
IT Management
IT Management focuses on governance, security, infrastructure, and operations—helping teams run reliable systems, reduce risk, and align technology with business goals.
- Home
- IT Management
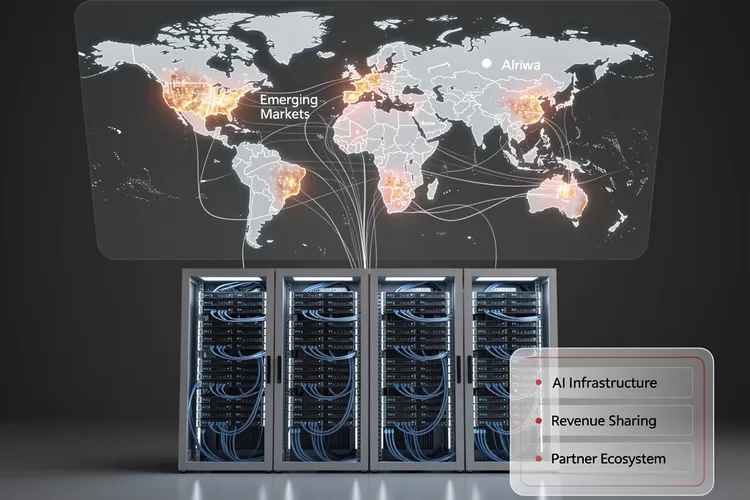
Inside Huawei Cloud’s Bold 2026 Partner Strategy: How Data Centers Become the Cornerstone of AI Infrastructure Expansion
Huawei Cloud's 2026 partner strategy positions data centers as strategic allies in AI infrastructure expansion, offering unprecedented revenue-sharing models and technical integration. The approach targets emerging markets with generous incentives while navigating geopolitical constraints and semiconductor restrictions.

Upwind’s Runtime Revolution: $250M Fuels $1.5B Cloud Security Unicorn
Upwind's $250 million Series B catapults it to $1.5 billion valuation, powering runtime-first cloud security amid 900% revenue surge. Backed by Bessemer and all-stars, the ex-Spot.io team targets AI-era threats for giants like Siemens and Roku.
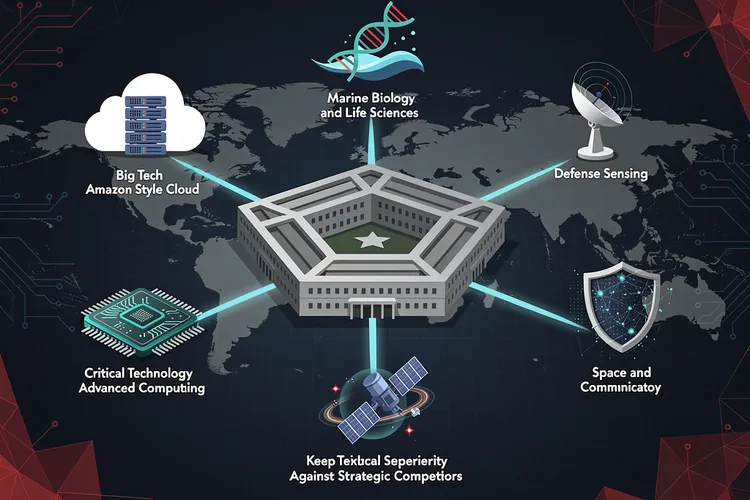
Pentagon’s New Technology Chiefs Signal Major Shift in Defense Innovation Strategy
The Pentagon's Chief Technology Officer has selected six defense technology veterans with diverse backgrounds—from Amazon executives to marine biologists—to lead Critical Technology Areas, signaling a major shift in how the Defense Department approaches innovation and maintains technological superiority against strategic competitors.
