- Home
- IT Management
Inside Palantir’s Double-Digit Surge: How AI Contracts and Government Spending Drove a Market-Beating Quarter
Palantir Technologies surged 10% after delivering fourth-quarter earnings that exceeded Wall Street expectations, driven by accelerating AI platform adoption and strong government contracts. The results underscore the company's successful transformation into an enterprise AI infrastructure leader.
The Hidden Dangers Lurking in Your Child’s Digital Diary: Why Moltbook’s Security Flaws Should Alarm Every Parent
Moltbook, a popular digital diary app for children, harbors critical security vulnerabilities that could expose young users' private journal entries to malicious actors. Security researchers have identified fundamental flaws in authentication, encryption, and data protection that raise urgent questions about children's digital safety.
Apple’s Safari Technology Preview 236 Signals Strategic Shift in Browser Development Amid Growing Competition
Apple's Safari Technology Preview 236 introduces significant WebKit improvements and privacy features amid intense browser competition. The release highlights Apple's strategic priorities as regulatory pressures and market dynamics reshape the browser ecosystem.
When Machines Hunt Bugs: How AI-Powered Security Teams Are Rewriting the Rules of Vulnerability Discovery
An AI-assisted security team's discovery of multiple OpenSSL vulnerabilities marks a turning point in cybersecurity research, earning praise from maintainers for report quality and collaboration while demonstrating how artificial intelligence can augment rather than replace human expertise in protecting critical digital infrastructure.
Docker’s AI Assistant Vulnerability Exposes Critical Security Flaws in Containerization Platform
Docker has patched a critical vulnerability in its Ask Gordon AI assistant that could have allowed attackers to execute arbitrary code through prompt injection. The flaw highlights growing security concerns as companies integrate AI into enterprise infrastructure tools.
Sophisticated Apple Pay Phishing Scheme Exploits User Trust Through Multi-Channel Attack Vector
A sophisticated multi-channel phishing campaign is targeting Apple Pay users through coordinated text messages, phone calls, and fraudulent websites. The operation exploits user trust in Apple's brand and payment platform, representing an evolution in social engineering tactics that security experts warn poses significant risks to digital payment security.
Federal Data Dragnet: How DHS Demands on Tech Giants Target Political Dissent in the Digital Age
The Department of Homeland Security is compelling major technology companies to surrender user data on Trump critics, raising profound questions about surveillance powers, corporate compliance, and First Amendment protections in the digital age. This unprecedented campaign targets political speech through National Security Letters and administrative subpoenas, creating tensions between national security claims and civil liberties.
The Terminal Threat: How AI Agents Are Exposing Critical Vulnerabilities in macOS Security Architecture
The integration of AI agents with terminal access in macOS has created unprecedented security vulnerabilities. This convergence allows AI systems to execute powerful system commands through natural language, potentially bypassing traditional security measures and exposing millions of users to sophisticated attacks.
Google Cloud’s Unified Maintenance Strategy Signals Major Shift in Enterprise Infrastructure Management
Google Cloud's new Unified Maintenance platform centralizes planned maintenance management across services, offering enterprises unprecedented control over infrastructure updates. The move signals a strategic shift in cloud operations, emphasizing predictability and customer control while addressing the hidden costs of maintenance coordination in complex cloud environments.
Inside Microsoft’s Copilot Crisis: How the Tech Giant’s AI Flagship Lost Its Way
Microsoft's Copilot chatbot, positioned as the cornerstone of its AI transformation, is losing users to competitors despite massive marketing investments. Data shows paid subscribers using Copilot as their primary option dropped from 18.8% to 11.5% while Google's Gemini gained ground, raising questions about the tech giant's AI strategy.
AMD’s AI Ambitions Meet Wall Street’s Reality Check: Why Strong Growth Wasn’t Enough
AMD's 34% revenue growth to $10.3 billion and surging data center sales failed to satisfy investors seeking bigger AI gains. The chipmaker's stock dropped 8% after forecasting Q1 revenue below $10 billion, highlighting the intense pressure facing semiconductor companies in the AI era.
Related

Formae’s Multi-Cloud Leap: Platform Engineering Labs Arms Builders Against IaC Gridlock
Platform Engineering Labs' formae surges to multi-cloud with GCP, Azure, OCI, and OVH beta support plus a Plugin SDK, empowering infrastructure builders to extend IaC without vendor delays. This upgrade redefines extensibility in a fragmented cloud era.

Sky47’s Sovereign Surge: Pakistan’s Massive AI Cloud Bet
Sky47's January 2026 launch marks Pakistan's boldest sovereign cloud move, with 3,000 racks and 50MW for AI workloads. Backed by Mari Energies and Fauji Foundation, it eyes hyperscalers amid rising data sovereignty demands.

