation
Enterprise IT pivots to split inference, partitioning AI tasks across edge devices and cloud clusters via secure networks. This hybrid model balances latency, cost and scale as inference dominates 2026 compute, per Deloitte and Gartner projections.
Inside the Alarming Security Failures Plaguing America’s Power Grid Infrastructure
A comprehensive survey of over 100 energy facilities reveals widespread cybersecurity vulnerabilities in operational technology systems controlling power generation and distribution. The study exposes fundamental security gaps including weak authentication, unpatched legacy systems, and inadequate network segmentation that leave critical infrastructure exposed to nation-state threats.
Tulsa Airport Breach Exposes Critical Infrastructure Vulnerabilities as Russian Ransomware Group Claims Responsibility
Russian ransomware hackers allegedly breached Tulsa International Airport's systems, dumping private operational files online as proof of infiltration. The attack highlights growing vulnerabilities in regional transportation infrastructure and raises urgent questions about cybersecurity preparedness across American airports.
Automation Platform n8n Patches Critical Flaws That Exposed Enterprise Workflows to Remote Takeover
Two high-severity vulnerabilities in the n8n workflow automation platform could have allowed attackers to execute arbitrary code and steal credentials, highlighting growing security challenges in enterprise automation tools. The flaws underscore the critical need for enhanced security practices in low-code platforms.
Chewy’s Technology Leadership Transition Arrives at Pivotal Moment for Pet Retail Giant’s Digital Strategy
Chewy's announcement of CTO Satish Mehta's retirement arrives at a critical moment as the pet retail giant navigates mounting pressure to accelerate AI integration and enhance membership programs. The search for new technology leadership will determine whether the company maintains its competitive edge in an increasingly sophisticated digital retail environment.
Windows 11’s Gaming Gains Overshadowed by Stability Crisis: Performance Tests Reveal a Troubled Transition
Windows 11 version 24H2 delivers measurable gaming performance improvements over Windows 10, with frame rates up to 8% higher in testing. However, widespread Blue Screen of Death errors and stability issues are undermining user confidence and delaying adoption among gamers and enterprises alike.
Woteki Legacy: $10 Million Fuels Virginia Tech’s Data Science Push Across Science and Agriculture
Alumni power couple Cathie and Tom Woteki pledged $10 million to Virginia Tech, endowing key positions in transdisciplinary data science across science and agriculture colleges to drive faculty excellence and data-driven discoveries in food, health, and policy.
The Confidence Crisis: Why Nearly 60% of Security Chiefs Say Their Companies Can’t Handle a Cyberattack
Despite record cybersecurity spending, 58% of CISOs believe their organizations are unprepared for cyberattacks. Four fundamental challenges—budget misalignment, organizational silos, talent shortages, and inadequate executive support—create a dangerous gap between security investments and actual readiness, leaving companies vulnerable despite their best intentions.
When Cybersecurity Leadership Bypasses Its Own Rules: The CISA ChatGPT Incident
A senior CISA official uploaded sensitive government contracting documents to public ChatGPT, bypassing DHS-approved AI tools. The incident exposes critical gaps between federal cybersecurity policy and practice, raising questions about enforcement, training, and the challenges agencies face in securely adopting generative AI technologies.
European Cloud Sovereignty Takes Center Stage as OpenNebula and OVHcloud Forge Strategic Alliance
OpenNebula Systems and OVHcloud have forged a strategic partnership to deliver sovereign cloud solutions for European organizations, combining open-source infrastructure management with European data centers to address growing concerns about data sovereignty and regulatory compliance.
Decoding Elite CTOs: Traits Driving Tech Supremacy in 2026
Elite CTOs in 2026 blend technical depth, strategic vision, and empathetic leadership to master AI integration, team building, and ethical innovation. Drawing from CIO.com, Forbes, and Edstellar, this analysis reveals traits powering tech dominance amid quantum and sustainability shifts.
The Strategic Imperative: How CIOs Are Redefining Enterprise Leadership Through 2026
Chief Information Officers are solidifying their positions as essential strategic leaders through 2026, navigating artificial intelligence deployment, cybersecurity threats, cloud optimization, and talent challenges while demonstrating measurable business impact that extends far beyond traditional technology management.
Meta’s Reality Check: How Slowing VR Adoption Is Reshaping the Company’s Metaverse Ambitions
Meta CTO Andrew Bosworth's admission that VR is growing slower than hoped marks a strategic inflection point for the company's multibillion-dollar metaverse ambitions, prompting layoffs and a rebalancing of resources toward artificial intelligence while maintaining long-term commitment to immersive technology.
The Hidden Threat in Your Search Results: How Mac Malware Infiltrates Google’s Advertising Ecosystem
Cybercriminals are exploiting Google's advertising platform to distribute sophisticated Mac malware through sponsored search results, undermining user trust and challenging Apple's security model. This investigation reveals how attackers leverage premium ad placements to reach valuable targets.
When Security Testing Becomes a Criminal Case: Iowa County’s $600,000 Lesson in Authorized Penetration Testing
Dallas County, Iowa's $600,000 settlement with security researchers arrested during authorized penetration testing highlights critical gaps in communication between contracting parties and law enforcement, raising important questions about legal protections for cybersecurity professionals conducting legitimate security assessments.
Subscribe Newsletter
Subscribe to our newsletter and stay up to date with the latest news, updates, and exclusive offers. Join our community today!
SolarWinds’ Web Help Desk: RCE Flaws Reawaken Supply-Chain Ghosts
SolarWinds discloses six Web Help Desk flaws, four critical RCE and auth bypass bugs rated 9.8 CVSS, urging upgrades to 2026.1. Echoing 2020 supply-chain attack and prior exploits, experts warn of rapid weaponization and massive downstream risks.
How a DNS Configuration Error Sent Microsoft’s Traffic to a Small Japanese Firm for Months
Microsoft recently resolved a DNS misconfiguration that silently redirected portions of its network traffic to an obscure Japanese company for months, exposing vulnerabilities in cloud infrastructure monitoring and raising questions about data security in modern internet routing systems.
Percona’s OpenEverest Challenges Cloud Giants with Kubernetes-Native Database Automation
Percona's OpenEverest platform introduces open-source database automation for Kubernetes, challenging cloud providers' managed services with multi-engine support and deployment flexibility. The platform addresses vendor lock-in concerns while enabling unified database management across hybrid and multi-cloud environments.
Abstract Security and Netskope Forge Real-Time Threat Pipeline, Slicing Through Data Delays
Abstract Security and Netskope's new partnership embeds real-time detection into security data streams, eliminating indexing delays and slashing costs for joint customers. By processing Netskope telemetry in motion, it boosts threat response while preserving data control.
Aurora PostgreSQL 13 Deadline: Four Upgrade Paths to Beat February Cutoff
As support for PostgreSQL 13 on Aurora and RDS ends February 28, 2026, AWS outlines in-place, blue/green, logical replication, and DMS strategies. Upgrades unlock 2x write throughput, advanced security, and 8x query speedups, but demand testing for breaking catalog changes.
The New Data Analyst Playbook: How Industry Veterans Are Redefining Career Entry in 2026
The path to becoming a data analyst in 2026 emphasizes practical skills over theoretical knowledge, with SQL, Excel, and dashboard creation consuming 70% of working time. Industry veterans now recommend domain expertise and project portfolios over traditional credentials, reflecting a market shift toward immediate business value.
Join Us
Share your perspective with confidence. Your experience could inform, inspire, and help someone live better.