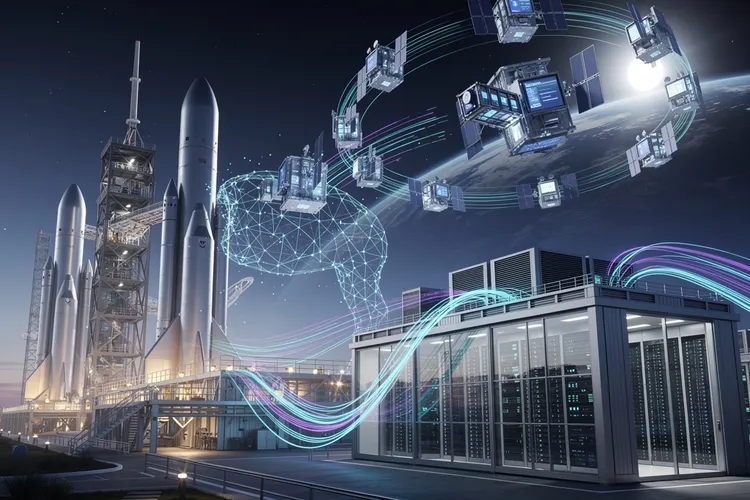
Inside Elon Musk’s Audacious Plan to Fuse Rockets and AI: The SpaceX-xAI Megamerger
Elon Musk is merging SpaceX and xAI in a deal combining an $800 billion rocket manufacturer with a $230 billion AI startup, advancing his vision of space-based data centers while consolidating his technological empire ahead of a planned summer IPO.

Verizon’s Subscriber Surge Signals Schulman’s Turnaround Triumph
Verizon crushed Q4 2025 expectations with 616,000 postpaid phone adds under CEO Dan Schulman, issuing bullish 2026 guidance post-Frontier acquisition. Revenue hit $36.4 billion, signaling a strategic revival amid fierce competition.
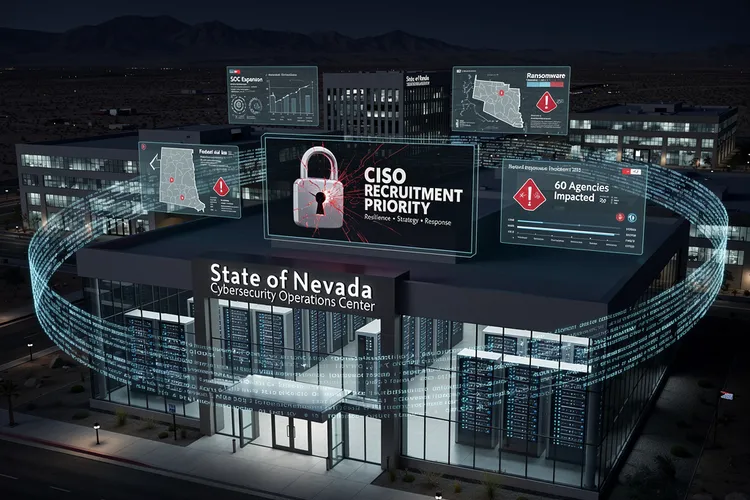
Nevada’s Urgent Hunt for a Cyber Sentinel After Ransomware Chaos
Nevada seeks a permanent CISO after 2025 ransomware chaos disrupted 60 agencies, stole data, and exposed gaps. The role demands strategy, response leadership amid SOC buildup and federal aid, signaling a hardened push for resilience.

How a Startup’s Unsecured Database Exposed the Fragility of AI Agent Platforms
Moltbook's completely exposed database allowed anyone to hijack AI agents on the platform, revealing how rapid AI deployment is outpacing basic cybersecurity practices. The incident highlights growing security debt in the AI startup ecosystem and regulatory gaps in governing autonomous agent platforms.