Cloud’s Complexity Trap: How Tool Overload and AI-Wielding Attackers Are Fracturing Security Defenses
Fortinet's 2026 Cloud Security Report exposes a widening complexity gap in hybrid clouds, where tool sprawl, AI-driven attacks, and skills shortages overwhelm teams despite rising budgets. Nearly 70% cite fragmentation as the top barrier, urging platform shifts and MSSP aid.
IT Management
NordVPN’s Sixth Consecutive Audit Validates Zero-Logs Promise as Privacy Scrutiny Intensifies
NordVPN completes its sixth consecutive independent audit by Deloitte, confirming its zero-logs policy amid intensifying privacy scrutiny. The verification highlights industry trends toward verifiable transparency as regulatory pressure mounts and consumer skepticism grows regarding VPN privacy claims.
IT Management
Upwind’s Runtime Revolution: $250M Fuels $1.5B Cloud Security Unicorn
Upwind's $250 million Series B catapults it to $1.5 billion valuation, powering runtime-first cloud security amid 900% revenue surge. Backed by Bessemer and all-stars, the ex-Spot.io team targets AI-era threats for giants like Siemens and Roku.
IT Management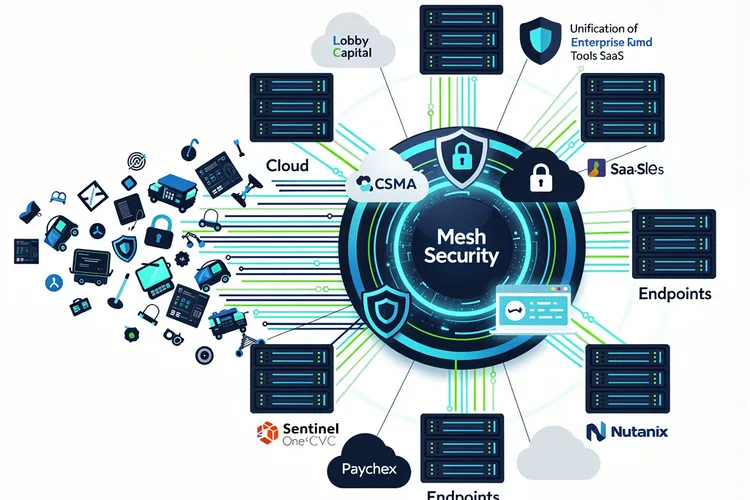
Mesh Security’s $12M Bet: Unifying Cyber Chaos into Enterprise Powerhouse
Mesh Security's $12M Series A funds its CSMA platform to unify enterprise cyber tools across clouds and SaaS, eliminating silos agentlessly. Backed by Lobby Capital and SentinelOne's CVC, it gains traction with Paychex and Nutanix amid tool sprawl crisis.
IT Management
Abstract Security and Netskope Forge Real-Time Threat Pipeline, Slicing Through Data Delays
Abstract Security and Netskope's new partnership embeds real-time detection into security data streams, eliminating indexing delays and slashing costs for joint customers. By processing Netskope telemetry in motion, it boosts threat response while preserving data control.
IT Management
Nationwide’s AI Fortress: AWS Bolsters Fraud Defenses for 17 Million Clients
Nationwide Building Society expands its AWS partnership to deploy AI-driven cloud security and fraud prevention, powering tools like Call Checker against impersonation scams affecting 17% of incidents. Workforce training boosts cloud literacy for enhanced service to 17 million customers.
IT Management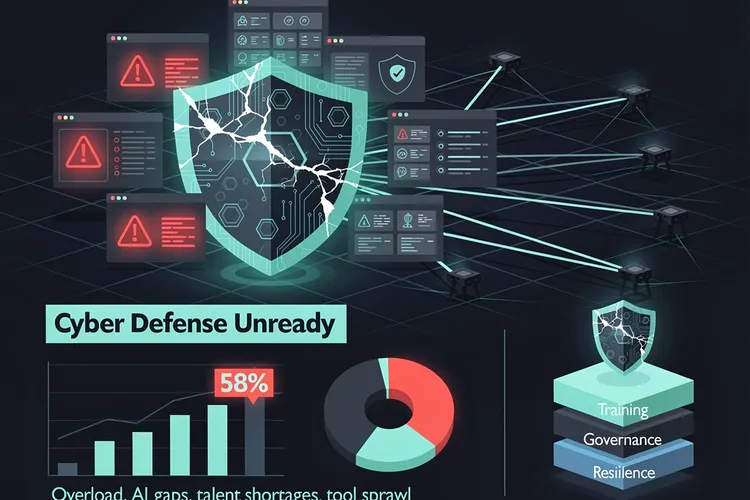
CISOs’ Hidden Roadblocks: Why 58% See Their Firms Unready for Cyber Onslaught
Despite rising budgets, 58% of CISOs deem their organizations unready for cyberattacks, hindered by team overload, AI gaps, talent shortages, and tool sprawl. Experts urge prioritization training, governance, and resilience focus.
IT Management
Security Chiefs Gear Up for AI Agents and Poly-Threats in 2026
Security leaders brace for 2026's AI agents, poly-threats, and quantum risks, shifting from reactive defenses to governance, identity controls, and resilient architectures amid record attacks and regulatory mandates.
IT Management