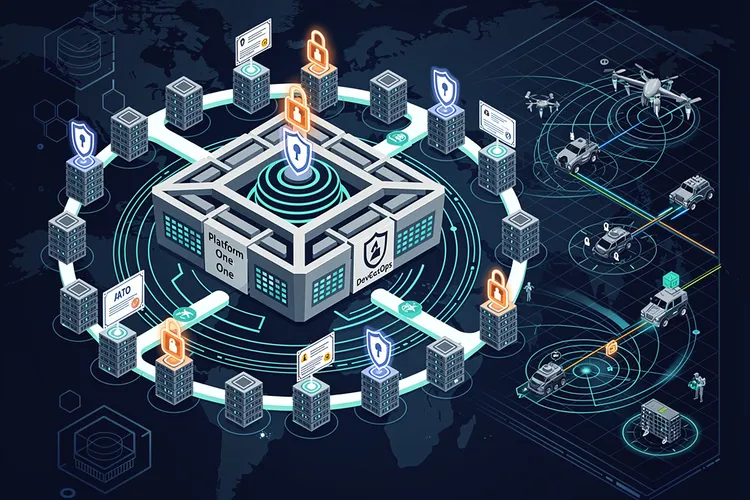
DevSecOps Arsenal: Pentagon’s Push for Warfighter Code at Warp Speed
The Pentagon's DevSecOps revolution integrates security into rapid software delivery, powering over 50 factories and slashing deployment times. From Platform One's secure pipelines to cATO approvals, it equips warfighters with resilient digital edge against evolving threats.
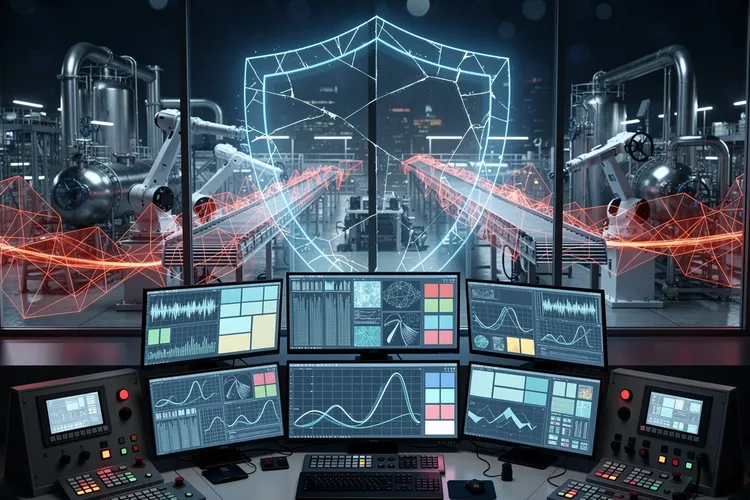
The Invisible Shield: Why Industrial Cybersecurity Still Can’t Quantify Its Worth to the Boardroom
Despite mounting threats to industrial control systems, OT cybersecurity teams face a persistent challenge: proving their value to executives when success means incidents that never happen. The struggle to quantify risk reduction in business terms leaves critical infrastructure chronically underprotected.

Data Scientist’s Trek: From Paris Courts to Australian Mineshafts
Simon Barres bridges labs and mines at QuantumBlack, deploying AI to optimize mining yields with sensor data and real-time models. His journey from Guadeloupe basketball to Amsterdam AI leadership highlights multidisciplinary impact in heavy industry.
Nationwide’s AI Fortress: AWS Bolsters Fraud Defenses for 17 Million Clients
Nationwide Building Society expands its AWS partnership to deploy AI-driven cloud security and fraud prevention, powering tools like Call Checker against impersonation scams affecting 17% of incidents. Workforce training boosts cloud literacy for enhanced service to 17 million customers.
Tech Titans’ Integration Nightmares: Why AI and Quantum Stymie CTOs
CTOs battle AI data woes, blockchain scalability snags, quantum talent voids, IoT security floods, and AR/VR compatibility clashes amid legacy binds. Surveys and reports reveal strategies for enterprise survival.
Inside NC State’s AI Revolution: How Marc Hoit Is Rewriting the Playbook for University Technology Leadership
North Carolina State University CIO Marc Hoit is pioneering AI democratization in higher education through collaborative stakeholder engagement rather than top-down mandates. His approach prioritizes widespread access to AI tools across campus while building governance frameworks that enable innovation without sacrificing institutional protections.
Apple’s Safari Technology Preview 236 Signals Strategic Shift in Browser Development Amid Growing Competition
Apple's Safari Technology Preview 236 introduces significant WebKit improvements and privacy features amid intense browser competition. The release highlights Apple's strategic priorities as regulatory pressures and market dynamics reshape the browser ecosystem.
The Battle Against Cookie Consent Fatigue: How Browser Extensions Are Reshaping Digital Privacy Compliance
Cookie consent banners have become the web's most frustrating feature, spawning browser extensions that automate privacy choices. This deep dive examines the technical, legal, and business implications of automated consent management and its role in reshaping digital privacy compliance.
China’s Mandate to End Tesla’s Flush Door Handles Signals Broader Safety Reckoning for Electric Vehicle Design
China mandates traditional door handles on all vehicles by 2027, targeting Tesla's signature flush design over emergency safety concerns. The regulation forces manufacturers to abandon electronically-activated systems in the world's largest automotive market, with implications for global EV design standards.
America’s Cybersecurity Deficit: Why Strategic Vision Without Operational Execution Leaves Critical Infrastructure Vulnerable
The United States possesses comprehensive cybersecurity strategy documents but lacks operational roadmaps to implement them effectively. This gap between policy and practice leaves critical infrastructure vulnerable to sophisticated threats, requiring detailed frameworks for coordination, resource allocation, and accountability across government and private sectors.
AMD’s AI Ambitions Meet Wall Street’s Reality Check: Why Strong Growth Wasn’t Enough
AMD's 34% revenue growth to $10.3 billion and surging data center sales failed to satisfy investors seeking bigger AI gains. The chipmaker's stock dropped 8% after forecasting Q1 revenue below $10 billion, highlighting the intense pressure facing semiconductor companies in the AI era.
The Enterprise AI Power Struggle: How Anthropic’s Claude is Challenging OpenAI’s Dominance in Corporate America
A survey of Global 2000 companies reveals OpenAI leads with 78% CIO adoption, but Anthropic's rapid rise to 44% signals a fundamental shift in enterprise AI strategy as organizations embrace multi-model approaches and prioritize safety and compliance.
Palantir’s Explosive Growth Signals New Era of AI Dominance in Government and Enterprise Markets
Palantir Technologies delivered fourth-quarter revenue of $1.41 billion, crushing Wall Street estimates with 70% year-over-year growth. The AI software firm's aggressive 2026 guidance projects revenue reaching $7.19 billion, substantially exceeding analyst expectations, while net income surged eight-fold to $608 million, demonstrating sustainable profitability amid broader market concerns about AI valuations.
Meta’s ICE List Firewall: Privacy Clash Amid Agent Tracking Fury
Meta has blocked links to ICE List across Facebook, Instagram and Threads, citing privacy rules amid backlash over a database naming thousands of DHS agents. The move follows Minneapolis unrest from ICE raids, sparking clashes between accountability advocates and safety concerns for officers.
Microsoft’s Delicate Dance: How Redmond Balances Legacy Software Revenue With Cloud Ambitions
Microsoft has mastered the art of balancing traditional software revenue with aggressive cloud expansion, creating a hybrid strategy that outmaneuvers competitors who chose more binary paths. This approach offers crucial lessons for technology incumbents navigating disruptive transitions.
NordVPN’s Sixth Consecutive Audit Validates Zero-Logs Promise as Privacy Scrutiny Intensifies
NordVPN completes its sixth consecutive independent audit by Deloitte, confirming its zero-logs policy amid intensifying privacy scrutiny. The verification highlights industry trends toward verifiable transparency as regulatory pressure mounts and consumer skepticism grows regarding VPN privacy claims.
The Silent Collapse: How America’s Public Health Data Infrastructure Is Crumbling in Real Time
The CDC's public health surveillance infrastructure is collapsing, with nearly half of its databases no longer being updated. Most affected systems track vaccines and infectious diseases, leaving health officials without critical data needed for outbreak response and policy decisions at a crucial time.
Why Linux Mint Could Be Your Escape Route From Windows 11’s Growing Pains
As Windows 11's restrictive requirements and intrusive practices drive users to seek alternatives, Linux Mint emerges as the ideal transition platform. With its familiar interface, robust software compatibility, and respect for user autonomy, Mint offers Windows refugees a compelling escape route.
The Cybersecurity Reckoning: How CISOs Are Preparing for an Era of AI-Driven Threats and Quantum Disruption
Chief Information Security Officers are preparing for an unprecedented convergence of threats in 2026, including AI-powered attacks, quantum computing risks, and systematic targeting of small businesses. These challenges are forcing fundamental changes in how organizations approach cybersecurity.
PAM Overhaul: Securing Privileged Keys for 2026 Audits
Enterprises overhaul privileged access management to counter standing privilege risks amplified by audits and breaches. Modern PAM delivers just-in-time access, session forensics, and compliance proofs amid a $4.44 billion market boom.
Palo Alto Networks Races to Shield Corporate America From Quantum Computing’s Cryptographic Threat
Palo Alto Networks launches quantum-safe security solution providing real-time cryptographic visibility to help enterprises protect against future quantum computing threats. The platform enables automated discovery and risk assessment of vulnerable encryption systems across global IT infrastructure.
Subscribe Newsletter
Subscribe to our newsletter and stay up to date with the latest news, updates, and exclusive offers. Join our community today!
Inside Citadel’s Technology Transition: What a CTO Change Signals for the Hedge Fund Giant
Citadel's Chief Technology Officer Umesh Subramanian is changing roles after seven years leading the hedge fund giant's technology operations.
How Q-SYS and ServiceNow Integration Is Reshaping Enterprise AV Infrastructure Management
Q-SYS's integration with ServiceNow's IT Service Management platform marks a pivotal shift in enterprise AV infrastructure management, enabling automated data flow and unified oversight that bridges the historical divide between audiovisual systems and traditional IT operations.
The Great Divergence: Why IT Management Thrives While Entry-Level Tech Jobs Vanish
The IT job market is splitting dramatically, with entry-level positions vanishing due to automation while management roles boom. Over 100,000 new IT management positions are expected in the next decade, creating a troubling gap in traditional career progression pathways.
Inside PwC and Google Cloud’s $400 Million Gambit to Reinvent Corporate Cybersecurity Through AI
PwC and Google Cloud's $400 million three-year partnership aims to revolutionize corporate cybersecurity by embedding AI capabilities into security operations centers, combining advanced machine learning with threat intelligence to address the growing sophistication of cyber attacks and talent shortages.
Android’s Private DNS Feature Emerges as Powerful Ad-Blocking Alternative to VPN Services
Android's built-in Private DNS feature offers users a powerful, cost-free alternative to VPN-based ad blocking. This hidden setting, available since Android 9, leverages DNS-over-TLS encryption to filter advertisements system-wide while maintaining internet speeds and requiring no additional software installations or subscriptions.
The New Security Imperative: How Chief Information Security Officers Are Redefining Enterprise Defense in the Age of Artificial Intelligence
Chief Information Security Officers face unprecedented challenges in 2026 as artificial intelligence, cloud infrastructure, and distributed workforces converge. This analysis examines five critical security priorities—from securing AI systems to modernizing identity management—that define the evolution of enterprise defense in an era of technological complexity and sophisticated threats.
Join Us
Share your perspective with confidence. Your experience could inform, inspire, and help someone live better.





